Matt Van Itallie - Sema software, generative ai and code analysis
Interview with Sema CEO Matt Van Itallie on using generative AI for code analysis, developer productivity, and explaining software to non-technical executives.
Interview with Sema CEO Matt Van Itallie on using generative AI for code analysis, developer productivity, and explaining software to non-technical executives.
A guide to selecting dispatchers in the SObjectizer actor model framework for C++, focusing on strategies for binding agents to threads.
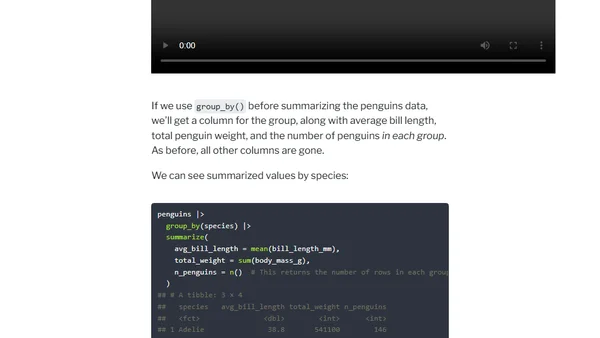
A tutorial using custom animations to visually explain how dplyr's mutate(), summarize(), group_by(), and ungroup() functions work in R.
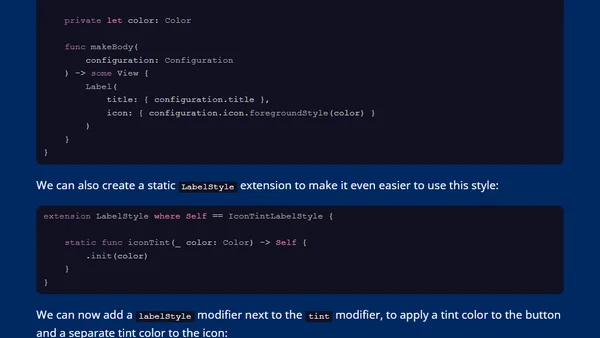
A SwiftUI tutorial on creating a custom LabelStyle to tint only the icon, leaving the text color unchanged.
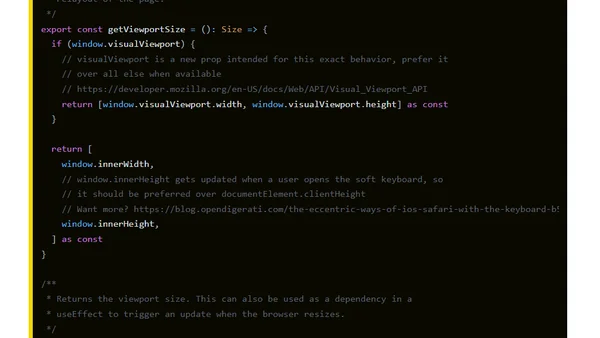
A technical guide on using the window.visualViewport API to accurately get the document height in iOS Safari when the on-screen keyboard is open.
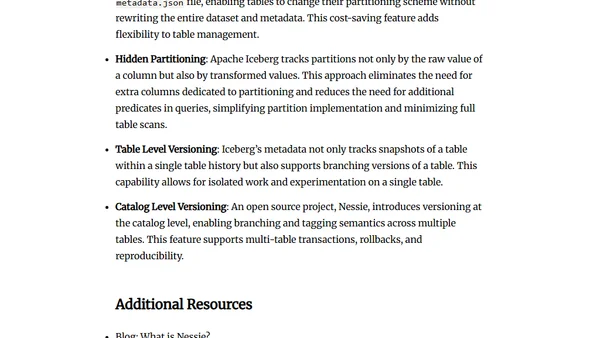
An introduction to Apache Iceberg, a table format for data lakehouses, explaining its architecture and providing learning resources.

Explores the evolution of Apache Iceberg catalogs, focusing on the current REST Catalog and future proposals for server-side optimizations.
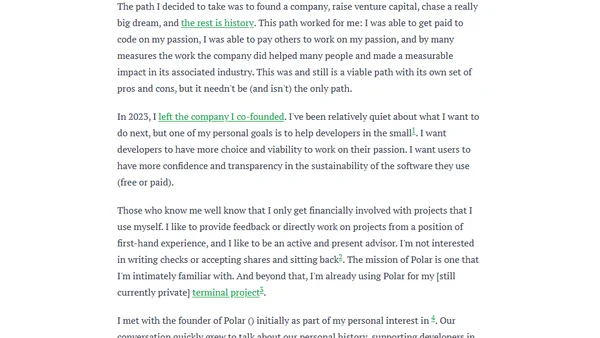
Mitchell Hashimoto joins Polar as an advisor to support its mission of helping developers get paid for working on their passion projects.
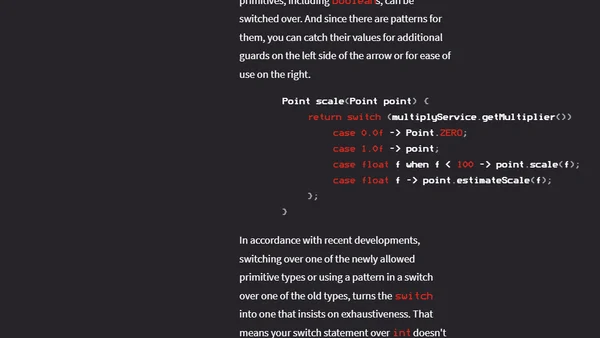
Explores Java 23's primitive patterns, detailing their role in rebalancing pattern matching alongside type, guarded, record, and unnamed patterns.
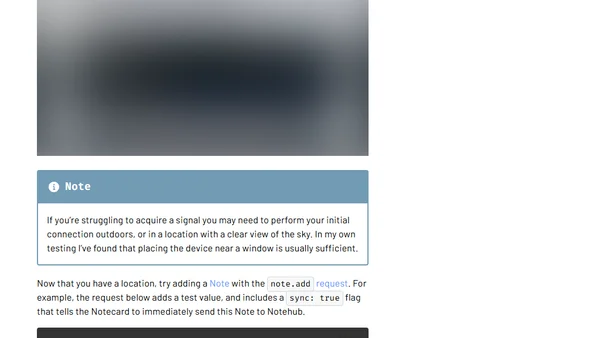
A guide on integrating an external GPS/GNSS module with the Notecard for continuous location streaming and cellular connectivity.
A tech manager outlines their ideal job criteria, focusing on management roles, fast-paced environments, remote work, and pragmatic technology use.
A developer adds flash messages and troubleshoots a content encoding issue with Django's 'timesince' in a SaaS project.
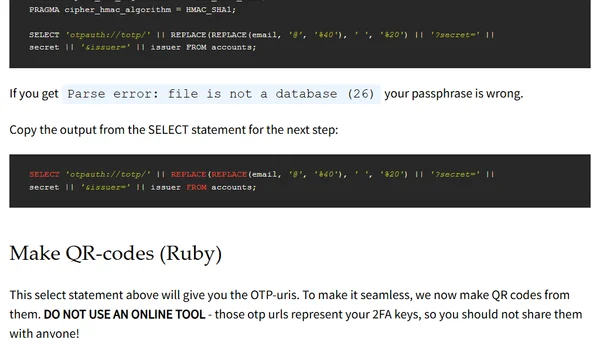
A technical guide on extracting 2FA secrets from the abandoned Authenticator Plus iOS app using SQLCipher and Ruby.
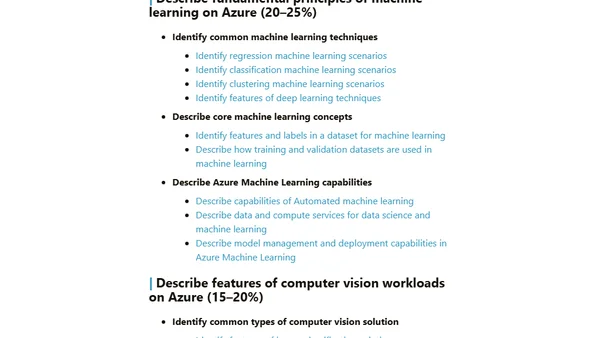
A study guide for the Microsoft AI-900 Azure AI Fundamentals exam, covering AI workloads, machine learning, and generative AI.
An introduction to NATS, an open-source technology for connecting applications and microservices over a network.
A critical analysis of whether test automation truly reduces stress and disruptions, or if it can initially increase workload and pressure on teams.
A web developer recounts a bug where moving a submit button outside its HTML form broke functionality, and how they fixed it using the form attribute.
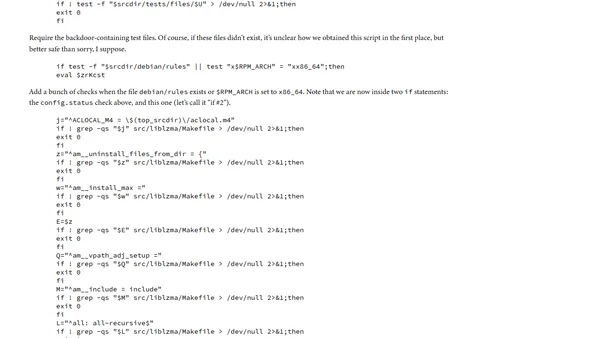
Analysis of the malicious shell script component in the xz backdoor attack, detailing its injection and execution mechanisms.
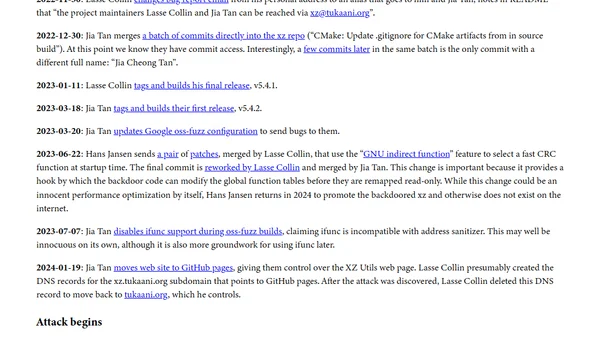
A detailed timeline of the multi-year social engineering attack that led to a backdoor in the xz compression library, a major open source supply chain incident.
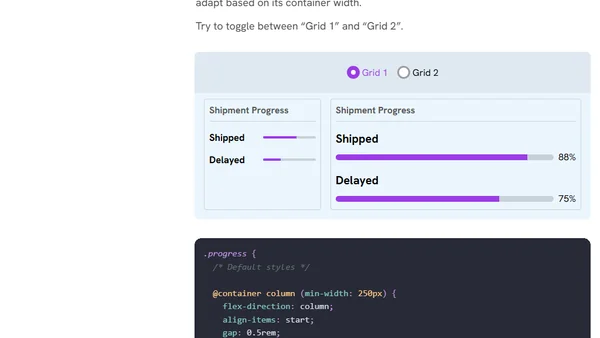
An interactive guide explaining CSS container queries, their purpose, and how to implement them for responsive component design.