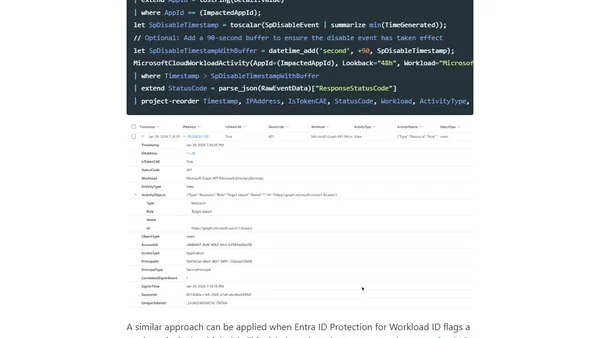
Analyzing Workload Identity Activity Through Token-Based Hunting
A technical guide on using KQL queries to hunt for suspicious activity and token theft targeting workload identities in Microsoft Entra.
Thomas Naunheim is a Cyber Security Architect and Microsoft MVP specializing in cloud-native identity and security solutions in Azure. He shares insights, session materials, and community contributions through his blog and Azure events.
10 articles from this blog
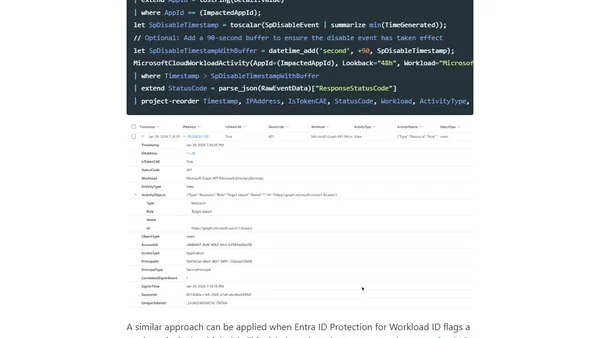
A technical guide on using KQL queries to hunt for suspicious activity and token theft targeting workload identities in Microsoft Entra.
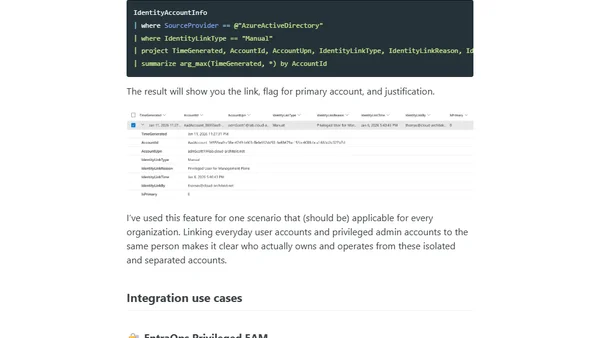
Explains how to link privileged accounts to user identities in Microsoft Defender for Identity to improve security visibility and incident response.
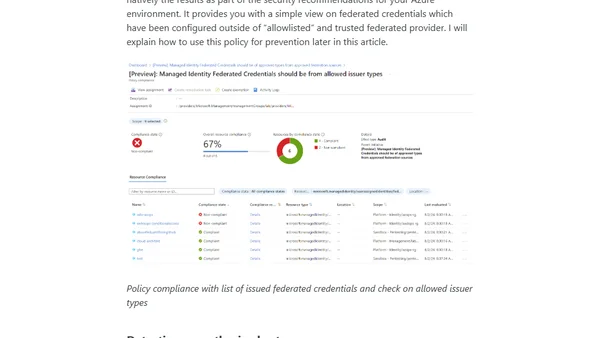
Explains security risks and attack scenarios for Managed Identities using Federated Credentials in Azure, focusing on privilege requirements and abuse prevention.
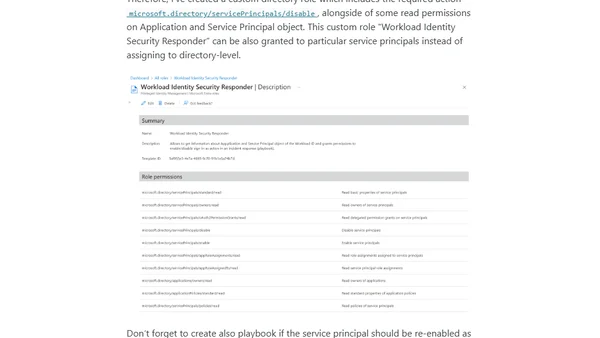
Explains how to use Microsoft Sentinel playbooks and Conditional Access to respond to security incidents involving compromised Microsoft Entra Workload Identities.
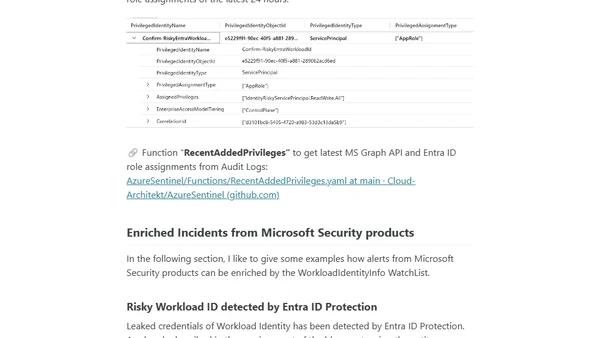
A guide on integrating Microsoft Entra Workload ID data into Microsoft Sentinel for advanced security monitoring and enrichment.
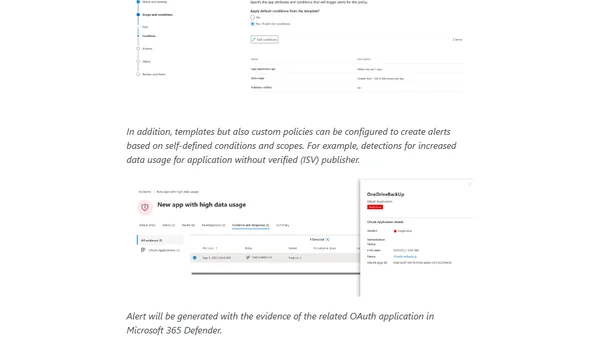
Explores threat detection for Microsoft Entra Workload IDs using Microsoft Defender XDR and Sentinel, focusing on attack paths and MITRE ATT&CK techniques.
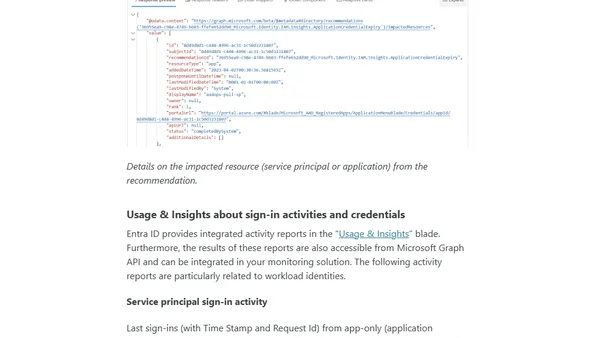
A technical guide on managing and monitoring Microsoft Entra Workload Identities, focusing on lifecycle management and security analysis.
Introduction to Microsoft Entra Workload ID, covering its features, premium capabilities, and common deployment scenarios for managing non-human identities.
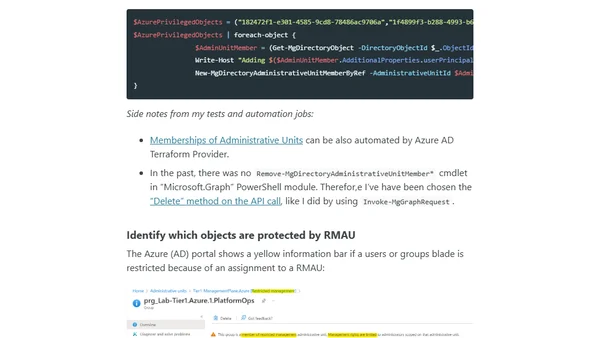
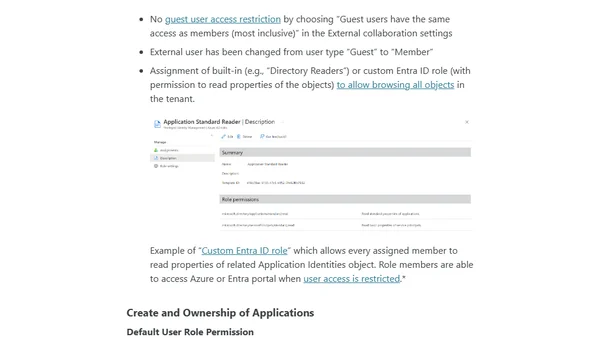
Explains Azure AD's Restricted Management Administrative Units (RMAUs) for securing privileged users and groups outside standard roles.
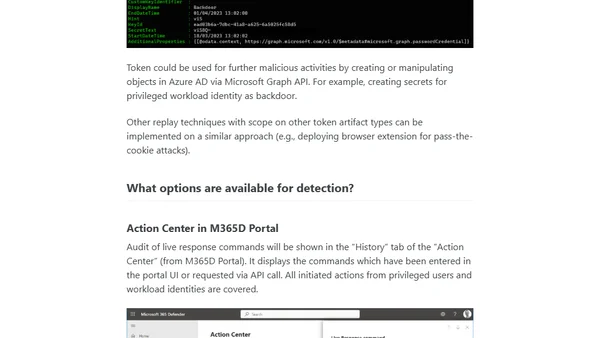
Analyzes the abuse of Microsoft 365 Defender's Live Response feature for privilege escalation on Tier0 assets and discusses detection methods.