Coding LLMs from the Ground Up: A Complete Course
A course teaching how to code Large Language Models (LLMs) from scratch to deeply understand their inner workings and fundamentals.
A course teaching how to code Large Language Models (LLMs) from scratch to deeply understand their inner workings and fundamentals.
A software engineer shares strategies for managing cognitive load and improving productivity through documentation, delegation, and focused task completion.
A course teaching how to code Large Language Models from scratch to deeply understand their inner workings, with practical video tutorials.
Critiques the limited scope of current customer support automation and argues for more ambitious AI solutions across industries.
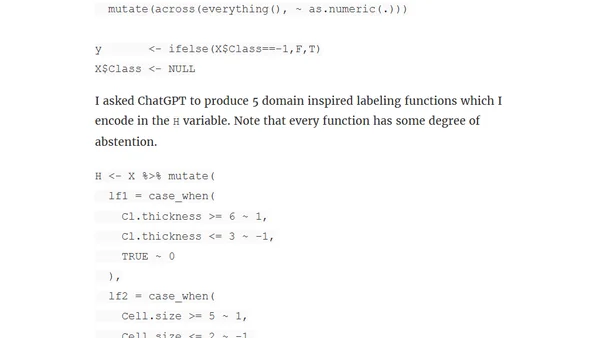
Explains the 'data programming' weak supervision paradigm for training models using noisy heuristic labels, with a practical example.
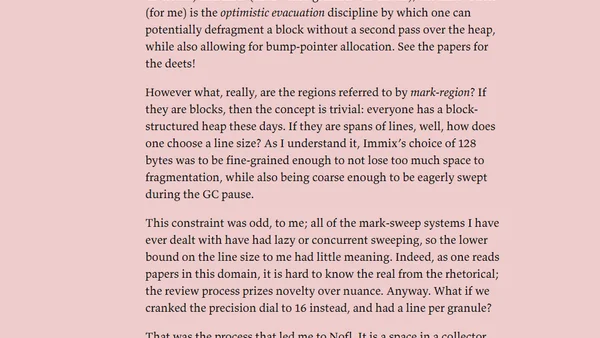
A developer's journey into garbage collection, detailing the creation of the Whippet GC and exploring Immix mark-region algorithms.
A developer's personal reflection on creating a Ruby gem inspired by another, the technical challenges faced, and the emotional journey of releasing imperfect work.
A developer argues that AI coding agents are not like junior developers but rather 'amnesiac spies' with vast knowledge but no memory or growth.
A tutorial on setting up a Java Spring Boot development environment on an Android phone using Termux and VSCode.
A developer explains his personal "policy of transience" in computing, detailing habits like disabling shell history and using temporary storage.

A developer explores ideas for improving linter developer experience, focusing on clarity, minimalism, and removing warnings.
A developer explores using AI tools like Grok within Neovim for Love2D game development, including enhancing a Pong clone and its particle system.
Summary of talks from the 2025 TLA+ Community Event, focusing on formal methods and model-guided fuzzing for distributed systems.

Compares two Kubernetes tools for integrating external secret managers: Secrets Store CSI Driver and External Secrets Operator.
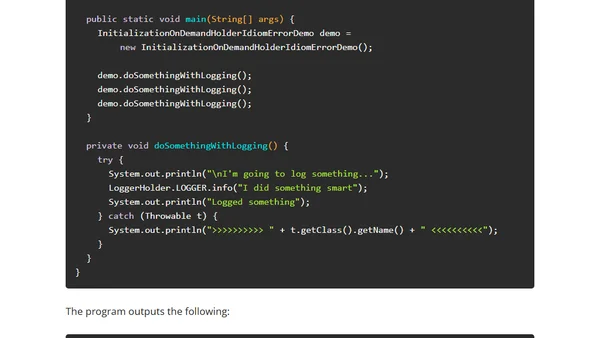
Explains the Initialization-on-Demand Holder idiom for lazy, thread-safe static initialization in Java, comparing it to alternatives.
Explains the Double-Checked Locking pattern in Java for thread-safe lazy initialization, covering its pitfalls and correct implementation.

Explores the security risks of self-replicating PHP code (quines), detailing how their underlying patterns can lead to vulnerabilities.
Introducing Ivar, a tool that provides Ruby developers with warnings for typos in instance variable names, preventing runtime errors.
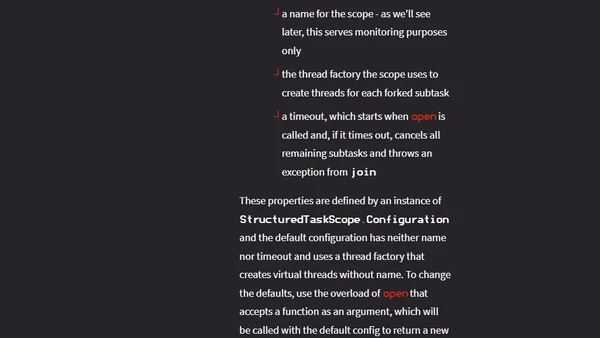
Overview of the revamped structured concurrency API in Java 25, a key feature for managing concurrent tasks with virtual threads.
Explains how React Server Components can be used to generate static sites, using a Next.js blog as an example.