Why “We Encrypt at Rest” Is No Longer Enough
Explains why traditional database encryption is insufficient in 2026, highlighting new threats and the need for advanced data-in-use protection.
Explains why traditional database encryption is insufficient in 2026, highlighting new threats and the need for advanced data-in-use protection.

A technical guide on enforcing TLS 1.2 and trusted certificates for SQL Server connections to secure data in transit, covering FedRAMP compliance.
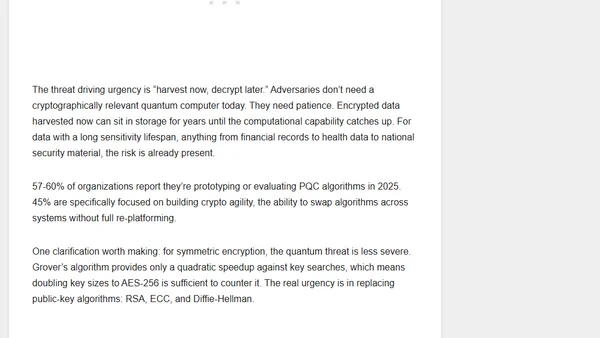
Explores the 'law of large data breaches,' a hypothesis that all online data subsets are eventually breached, relating it to probability and data as a toxic asset.
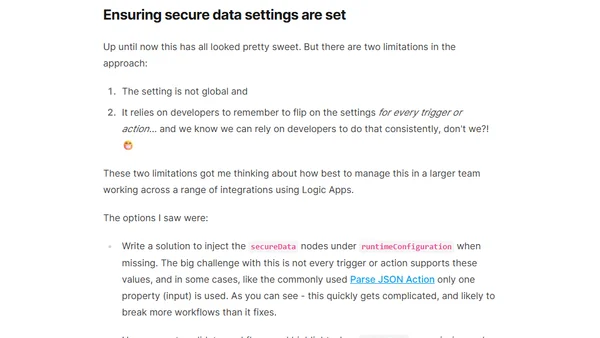
Explains how to use Azure Logic Apps' built-in input/output obfuscation to secure data in operational logging and how to validate the settings.

Explores privacy risks, bias, dependence, misinformation, and manipulation dangers associated with conversational AI and chatbots.
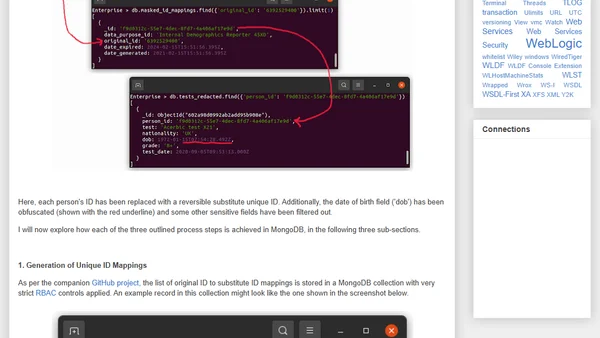
Explains how to implement reversible data masking in MongoDB using an idempotent pattern to protect sensitive data while enabling authorized recovery.
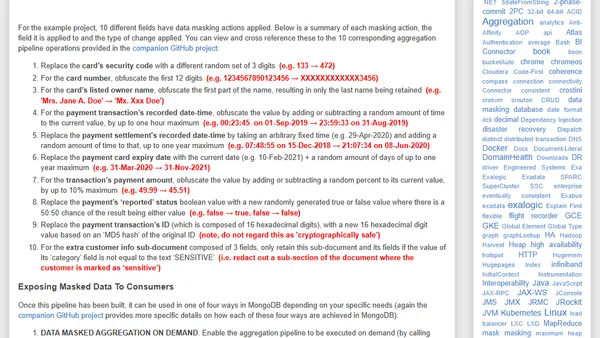
Explores how to use MongoDB aggregation pipelines to mask sensitive data for testing and API access, with practical examples.
The article critiques the use of SSNs as both a secret and a universal ID, arguing it's a core problem behind data breaches like Equifax.
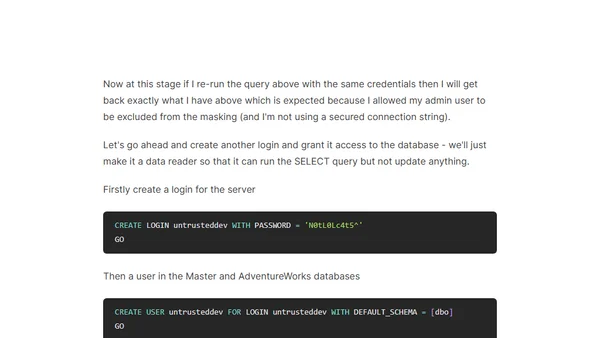
A technical walkthrough on setting up and using the Dynamic Data Masking feature in Azure SQL Database for on-the-fly data obfuscation.
Analyzes the TV show Continuum to discuss real-world surveillance, IoT security risks, and the erosion of privacy in a connected world.
An article explaining cryptography and data security concepts, including a notable section on steganography.
Explores the legal and privacy implications of law enforcement's expanding digital wiretapping authority in the era of cloud computing.
Explains why Twitter is important for businesses, enterprises, power users, and consumers as a communication and feedback tool.
A user attempts to clean a hard drive with soapy water, but data remains recoverable. The article explains why physical destruction is necessary.