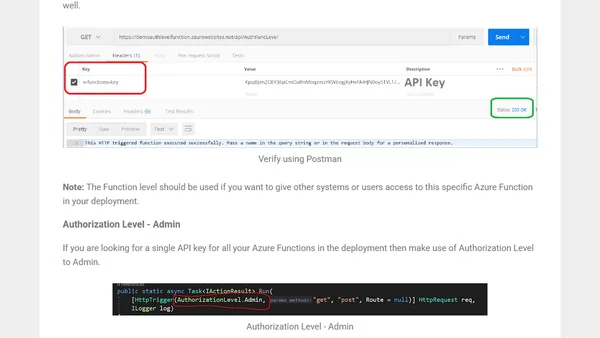
Authenticate Azure Functions - API Keys
A guide to securing Azure Functions using API keys, covering different authorization levels and practical verification with Postman.
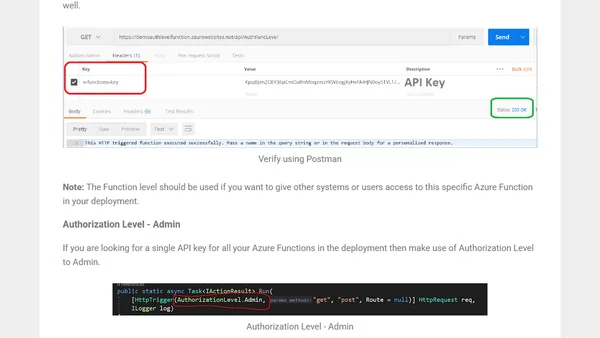
A guide to securing Azure Functions using API keys, covering different authorization levels and practical verification with Postman.
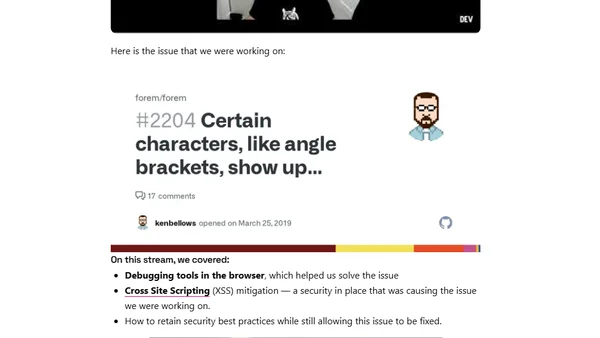
A live coding session on debugging browser tools and XSS mitigation while fixing an issue to render HTML tags as text.
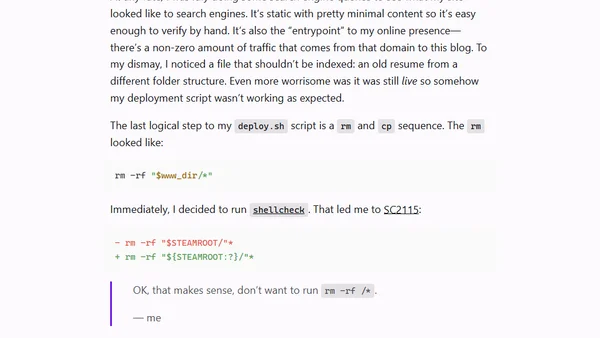
A developer recounts a dangerous Bash scripting mistake that could have deleted his entire server, highlighting the importance of proper glob expansion and shellcheck.
A guide to securing Azure DevOps pipelines using approvals, environments, and Azure Key Vault to prevent unauthorized or malicious changes.
A guide on using environment variables in React to securely manage sensitive data like API keys and database credentials.
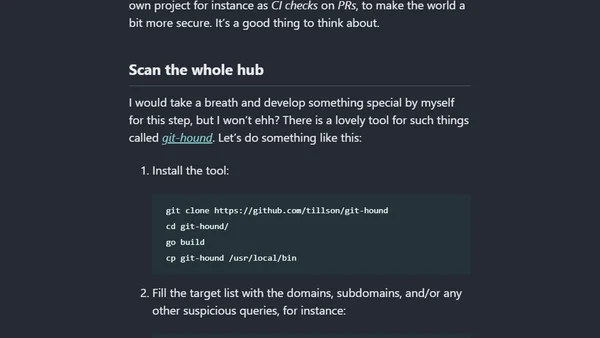
A technical guide on using tools like gitleaks, earlybird, and git-hound to find security leaks and exposed secrets in code repositories.
OpenIddict 3.0, a .NET OpenID Connect server and validation library, is now generally available with a rewritten, event-oriented architecture.
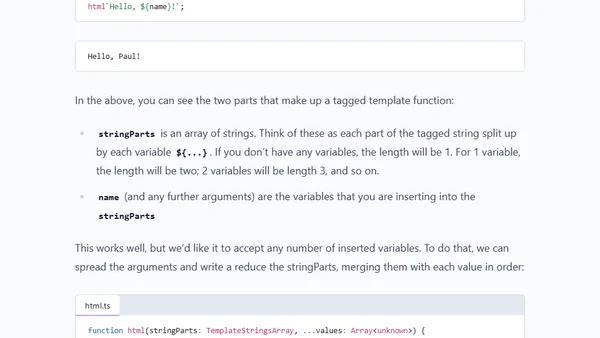
Explains how to safely generate HTML responses in Express.js without a templating engine, focusing on preventing XSS attacks.
Let's Encrypt's root certificate change may cause website trust issues for older Android devices, affecting millions of users globally.
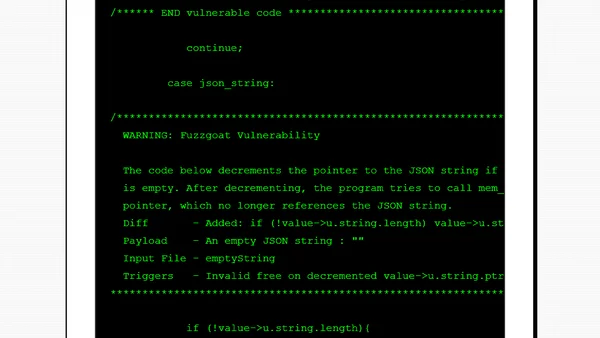
An evaluation of GitHub's CodeQL-based code scanning feature, testing its reliability in detecting vulnerabilities in a sample C codebase.
A guide to implementing secret scanning with GitLeaks in Azure DevOps pipelines to prevent accidental exposure of API keys and passwords in code repositories.
A developer recounts accidentally creating a spying app as a teenager while trying to solve the iPhone's 1000-SMS limit, exploring early mobile hacking.
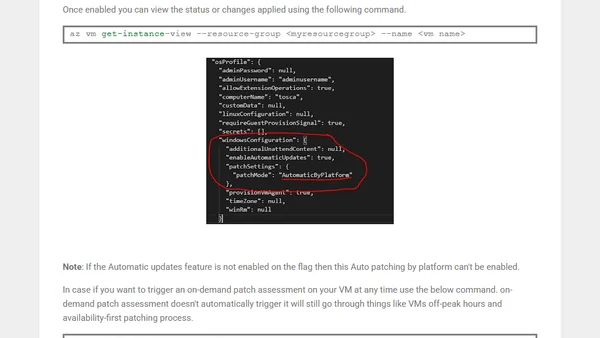
Guide to enabling Automatic Guest OS Patching for Windows Azure VMs, a public preview feature for automated security updates.
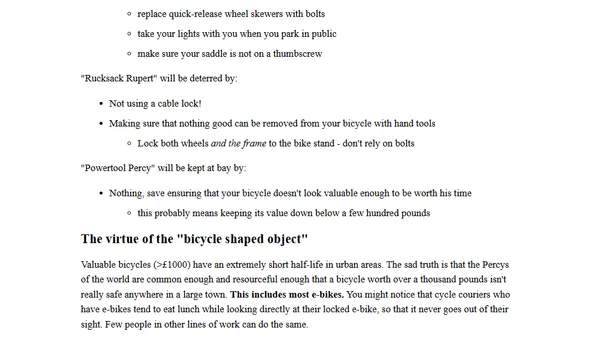
A threat modeling case study using bicycle theft to illustrate security principles applicable to IT systems.
A guide on using the Terminal command `spctl` to verify if a macOS application has been notarized by Apple.
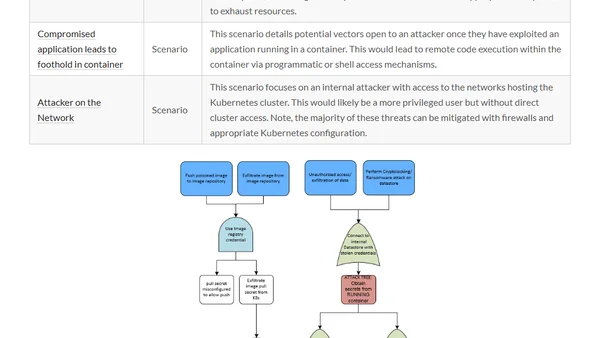
A summary of three major Kubernetes threat modeling initiatives to help security professionals secure their production clusters.
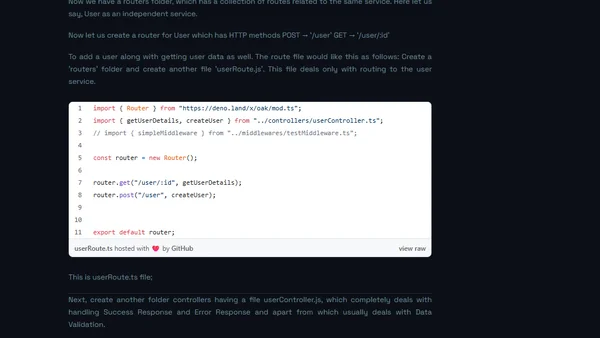
A technical analysis comparing Deno and Node.js, focusing on Deno's design improvements like security, URL imports, and eliminating node_modules.
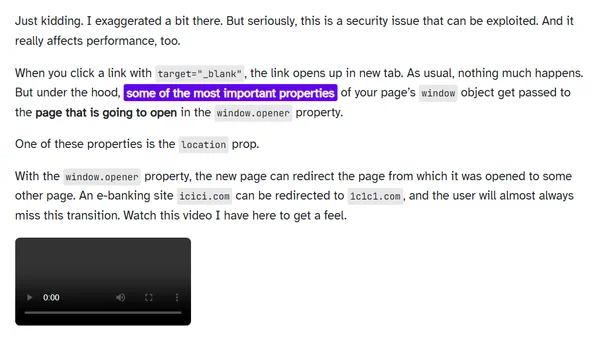
Explains the security and performance risks of using target=_blank links without rel="noopener" and provides the simple fix.
A detailed analysis of a blackmail email scam demanding a $2000 Bitcoin payment to prevent the release of compromising material.
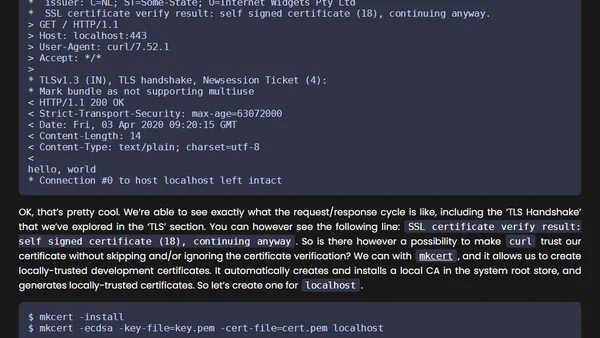
A guide to implementing security best practices for Go HTTP webservers, covering timeouts, TLS, and other hardening measures.