Prior Probability in Logistic Regression
Explains how prior probabilities are learned and updated in logistic regression models, using a coffee brewing example to illustrate class imbalance.
Explains how prior probabilities are learned and updated in logistic regression models, using a coffee brewing example to illustrate class imbalance.
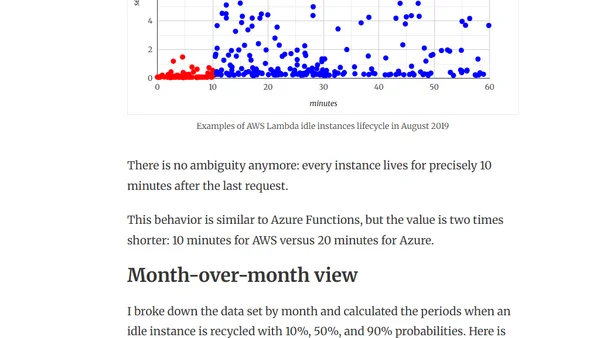
Analysis of AWS Lambda cold start behavior, revealing idle instances are now recycled after ~10 minutes, impacting serverless performance.

Announcement for SQLSaturday Lisbon 2019 and Porto 2019, including dates, call for speakers, and workshop topics.
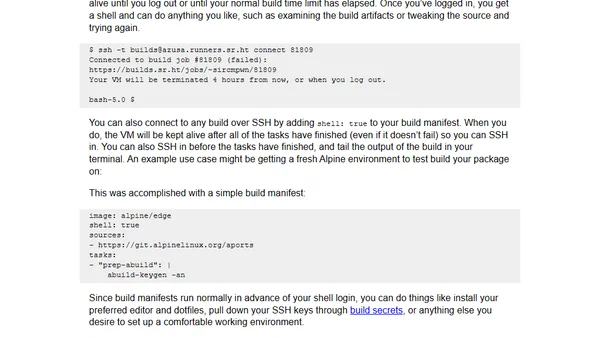
Sourcehut's builds.sr.ht CI now offers SSH access to build environments for debugging and interactive testing.
Essential npm security best practices to protect against malicious packages, including ignoring run-scripts and vetting third-party modules.
Explains how to change the default binding mode for XAML bindings using the x:DefaultBindMode attribute in UWP development.
Explores the practical uses of reversible computing, from automatic differentiation in deep learning to distributed systems and database operations.
Explores SQL Server 2019's new 'Feature Restrictions' security feature, designed to help prevent SQL injection attacks.

Traces the evolution of enterprise middleware from the 1990s to today, drawing parallels to modern enterprise blockchain solutions.
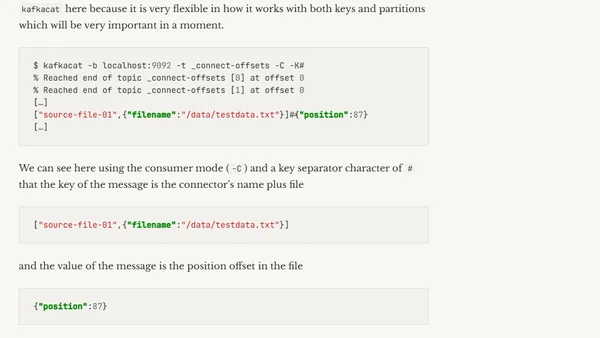
A guide to resetting offsets for Kafka Connect source connectors by modifying data in the Kafka offset topic, using tools like kafkacat.
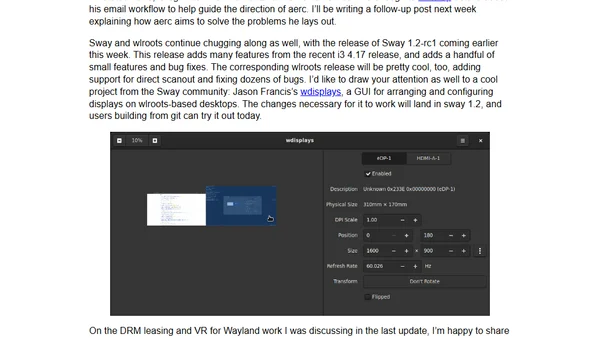
Developer shares updates on SourceHut, aerc email client, Sway/Wayland, and VR support for Linux, from Osaka.
A developer shares how solving coding puzzles on Advent of Code helps practice algorithms, learn Python, and improve problem-solving skills.
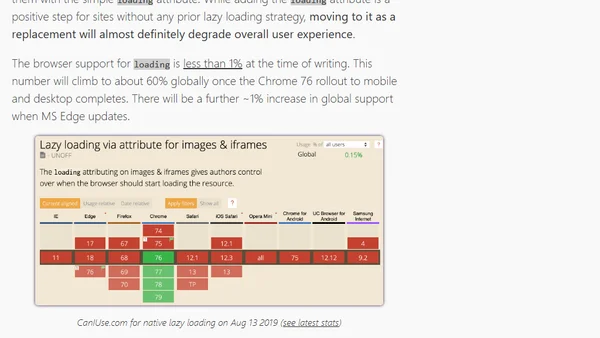
Discusses Chrome's new native lazy loading for images, its current limitations, and why developers should be cautious about adopting it immediately.
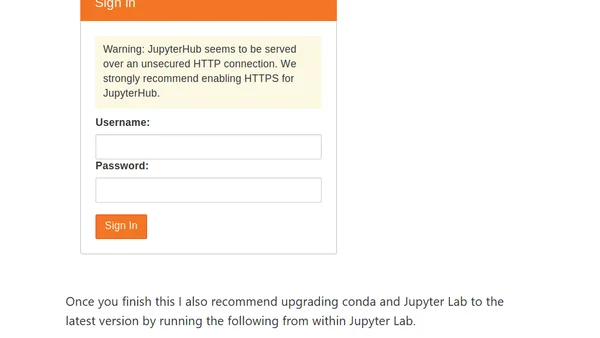
A guide to setting up a GPU-powered JupyterHub environment on AWS for a data science hackathon, including driver installation and configuration.

Performance analysis of SQL Server 2019's Batch Execution Mode on TPC-H queries using rowstore indexes and compressed data.
Explains memory unsafety in programming languages, its security risks (out-of-bounds reads/writes, use-after-free), and contrasts unsafe languages like C/C++ with safe ones.
Explains the theory behind linear regression models, a fundamental machine learning algorithm for predicting continuous numerical values.
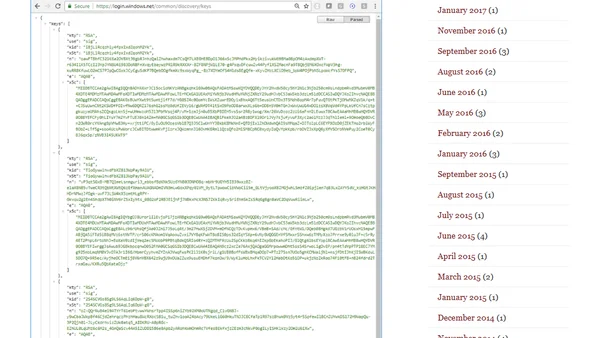
Explains the process and importance of rotating signing keys in IdentityServer for security, detailing the use of AddSigningCredential and AddValidationKey.
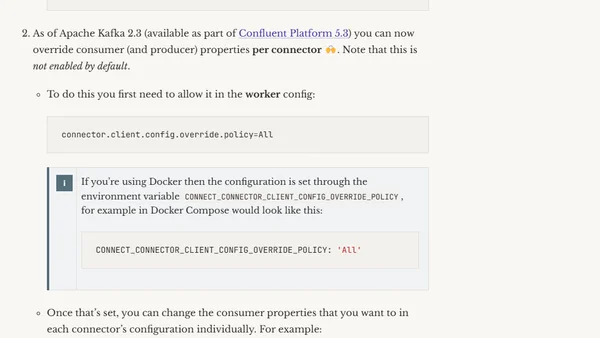
How to configure a Kafka Connect sink connector to start reading from the end of a topic instead of the beginning.
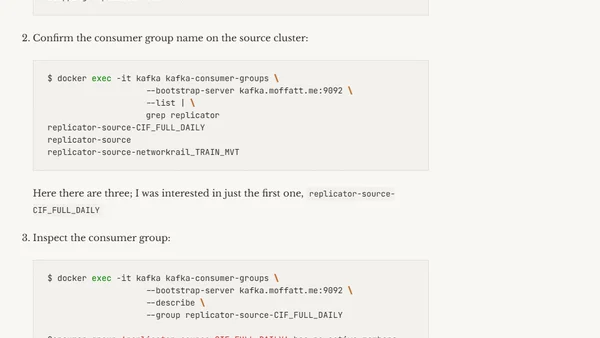
A guide on troubleshooting and resetting Kafka consumer group offsets when using Replicator to copy data between clusters.