DevOps Links for 15/10/2021
A roundup of DevOps news and tools, including GitHub Releases beta, npm security updates, composite actions, and container vulnerability scanning.
A roundup of DevOps news and tools, including GitHub Releases beta, npm security updates, composite actions, and container vulnerability scanning.
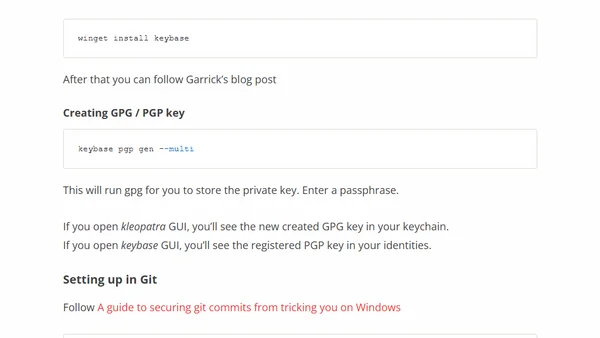
A step-by-step guide to setting up signed Git commits using Keybase and GPG on Windows 10, including installation and configuration.
A quick guide to manually patching the OMIGOD vulnerability in Azure-hosted Linux VMs by updating the OMI package.
Explains disk encryption basics for non-technical users, covering why it's needed, how it works, and different implementation types.
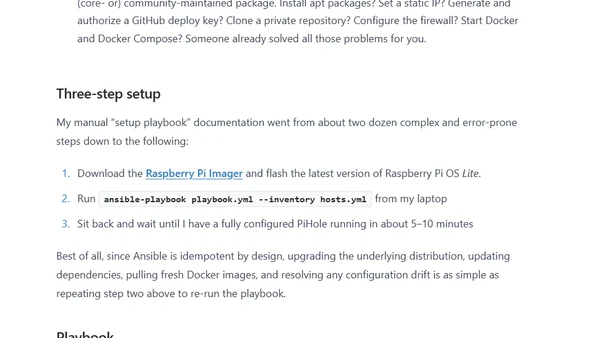
A developer details their journey to further automate and secure their home network using Docker, Ansible, and AdGuard Home.
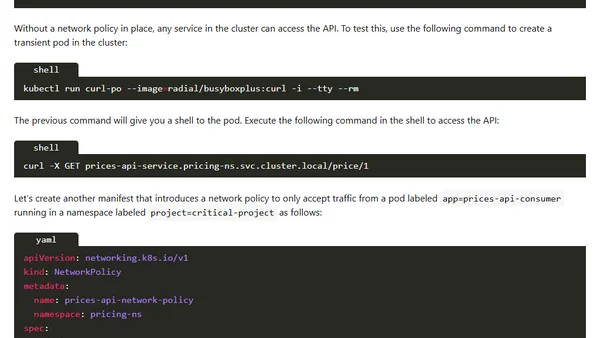
Explains how to use Kubernetes Network Policies to restrict communication between microservices for improved security.
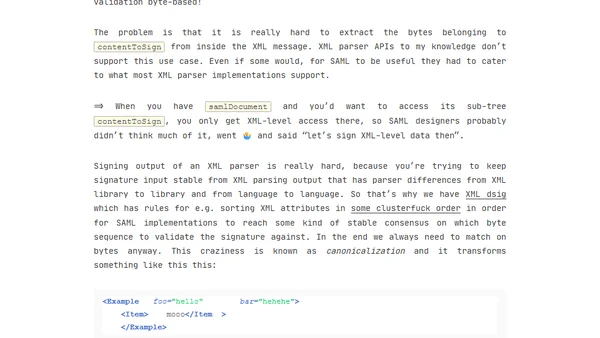
A critical analysis of SAML security, arguing its design is inherently insecure due to malleable signature computation, with examples of real-world vulnerabilities.
A beginner-friendly introduction to JSON Web Tokens (JWT), explaining their structure, use for stateless authentication, and basic flow.
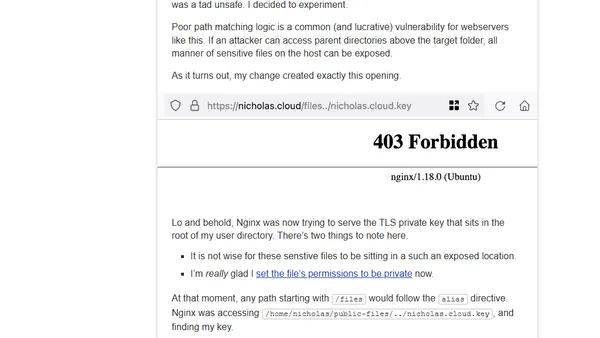
A developer's cautionary tale about a security vulnerability introduced by a seemingly minor change to an Nginx alias directive configuration.
Critique of npm audit's flaws, arguing its default rollout was rushed and harmful to front-end development workflows.
Explores the benefits and security advantages of using Generation 2 virtual machines in Azure, focusing on the upcoming Trusted Launch feature.
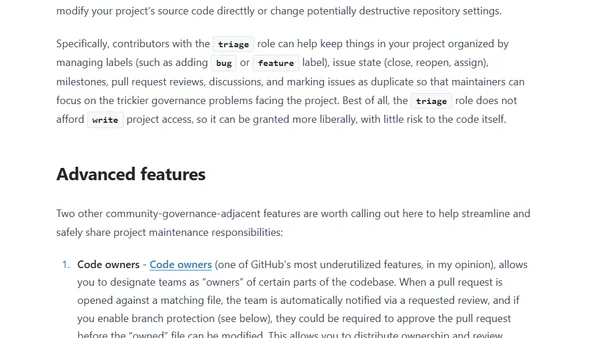
Practical advice for establishing and operationalizing governance in mature open source projects, covering ownership, security, and contributor roles.
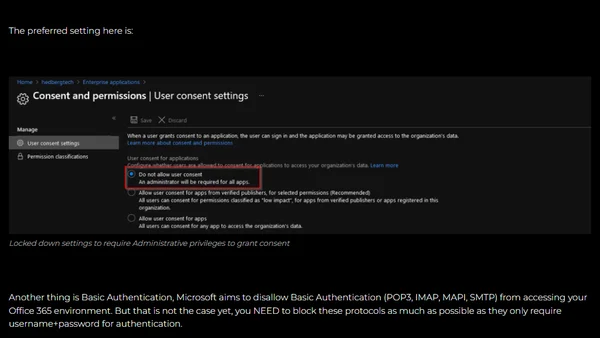
A security-focused guide listing eight critical areas to monitor and secure in Azure Active Directory to prevent breaches.
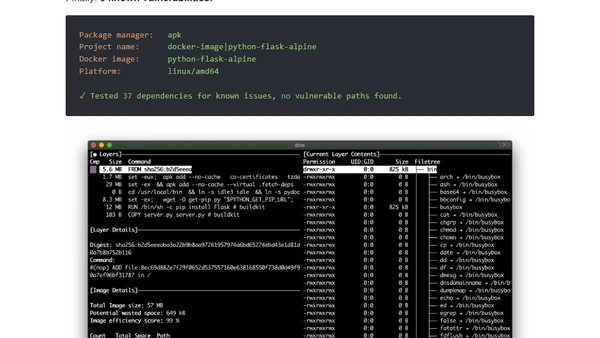
Discusses the importance of using smaller, secure container images, analyzing vulnerability scans and trade-offs between Alpine and Debian-based images.
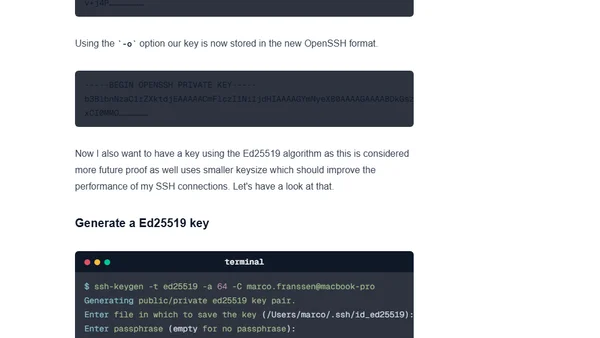
A technical guide comparing SSH key algorithms (RSA, ECDSA, Ed25519) and providing recommendations for generating secure keys in a DevOps context.
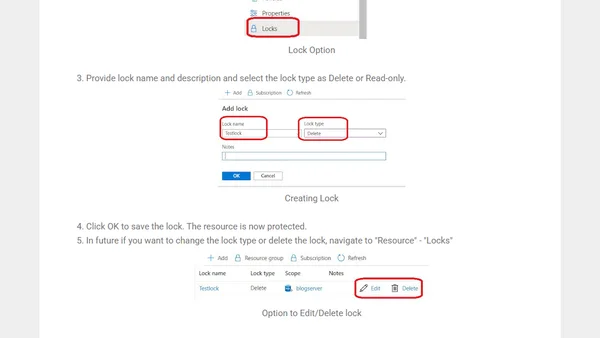
Explains Azure Resource Locks, their types (CanNotDelete/ReadOnly), and how to apply them via the Azure Portal to prevent accidental deletion or modification.
A developer argues that cryptocurrency has caused widespread abuse of free CI services and damaged trust in the software industry.
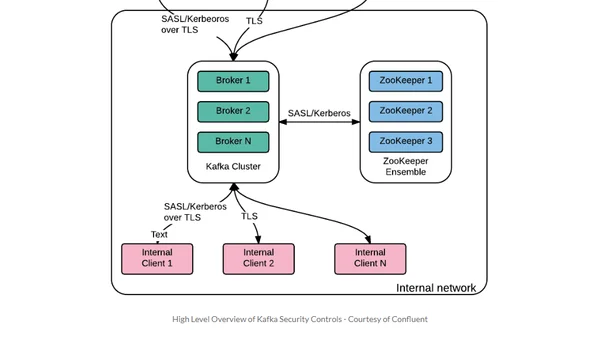
A guide for security professionals to understand Apache Kafka basics and its security features within the Kubernetes ecosystem.
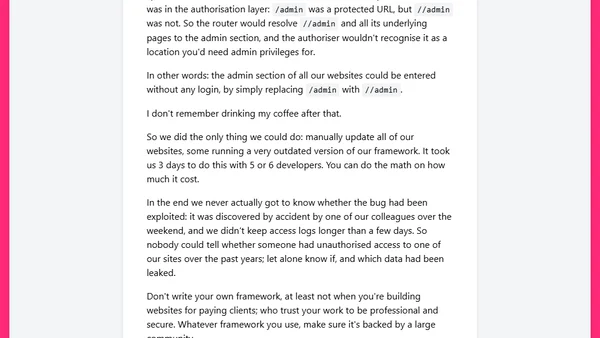
A developer recounts a critical security bug in a custom-built framework, arguing against writing your own framework for client projects.
A guide to debugging GitHub Actions secrets by revealing them in logs using a sed command, with a security warning.