Get prepared for default outbound access retirement
Discusses the retirement of Azure's default outbound access for VMs in 2025, explaining the security reasons and urging preparation.
Discusses the retirement of Azure's default outbound access for VMs in 2025, explaining the security reasons and urging preparation.
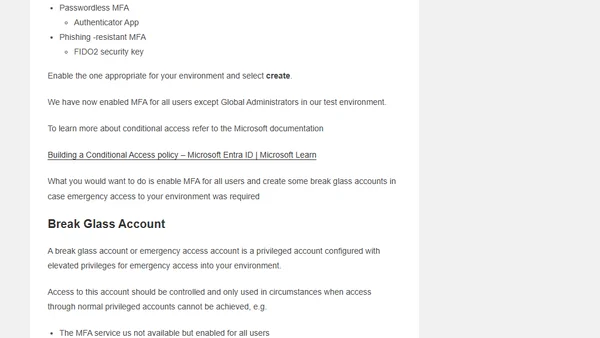
A technical guide on securing user identity in Azure Entra ID, covering MFA, Conditional Access, break glass accounts, and other security configurations.
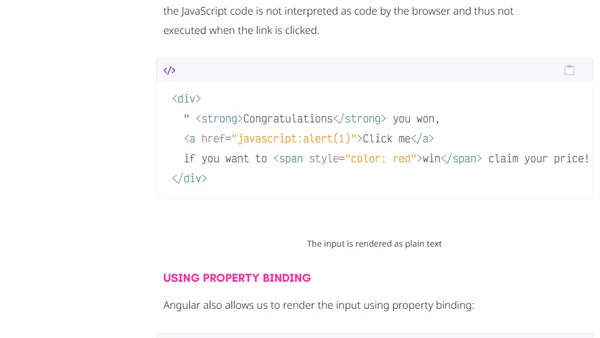
Explains how Angular's built-in security features automatically protect web applications from Cross-Site Scripting (XSS) attacks by sanitizing untrusted values.

An open source maintainer explains why automated security reports about nested dependencies are often unhelpful and asks developers to stop sending them.
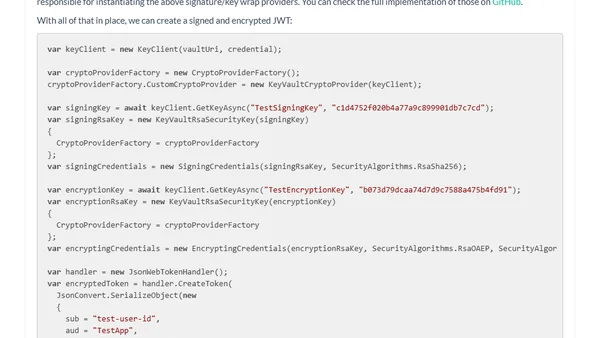
Explains how to use Azure Key Vault keys for signing and encrypting JSON Web Tokens (JWTs), including key rotation.
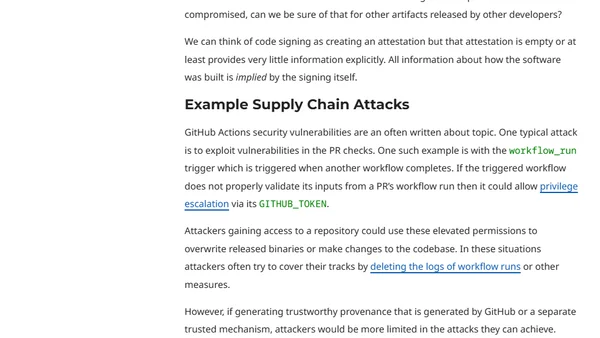
Explains the limitations of code signing for software security and introduces software provenance as a more robust alternative.

A developer's prank NPM package called 'everything' that depends on all public packages causes dependency chaos and highlights registry policy flaws.
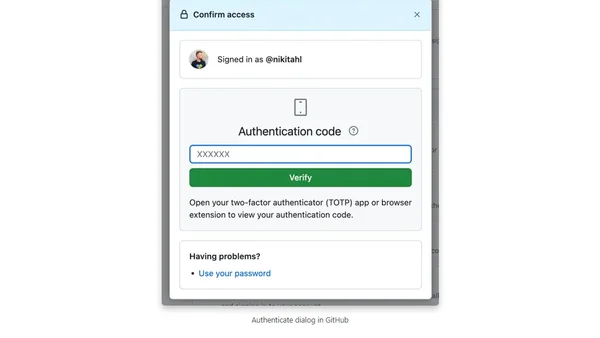
A step-by-step guide on how to change the TOTP-based two-factor authentication app linked to your GitHub account.
A fable about a security guardian and a developer learning to collaborate, illustrating the principles of DevSecOps and secure software development.
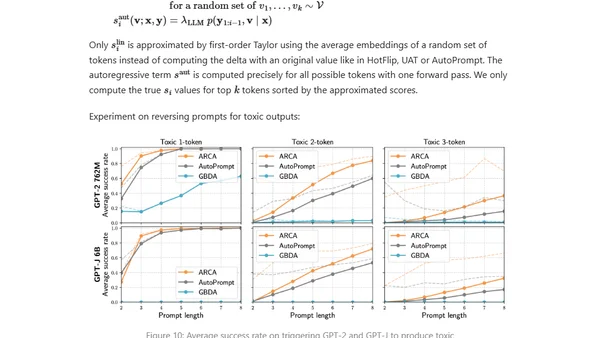
Explores adversarial attacks and jailbreak prompts that can make large language models produce unsafe or undesired outputs, bypassing safety measures.
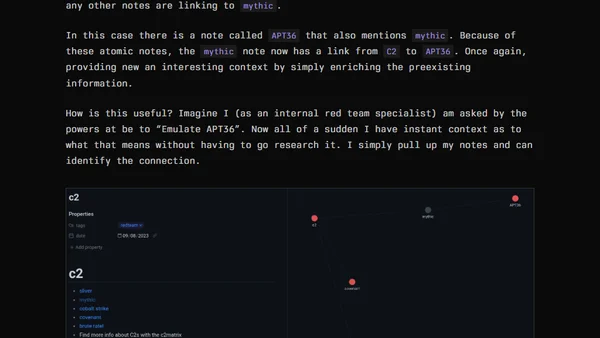
A security researcher shares a personal system for managing knowledge and taking effective notes for actionable cybersecurity learning and research.
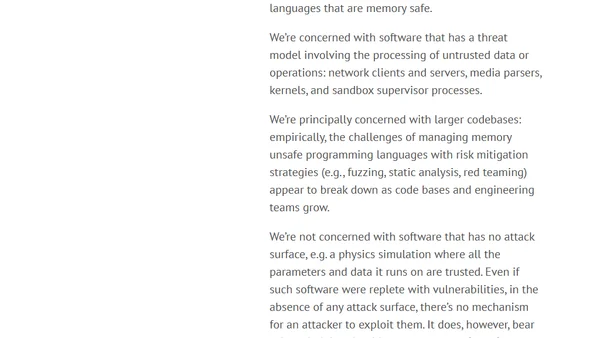
A detailed analysis of memory unsafe programming languages, their security risks, and the types of software most affected by these vulnerabilities.
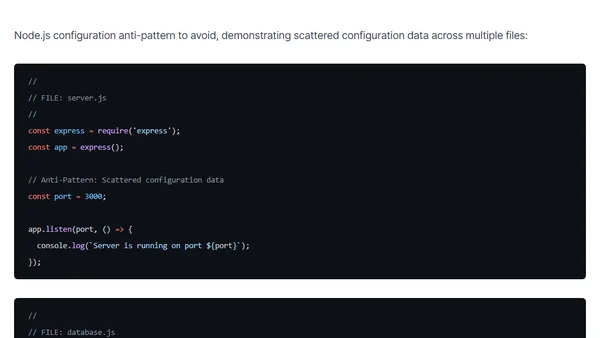
Explores configuration management patterns and anti-patterns for Node.js applications, focusing on security, portability, and maintainability.
Explains why using the Device Filter is more secure than Device Platform for Conditional Access policies targeting managed devices.
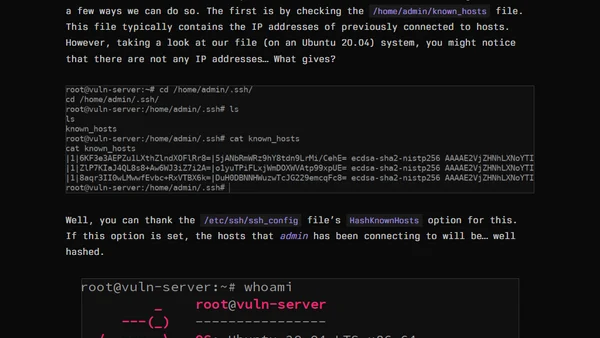
Explores the security risks of SSH-Agent forwarding, demonstrating how attackers can abuse it for lateral movement in compromised networks.
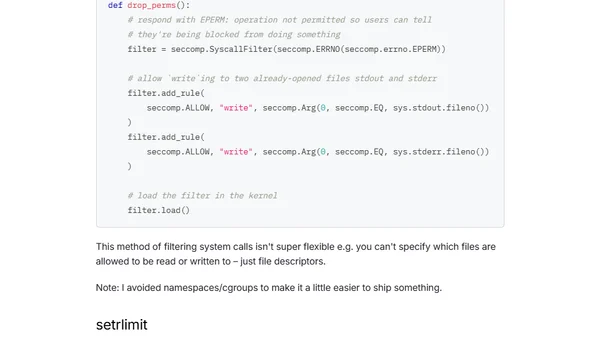
A developer explores the challenges of sandboxing untrusted Python code in a side-project, using process isolation and seccomp.
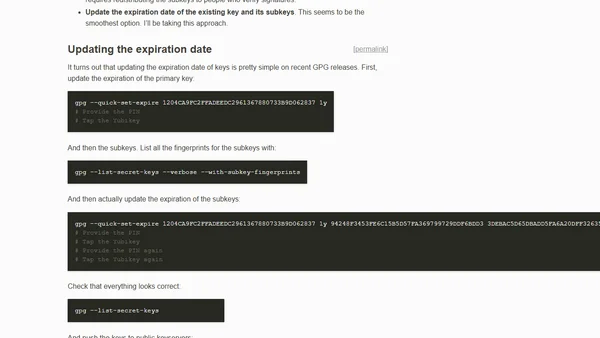
A technical guide on how to extend the expiration date of an existing GPG key and its subkeys, including commands and best practices.
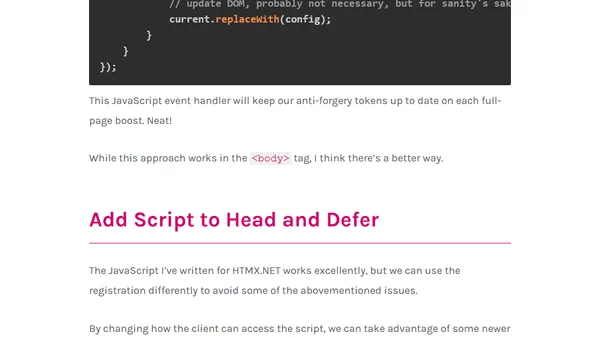
Explains how to handle ASP.NET Core anti-forgery tokens when using HTMX boosts, including solutions for script re-registration.
A developer shares a cautionary tale about identity theft on freelancer platforms, based on a Darknet Diaries podcast episode.
Explains why eBPF observability tools, designed for low overhead, are not suitable for security monitoring due to evasion risks.