Compressive Images Revisited
Revisits the 'compressive images' technique for responsive web design, analyzing its modern relevance, performance trade-offs, and memory impact.
Revisits the 'compressive images' technique for responsive web design, analyzing its modern relevance, performance trade-offs, and memory impact.

Introducing AstroImages.jl, a Julia package for visualizing astronomical images from FITS files.
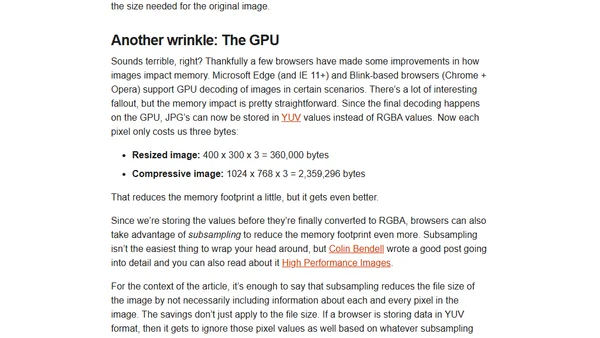
Second part of a series on building a Wayland compositor from scratch using wlroots, focusing on enabling client connections.
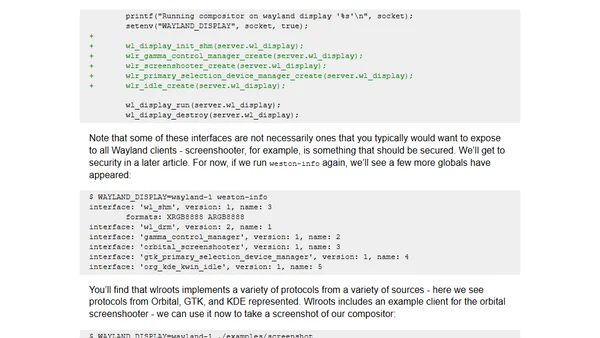
A technical guide on deploying a Docker Swarm cluster using Microsoft Azure and Azure Cloud Shell for hands-on learning from the Docker Deep Dive book.
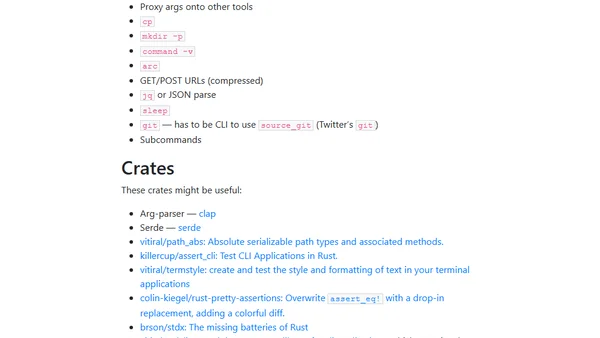
Exploring Rust for migrating complex CLI tools from Bash, covering requirements, useful crates, and considerations for adoption.
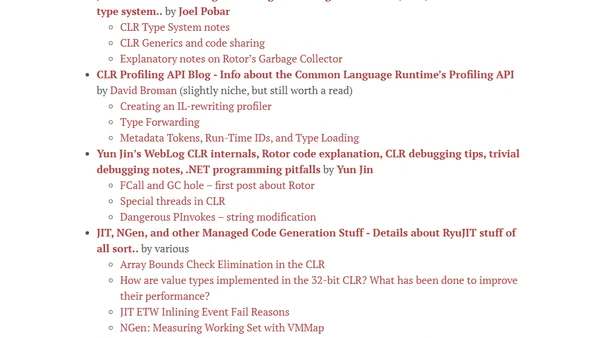
A curated list of blogs and resources for developers to learn about the low-level internals and performance of the .NET runtime and CLR.
Explores Rao-Scott tests for survey data analysis, comparing them to Wald tests and discussing new Satterthwaite-adjusted Wald tests in the survey package.
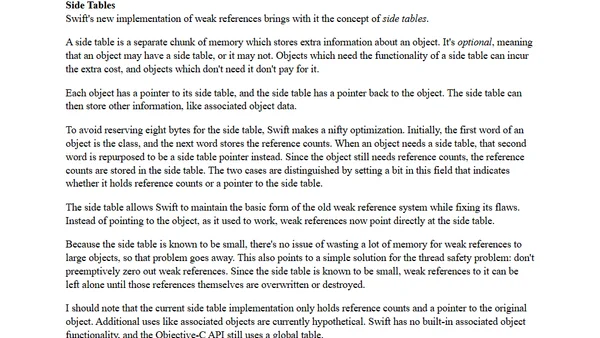
Explains the implementation details and changes to weak references in Swift 4, comparing the old and new runtime behavior.
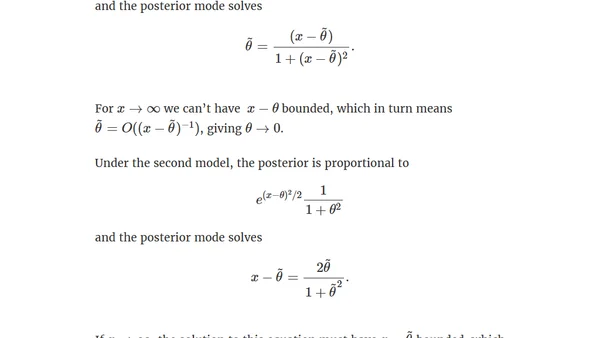
Explores Bayesian inference when data strongly contradicts prior expectations, analyzing how heavy-tailed priors and likelihoods affect posterior beliefs.
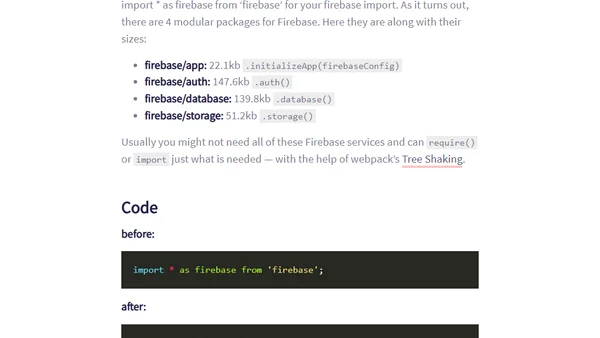
Explains how to reduce Firebase bundle size by 220kb using webpack's tree-shaking and modular imports.
A summary of Jeremy Keith's book on resilient web design principles, using web history to advocate for flexibility and progressive enhancement.
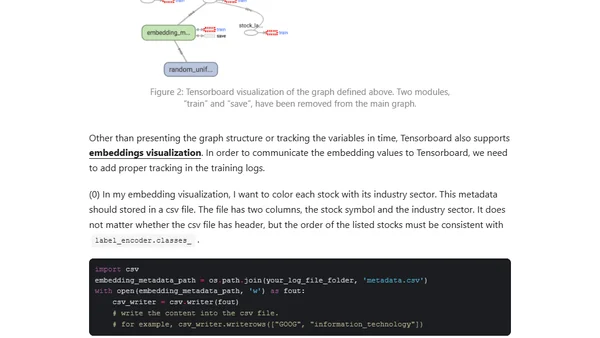
Part 2 of a tutorial on using RNNs with stock symbol embeddings to predict prices for multiple stocks.
Spring 2017 database news: SQL:2016 standard, cloud pricing wars, ACIDRain security study, and DB-Engines rankings.
Analysis of CVE-2016-10229, a serious Linux kernel vulnerability in MSG_PEEK, urging immediate updates for affected systems.
A tutorial on implementing a reusable custom loader/spinner as a service in an Angular 2 application using BehaviorSubject.
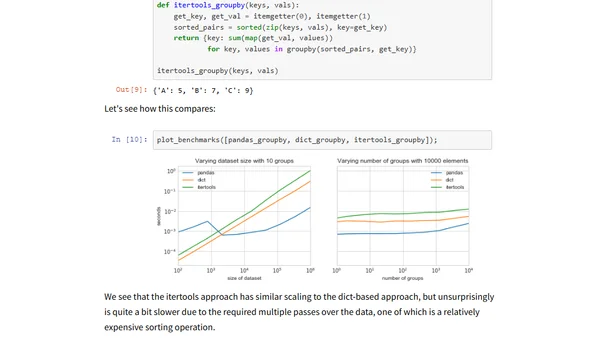
Explores implementing group-by operations from scratch in Python, comparing performance of Pandas, NumPy, and SciPy for data aggregation.
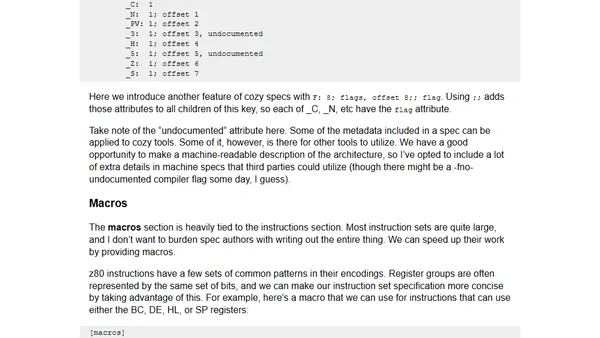
A developer introduces 'cozy', a long-term project to build a new C compiler toolchain with a focus on simplicity, portability, and a human-friendly machine specification format.
A technical guide on inviting external Microsoft Account users to a VSTS tenant secured by Azure Active Directory, covering admin and user steps.
A guide on contributing to open source projects by improving documentation, using a Node.js library example.
A guide to building great software products by absorbing complexity for users, focusing on core features, dogfooding, and optimizing for ideal use cases.