Redacting sensitive information with Application Insights in C#
A guide to redacting sensitive PII data like email addresses from logs before they are sent to Azure Application Insights using C# and ITelemetryInitializer.
A guide to redacting sensitive PII data like email addresses from logs before they are sent to Azure Application Insights using C# and ITelemetryInitializer.
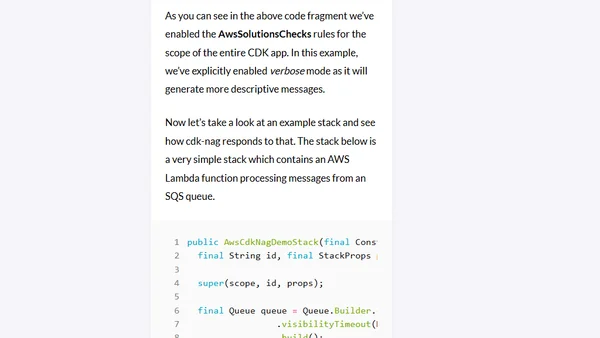
Introduces cdk-nag, an open-source tool for automated security and compliance checks in AWS CDK infrastructure-as-code projects.
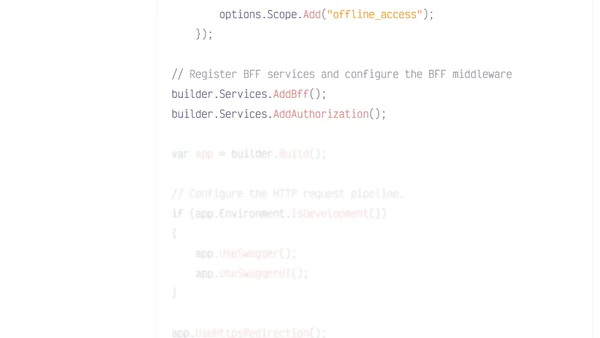
A guide to implementing a Backend for Frontend (BFF) architecture with .NET, Duende, and Auth0 to enhance SPA security by moving token handling server-side.
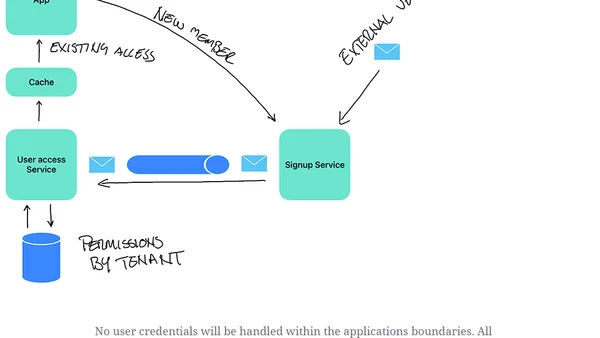
Explores a multi-tenancy security design pattern: external authentication with local authorization, using IDP tokens and SAGA for signup.
An overview of Django's built-in session management system, explaining its security features and how to configure them for robust user data protection.
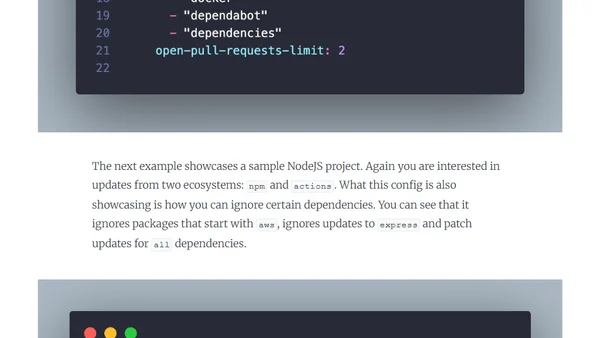
A guide on implementing Dependabot for automated dependency updates and vulnerability management to improve software supply chain security.

A developer shares their journey creating an open source activism program to teach collaboration and inclusivity in software development.
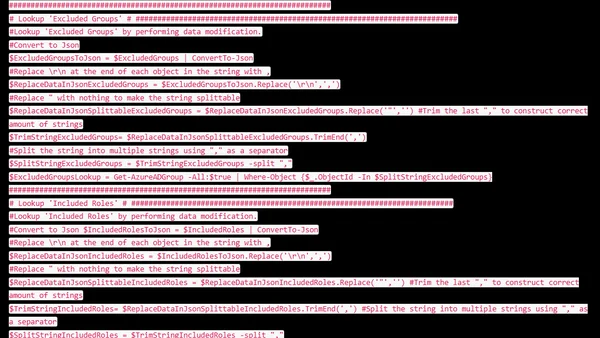
A guide to exporting Azure AD Conditional Access policies using PowerShell, focusing on retrieving readable object names instead of just IDs.
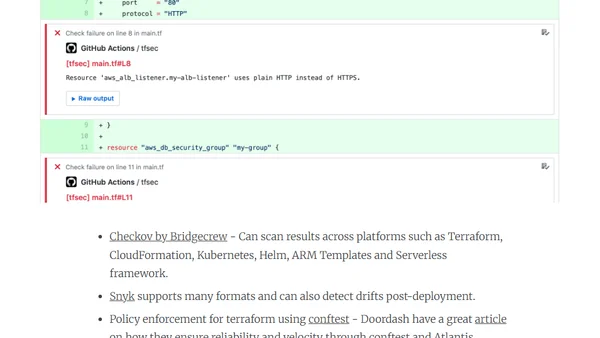
Explains the 'shift left' approach to integrating security early in the DevOps software development lifecycle for better outcomes.
A talk on implementing flexible, permission-based authorization in ASP.NET Core to overcome limitations of traditional role/claim-based systems.
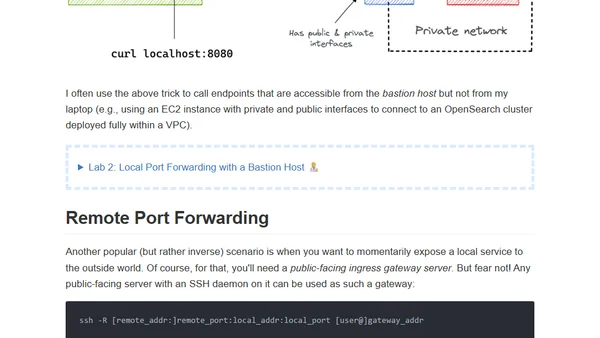
A visual guide and hands-on labs explaining SSH tunnels, focusing on local and remote port forwarding for developers.
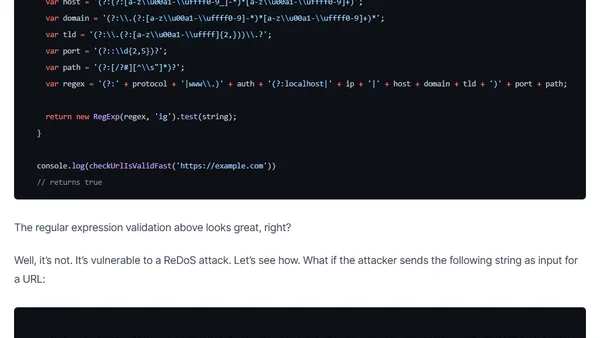
Explains why using RegEx for URL validation in JavaScript can introduce security vulnerabilities like ReDoS attacks, and recommends safer alternatives.
An overview of core cryptography concepts and their implementation in Python, based on a presentation by Andrew Sillers.
VMware vSphere 6.5 and 6.7 reach end of general support, urging users to upgrade for security and updates.
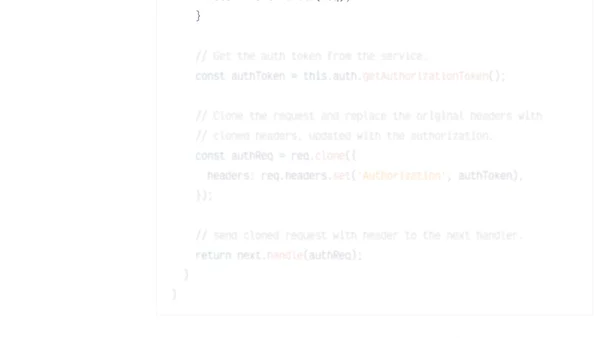
Discusses security risks in Angular HTTP interceptors, especially when exposing authentication tokens, and provides examples from common implementations.
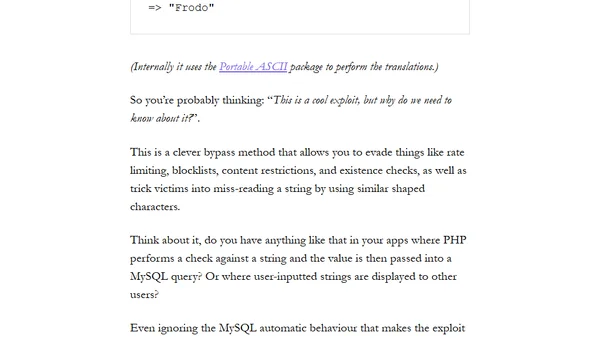
Explains how Unicode transliteration can bypass security measures like rate limiting in Laravel apps and how to fix it.
Announcing django-denied, a Django package that enforces authorization by denying all views by default for enhanced security.
A Laravel security tip on using Git's selective staging (git add -p) to review code before committing, preventing secrets or debug code from being pushed.
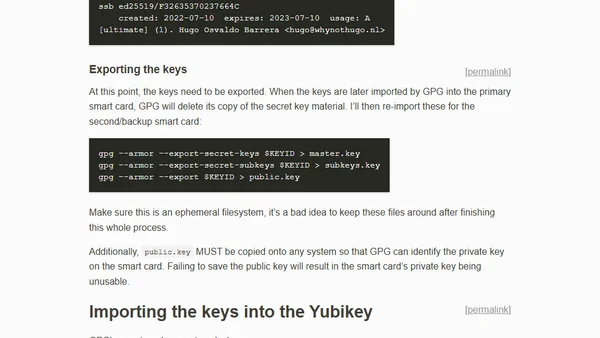
A technical guide on setting up and using a Yubikey hardware token for GPG encryption and signing, covering key generation and smart card configuration.
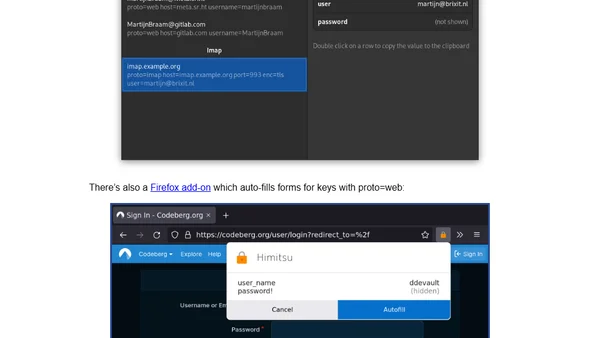
Introducing Himitsu, a new Unix key/value store and protocol for managing secrets like passwords and SSH keys, with a focus on extensibility and user consent.