Try a URL Sandbox! (For Free!)
Learn how to use a free URL sandbox to safely open suspicious links and test websites in isolated, remote browsers without risking your device.
Learn how to use a free URL sandbox to safely open suspicious links and test websites in isolated, remote browsers without risking your device.
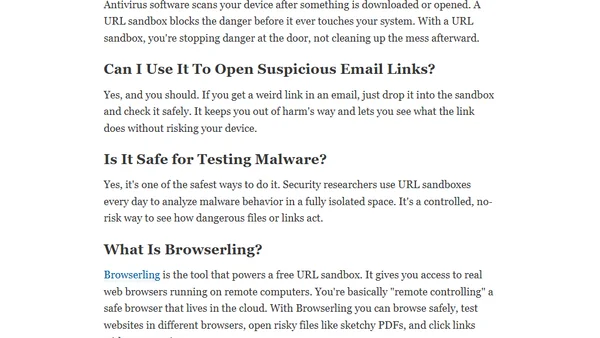
Explains how to embed Info.plist, sign with entitlements, and use undocumented APIs to make AppleScript work in macOS CLI tools without permission dialogs.
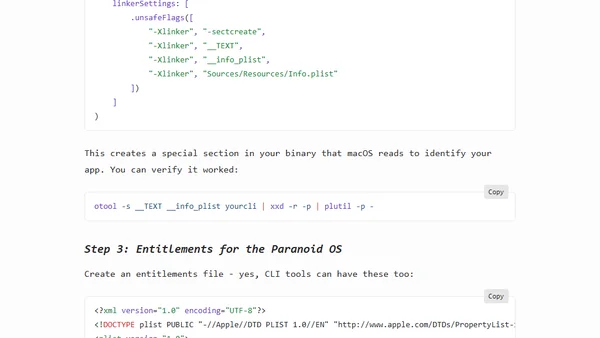
A guide for FOSS community leaders on handling reactionary agitators, contrasting ineffective and effective response strategies.
AI agents' autonomous and probabilistic nature forces stricter security and authorization models, breaking traditional microservice assumptions.
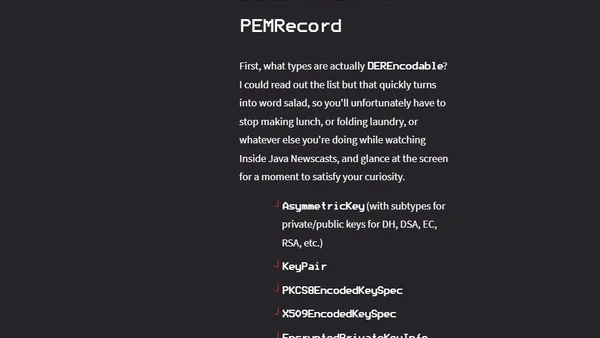
Java 25 introduces a new preview API for easily encoding and decoding cryptographic objects in the PEM text format, addressing a key developer pain point.
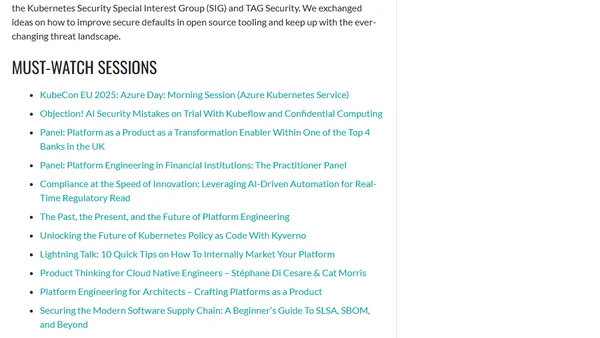
A developer shares their journey to speaking at KubeCon EU 2025, presenting on shifting security down into the platform, and key takeaways from the event.

An engineer critiques the poor security practices in many software companies, highlighting willful neglect and developer resistance to basic safeguards.

SQL Server 2022 Cumulative Update 19 includes a critical security fix for auditing missing permission changes, urging immediate installation.

A security experiment exposing a SQL Server to the internet, revealing attack patterns and providing security recommendations.
A recap of KubeCon NA 2024 highlighting key trends in cloud-native tech: WebAssembly (WASM), Platform Engineering, and Security.
A speaker shares their experience presenting on Kubernetes security at the KubeHuddle Toronto 2024 community conference.

Explores the security risks of self-replicating PHP code (quines), detailing how their underlying patterns can lead to vulnerabilities.
A developer shares their experience and key takeaways from attending and speaking at Cloud Native Security Con 2024 in Seattle.
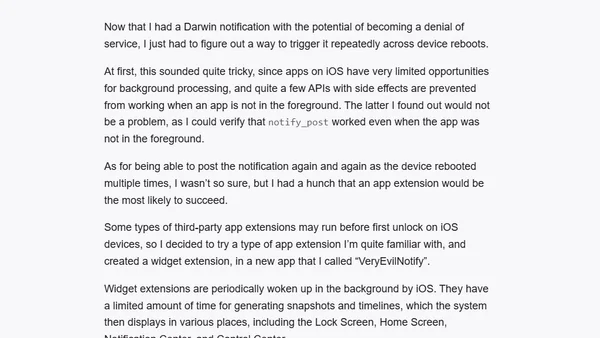
A developer details a simple iOS vulnerability using Darwin Notifications, a legacy public API, that could potentially brick an iPhone.
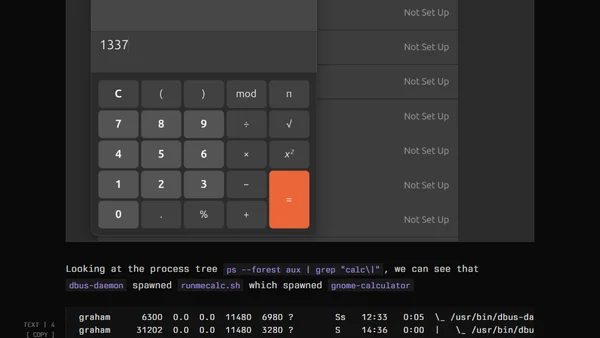
Explores a Linux user-land persistence technique using D-Bus to execute code without root access, targeting desktop environments.
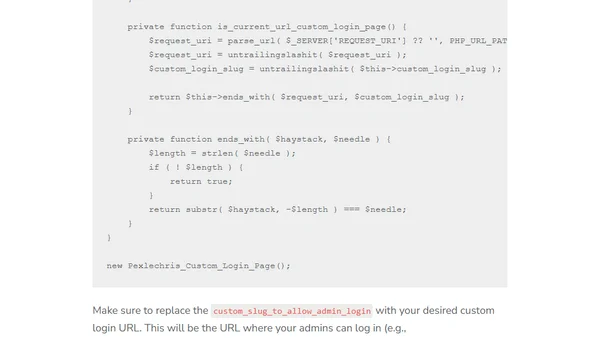
A technical guide on using custom PHP code to hide and secure the WordPress admin login page, offering a lightweight alternative to plugins.
Part 3 of a series on SQL Server security, covering auditing, encryption, and secure development practices for DBAs.
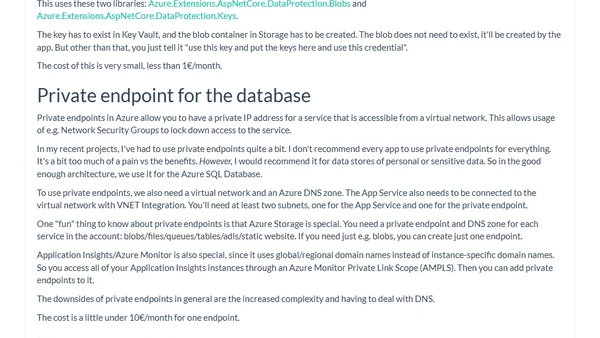
A guide to implementing cost-effective, 'good enough' security for Azure PaaS applications, covering architecture, Entra ID, WAF, and Managed Identities.
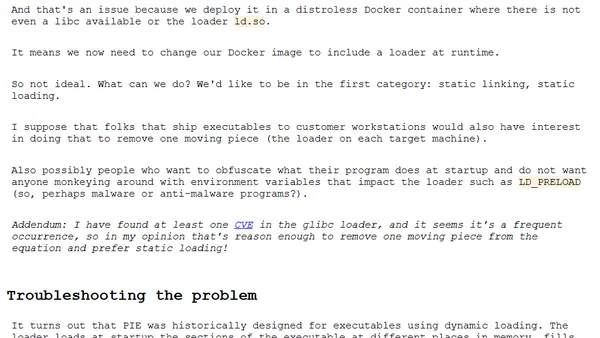
A technical guide on enabling Position Independent Executable (PIE) builds in Go for security hardening, covering the process and troubleshooting dynamic linking issues.
![Devs: draw your line [blog]](https://alldevblogs.blob.core.windows.net/thumbs/article-46fafe2d50fe-full-cab9d995.webp)
A developer's call to action to protect user privacy by refusing to implement invasive tracking scripts, especially on sensitive data like medical information.