My brave new code-signing world
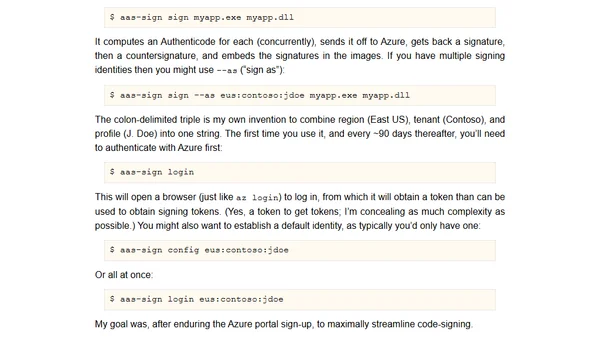
A developer details their journey setting up code-signing for Windows builds using Azure Artifact Signing and their own tool, aas-sign.
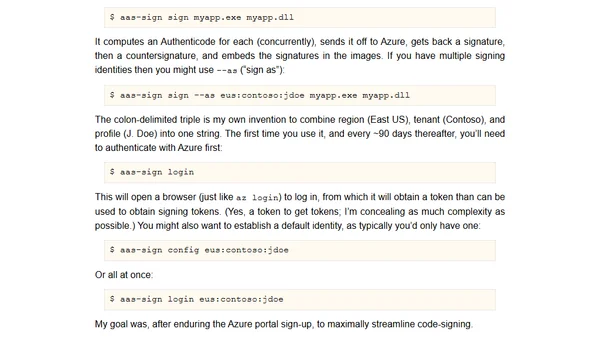
A developer details their journey setting up code-signing for Windows builds using Azure Artifact Signing and their own tool, aas-sign.
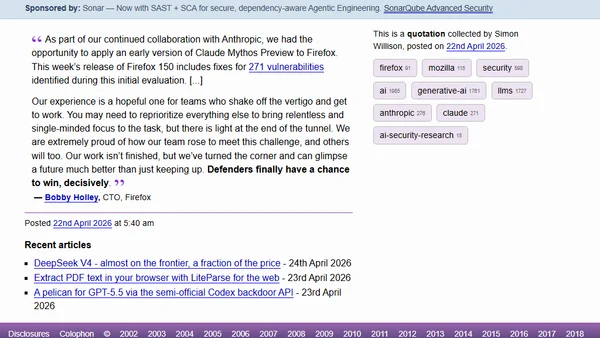
Firefox CTO discusses using Claude Mythos Preview to fix 271 vulnerabilities in Firefox 150, highlighting security improvements.
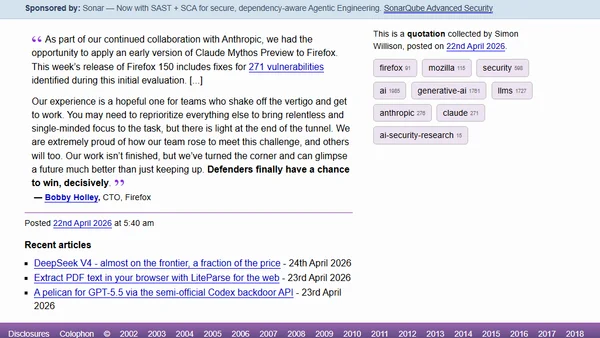
Firefox CTO discusses using Claude Mythos Preview to fix 271 vulnerabilities in Firefox 150, highlighting security improvements.
Announcing PyCon US 2026 in Long Beach with new AI and security tracks, plus community highlights.
Announcement of PyCon US 2026 in Long Beach with new AI and security tracks, including schedule highlights.
Martin Fowler shares podcast recommendations on programming trends and Uber's microservices, plus a detailed post-mortem on a supply chain compromise.
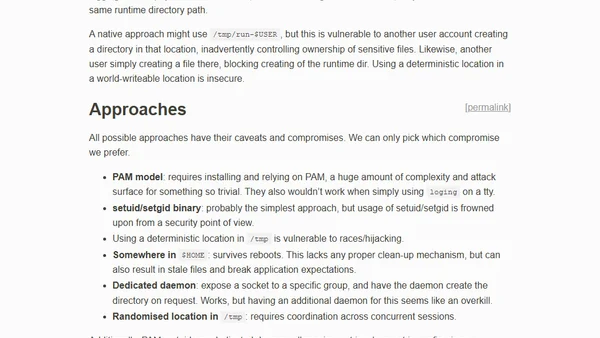
This article explores methods for creating an XDG_RUNTIME_DIR, comparing approaches like PAM, setuid binaries, and randomized locations in /tmp.

Overview of new Azure hybrid management and security updates, including Azure Arc, Defender for Cloud, and AI-driven tools for March 2026.
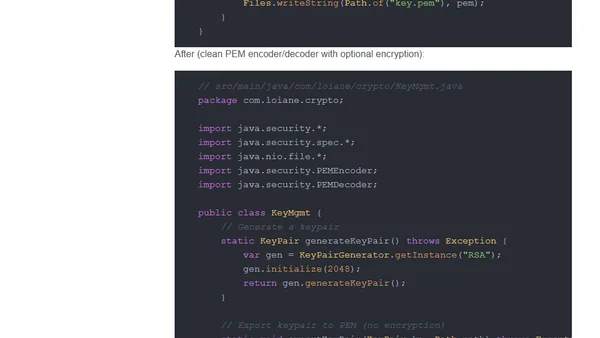
A hands-on tour of Java 26's new features for developers, covering pattern matching, concurrency, performance, and APIs.
Microsoft Authenticator will block work/school accounts on jailbroken or rooted devices starting in 2026, with a phased rollout.
Microsoft closes a security loophole in Azure ACS that allowed unauthenticated enumeration of tenant domains, hardening M365 against reconnaissance.
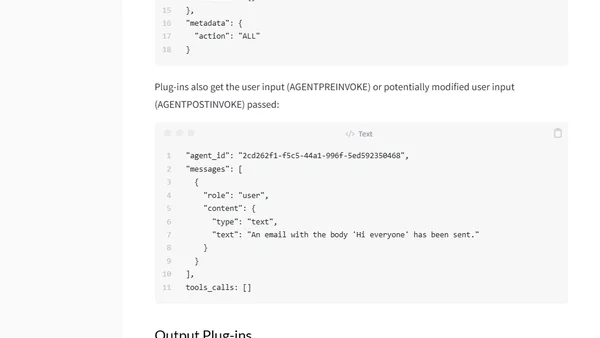
Explains how to use input and output plug-ins in IBM watsonx Orchestrate to enforce security, compliance, and safety guardrails for AI agents.
Microsoft releases a hands-on Sovereign Cloud MicroHack workshop for engineers to learn and implement technical controls for sovereign cloud architectures.

A developer's experience switching from 1Password to Apple Passwords, comparing features, performance, and ecosystem integration.
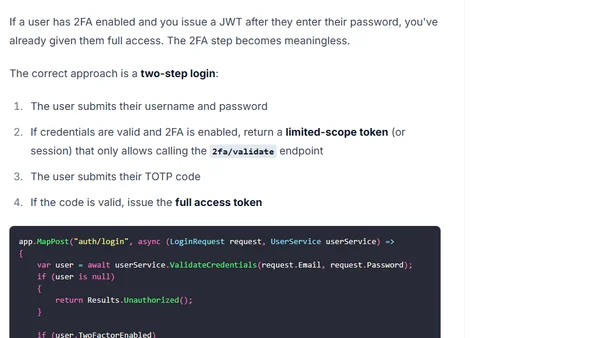
A technical guide on implementing Two-Factor Authentication (2FA) using TOTP and QR codes in ASP.NET Core for enhanced security.
A developer documents using Claude Code to audit and clean up overly permissive command permissions in a local settings file for better security.
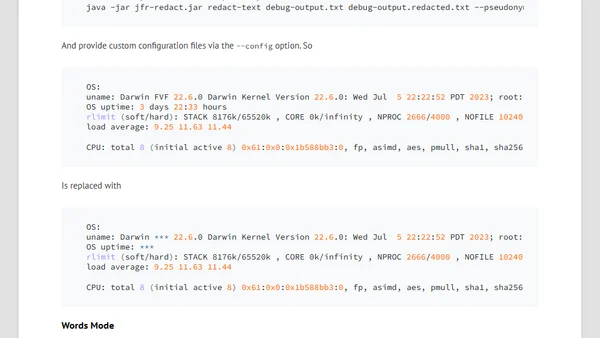
A guide to building a tool for redacting sensitive data like tokens and keys from Java Flight Recorder (JFR) and error log files.
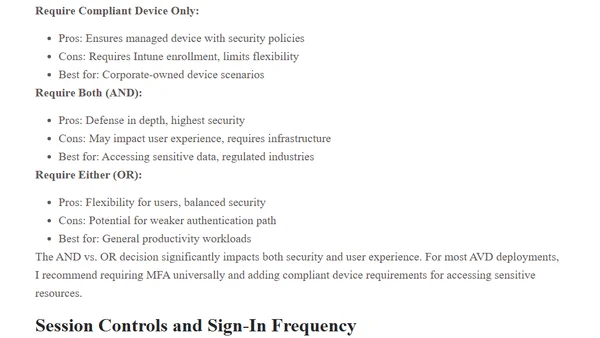
A guide to implementing Conditional Access policies for securing Azure Virtual Desktop, covering architecture, policy configuration, and best practices.
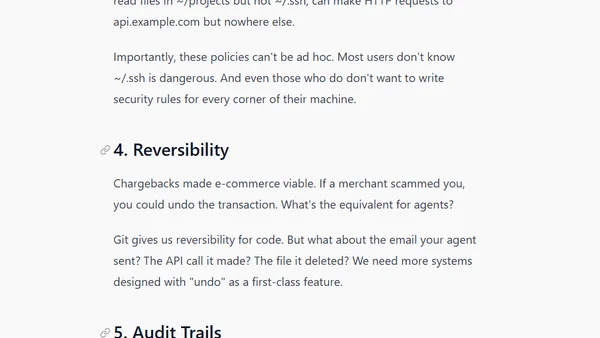
The article compares AI agent security to early e-commerce, arguing we need a multi-layered security stack (supply chain, prompt defense, sandboxing) to make agents trustworthy.
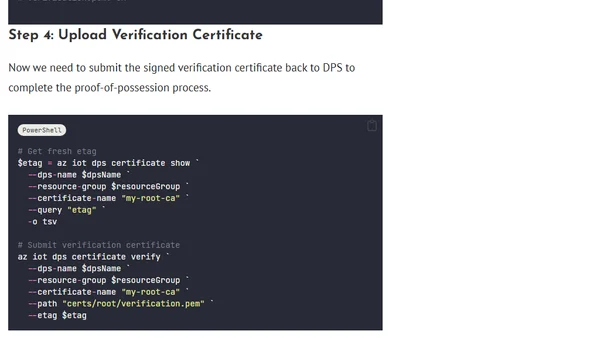
A technical guide on verifying X.509 certificate ownership for Azure IoT Device Provisioning Service using proof-of-possession.