mod_defensible 1.5 released
The author updates the Apache module mod_defensible to be compatible with Apache 2.4, discussing the process and its utility as a prototype.
The author updates the Apache module mod_defensible to be compatible with Apache 2.4, discussing the process and its utility as a prototype.
Debunks the myth that PHP is inherently insecure, attributing its reputation to FUD, its ubiquity, and its forgiving nature for beginners.
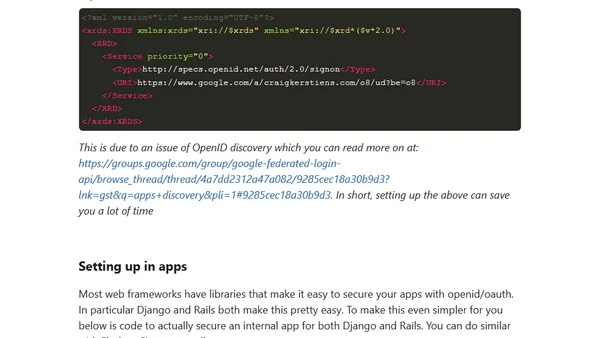
Explains how to use OpenID with Google Apps to secure internal company applications, replacing VPNs for a cleaner authentication workflow.
A security researcher details a clickjacking vulnerability in Adobe Flash that allowed websites to secretly activate users' webcams and microphones.
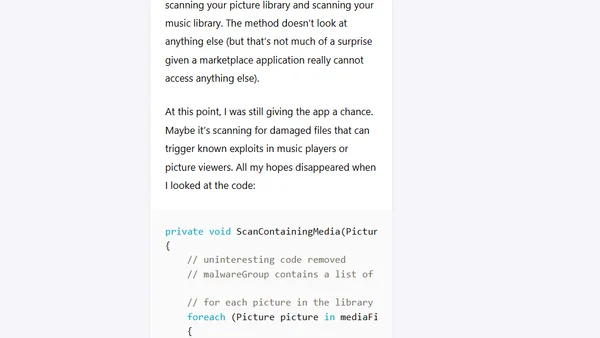
Analysis of the AVG Mobilation antivirus app for Windows Phone, revealing it as a non-functional port with humorous, ineffective scanning code.
Oracle's July Critical Patch Update addresses a security vulnerability (CVE-2011-2241) in OBIEE versions 10.1.3.4.1 and 11.1.1.3.
Discusses the prevalence of Game Center score hacking via jailbreak apps and criticizes Apple's lack of enforcement.
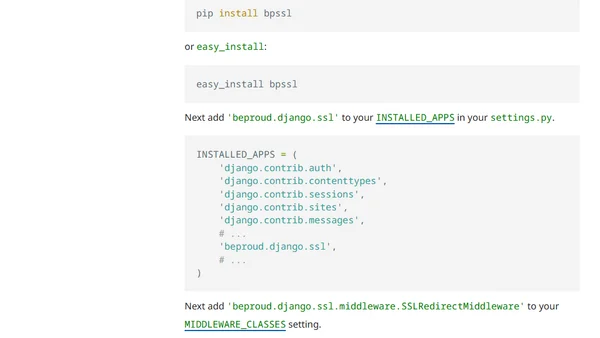
Introducing bpssl, a Django application for managing HTTPS redirection and securing specific URLs at the application level.
A technical guide on creating a Python decorator to restrict Google App Engine cron job URLs to authorized requests only.
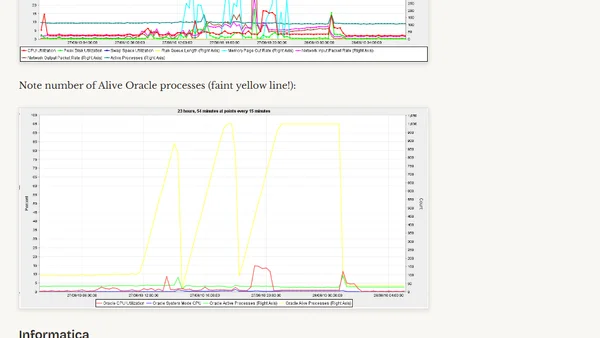
A technical analysis of how an expired database password caused Informatica to spawn excessive connections, crashing an Oracle server.

Exploring the idea of automatic login via notification emails, discussing the tradeoffs between usability and security.
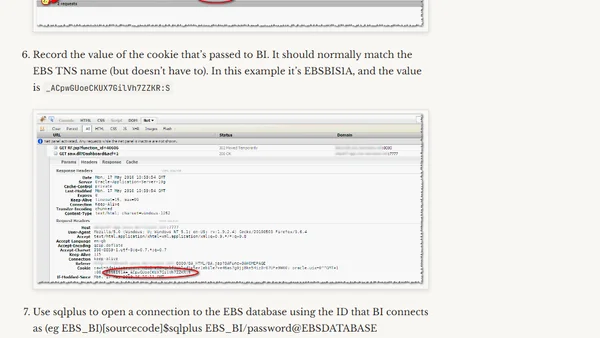
A technical guide for troubleshooting EBS-BI integrated authentication by validating session cookies directly in the Oracle database.
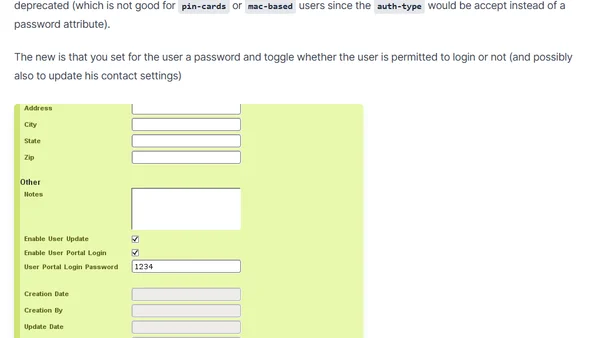
daloRADIUS update deprecates old user portal authentication method, introduces new password and permission settings for better security.
Investigating Google Chrome's persistent background connections to 1e100.net domains, exploring their purpose and potential tracking implications.
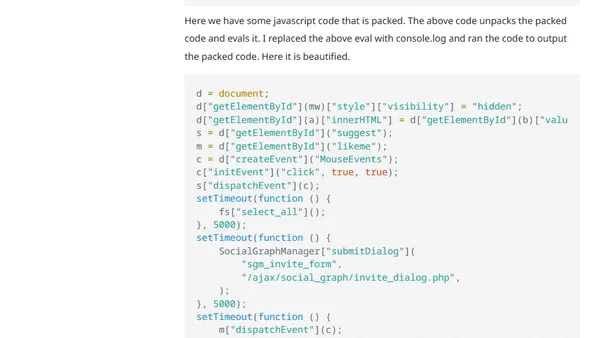
Analysis of a deceptive Facebook app that tricks users into running malicious JavaScript to spam friends.
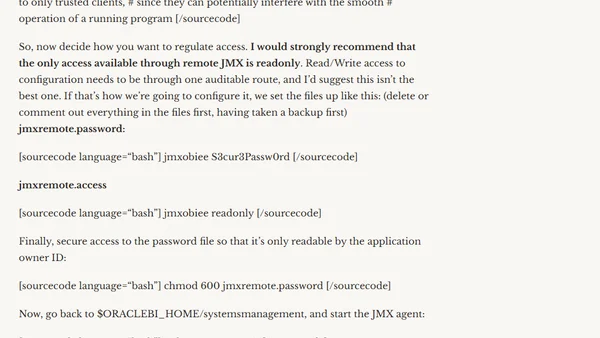
Discusses a security vulnerability in OBIEE's JMX remote access and provides steps to secure it with password authentication.
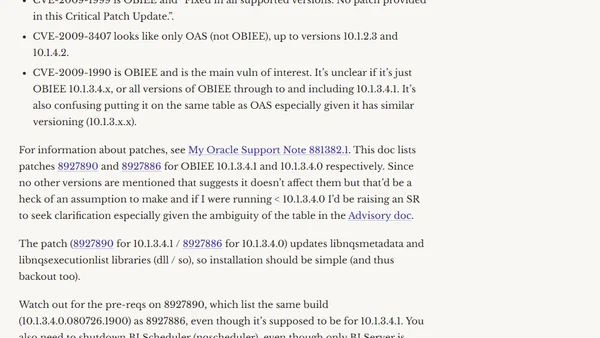
Analysis of Oracle's October Critical Patch Update, focusing on the OBIEE vulnerability CVE-2009-1990 and its patch details.
A guide to installing Microsoft Security Essentials on Windows Server 2008 by modifying system checks during installation.
Oracle's October Critical Patch Update addresses security vulnerabilities in OBIEE and Oracle Application Server, requiring immediate attention.

A security vulnerability in SQL Server (2005-2008 R2) allows guest account impersonation to bypass database access controls, with a fix planned for a future version.