The Complete List of OAuth 2 Grants
A comprehensive guide to all OAuth 2.0 grant types, explaining their flows and use cases for secure application authorization.
A comprehensive guide to all OAuth 2.0 grant types, explaining their flows and use cases for secure application authorization.
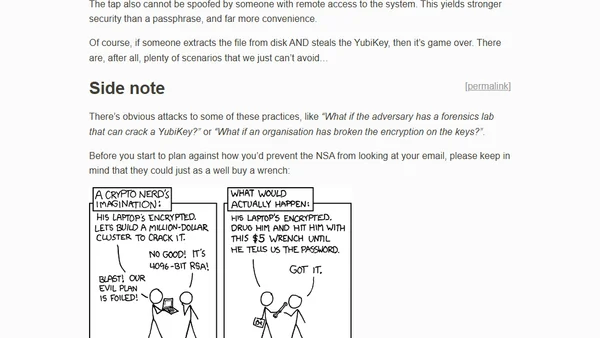
A developer shares practical tips and warnings for using YubiKeys for 2FA, SSH authentication, and sudo prompts to enhance security.
Explains why Azure AD's 'Nudge' campaign fails to prompt users to register the Microsoft Authenticator app, often due to conflicting Conditional Access policies.
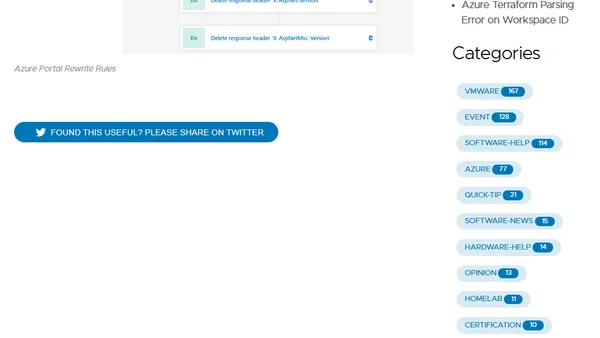
A PowerShell guide to increase security by removing unwanted HTTP response headers from an Azure Application Gateway using rewrite rules.
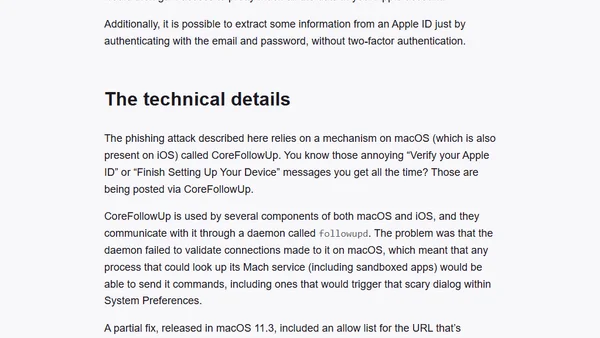
A macOS bug allowed malicious apps to spoof Apple ID verification alerts within System Preferences, enabling sophisticated phishing attacks.
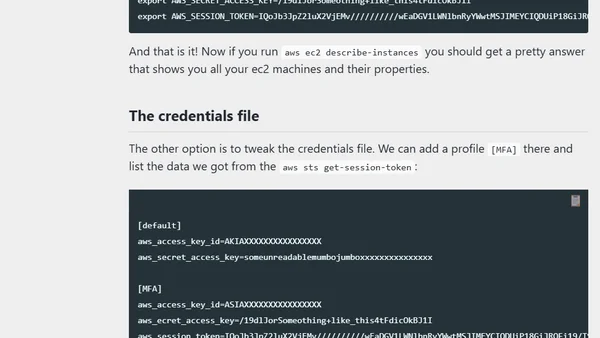
A guide to enforcing AWS IAM 2FA and scripting logins for secure, automated command-line access.
Announcing a new book for JavaScript developers on practical cryptography, covering hashing, encryption, and digital signatures.
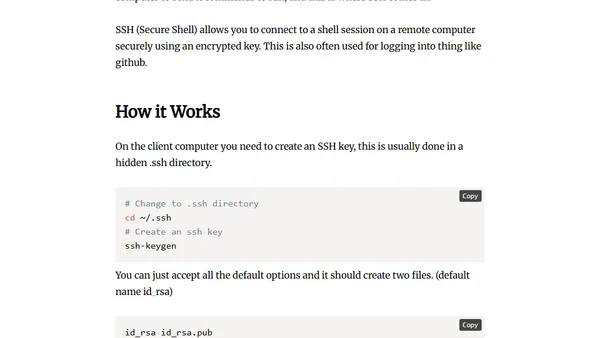
Explains SSH (Secure Shell), its purpose for secure remote computer connections, and how to generate and use SSH keys.
A critical analysis of Plaid's security model, arguing its credential collection widget undermines decades of online banking security best practices.
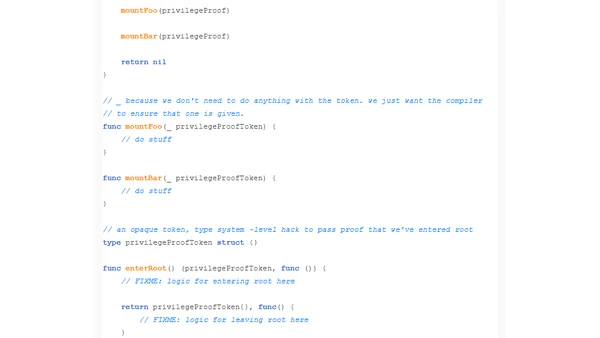
A programming pattern using opaque tokens and the type system to ensure functions requiring root privileges are only called from within a root context.
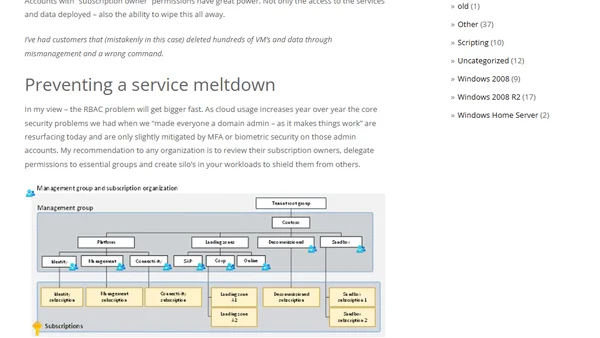
Discusses when to create new Azure subscriptions vs. consolidating workloads, focusing on security and management best practices.
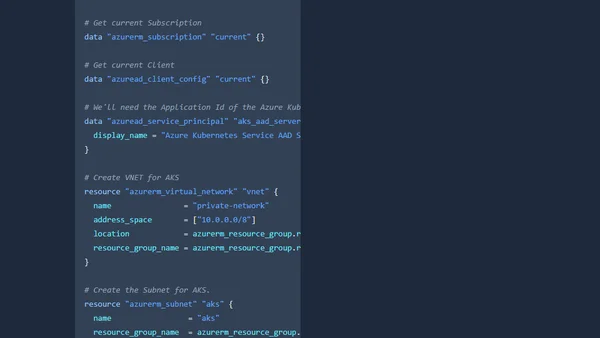
Guide to disabling local accounts on Azure Kubernetes Service (AKS) clusters using Terraform for improved security and auditability.
A blogger shares their 2022 goals for writing, media production, and software development, focusing on accountability and personal growth.
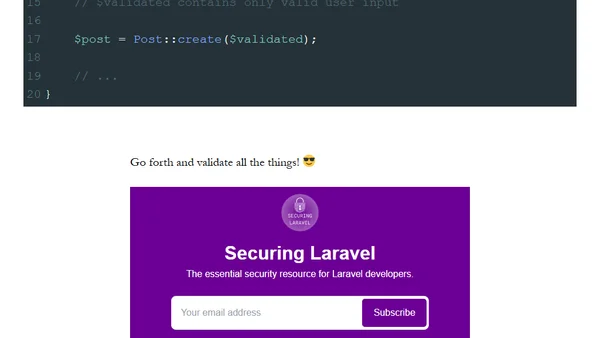
A Laravel security tip emphasizing the critical importance of validating all user input to prevent unexpected behavior and security vulnerabilities.
Explains why using user accounts for Azure Logic App connections is a security risk and recommends using managed identities instead.
Signal's new sponsorship model is a sustainable alternative to ad-based revenue, ensuring user privacy and long-term viability.
Using Python's pytm framework to threat model the security flaws in the fictional systems of Jurassic Park.
Analyzes the security flaws in Flatpak's all-or-nothing permissions model and compares it to more granular systems like iOS.
A technical guide explaining how to implement authentication and authorization in any backend language or framework, covering user models, signup/login routes, and session vs JWT auth.
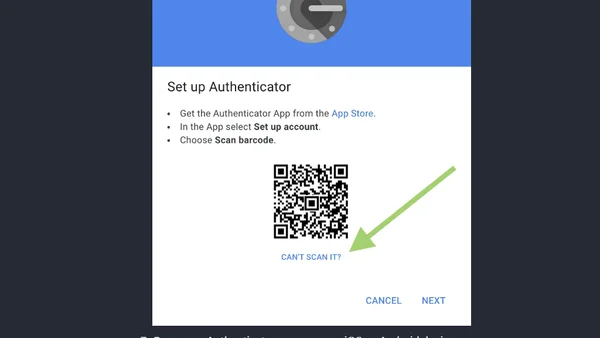
A technical guide on automating the bypass of two-factor authentication (2FA) for use in scripts and automated testing.