Building a Homelab VM Server
A guide to building a dedicated homelab server for running development VMs, covering the benefits of isolation and hardware selection.
A guide to building a dedicated homelab server for running development VMs, covering the benefits of isolation and hardware selection.
Explains why forward secrecy is crucial for modern encryption, contrasting GPG's long-term key model with the Signal Protocol's ephemeral keys.
A developer tracks HTTP vs HTTPS requests for a year, highlighting major websites still using insecure HTTP and advocating for HTTPS adoption.
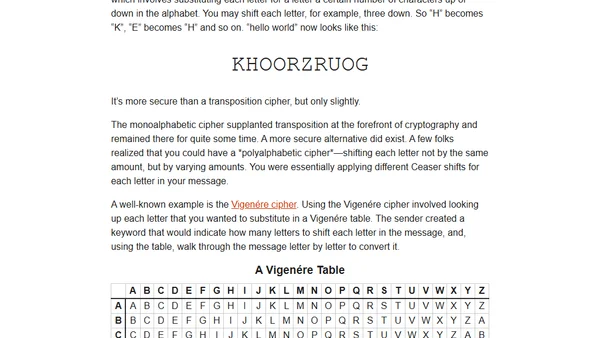
A reflection on teaching basic cryptography to children, highlighting the importance of usable security through historical ciphers like the rail fence and Caesar cipher.
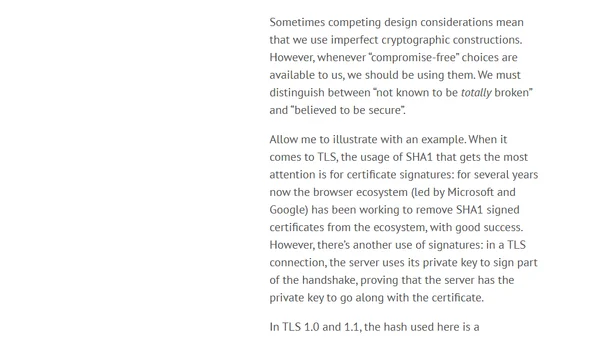
Discusses the importance of cryptographic safety factors, using SHA1's vulnerabilities and Feynman's Challenger report as analogies.
A guide on protecting API keys in Python applications by storing them in a separate config file and using .gitignore to prevent exposure on GitHub.

A guide to implementing HTTP Public Key Pinning (HPKP) for enhanced security in ASP.NET Core applications, covering benefits and risks.
Explains how to implement HTTP Strict Transport Security (HSTS) in ASP.NET Core to enforce secure HTTPS connections.

A tutorial on creating custom middleware in ASP.NET Core to automatically redirect HTTP requests to HTTPS for improved security.
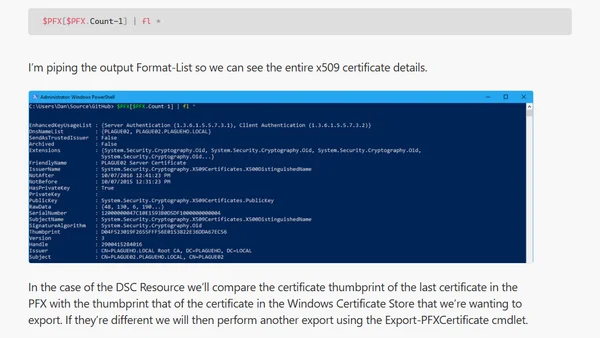
A technical guide on using PowerShell to read, analyze, and validate certificates within PFX files, including trust chain inspection.
Explains why protocol-relative URLs (//example.com) are harmful for security and compatibility, advocating for absolute HTTPS URLs instead.
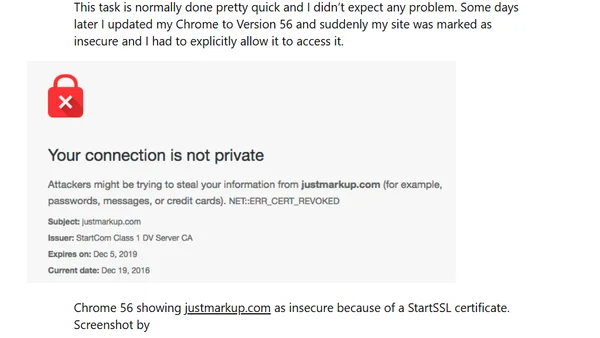
Urgent warning to replace StartCom or WoSign SSL certificates before Chrome 56 and Firefox 51 mark sites as insecure in early 2017.
Explores the $500 security guarantee for finding vulnerabilities in qmail, highlighting principles for secure open-source software development.
A developer's initial experience using Google's OSS-Fuzz project to perform large-scale fuzz testing on the open-source libyaml library.
A developer creates a Chrome extension and Android app for generating secure, service-specific passwords from a master passphrase, inspired by existing tools.
A guide to using an AWS CloudFormation template for standardizing the configuration of new linked accounts, including security and administrative roles.
Argues that web browsers should actively warn against and eventually block performance-harming and inaccessible web development practices.
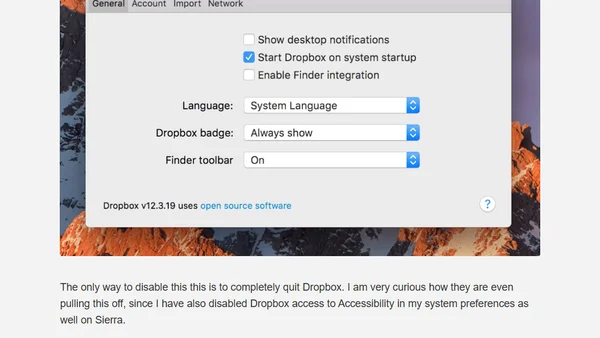
Dropbox's latest update adds a non-removable Finder toolbar, sparking criticism for poor UX and ignoring user control.
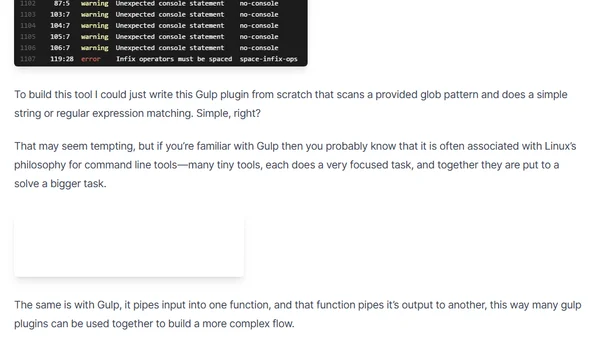
A developer explains building a security-focused static code analysis tool for Gulp by extending an existing plugin, following open source philosophy.
An introduction to threat modeling, a security technique for identifying assets, attack vectors, and attackers to build better system defenses.