Prevent clickjacking on Drupal and other Apache web applications
A guide to preventing clickjacking attacks on Drupal and Apache web applications by configuring the X-Frame-Options header.
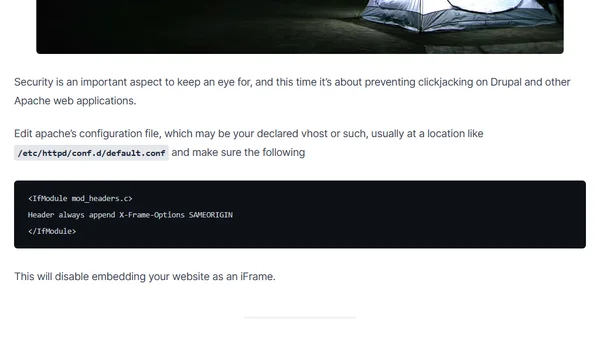
A guide to preventing clickjacking attacks on Drupal and Apache web applications by configuring the X-Frame-Options header.
A technical walkthrough on setting up and testing the Auditing feature in Azure SQL Database, including configuration and reporting.
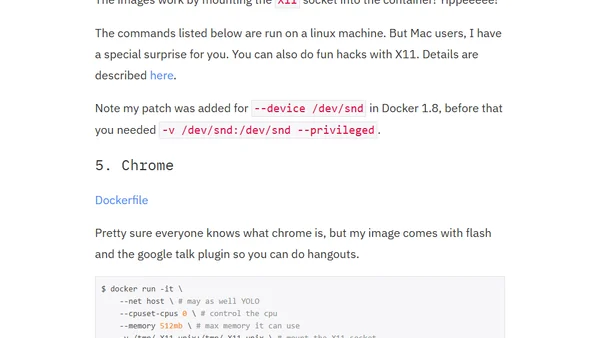
A guide on using Docker containers to run desktop applications like IRC clients and email, offering isolation and resource control.
A guide to securing the ASP.NET MVC Web.config file, covering custom errors, cookie security, and removing revealing HTTP headers.

A technical guide to achieving an A+ SSL/TLS rating on Qualys SSL Labs by configuring Nginx with specific protocols, ciphers, and security features.
A comprehensive guide to implementing favicons and related icons for modern websites, covering various devices and platforms with ASP.NET MVC examples.
An overview of ASP.NET Core Boilerplate, a professional template for building secure, fast, and SEO-friendly web applications with improvements over the default MVC template.
Essential security practices for freelance developers, covering device locking, password management, and multi-factor authentication.
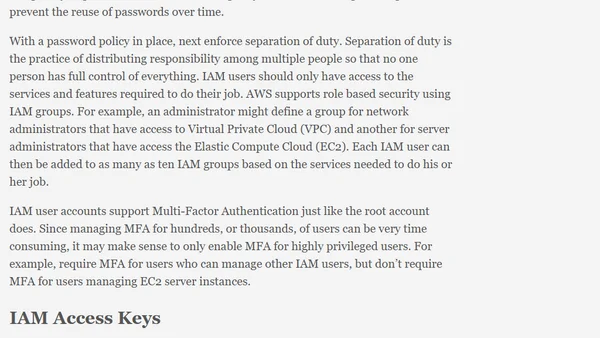
Explains AWS authentication options like root accounts and IAM users, focusing on security best practices and access control.
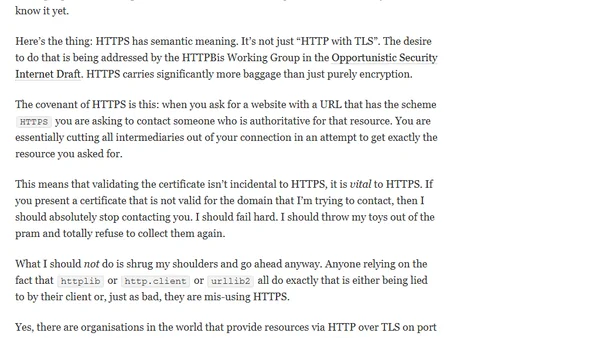
Argues that HTTPS requires certificate verification for security, discussing Python's debate on backporting this fix to version 2.7.
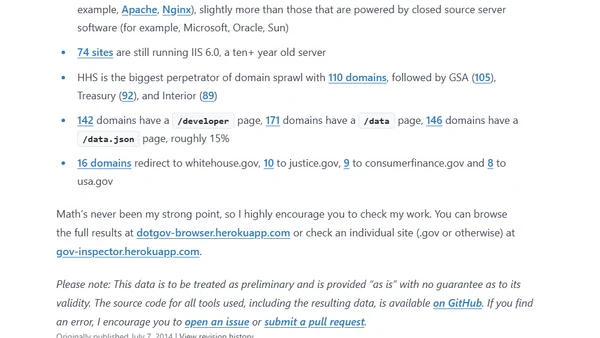
A follow-up analysis of U.S. federal .gov domains, tracking changes in technology, security, and accessibility over three years.
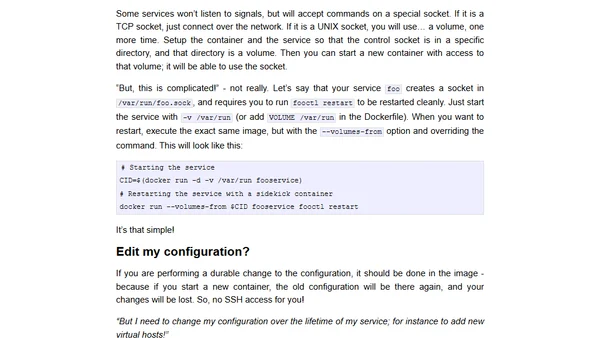
Explains why running SSH servers in Docker containers is bad practice and recommends better alternatives for debugging and management.
A reflection on the ethical responsibilities of open source maintainers, especially regarding security and user dependency, beyond the 'volunteer' excuse.

Explains new SQL Server 2014 permissions like IMPERSONATE ANY LOGIN and how they interact with CONTROL SERVER for security and privilege escalation.
A blogger clarifies that Skype's unencrypted local database is not a security vulnerability, as it's protected by system-level access controls.
A practical guide on the essential and non-essential elements for building a successful web application, emphasizing simplicity and core problem-solving.
A blog post explaining the Heartbleed OpenSSL vulnerability and providing Python scripts to test websites for it.
A technical talk on the challenges and proper implementation of TLS/SSL for secure communications, presented at multiple Python conferences.
A concise, urgent guide for sysadmins on the mandatory steps to fix the critical Heartbleed OpenSSL vulnerability and secure web servers.
Explains the April 7 web security vulnerability, its impact on major sites, and provides steps for users to protect their accounts.