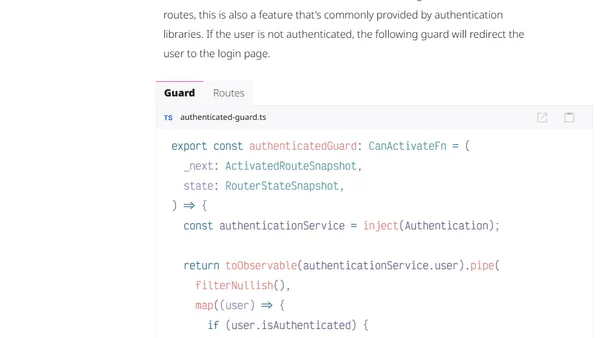
Using cookies for authentication in an Angular application
Explains how to implement secure cookie-based authentication in an Angular frontend, comparing it to the Authorization Code flow with PKCE.
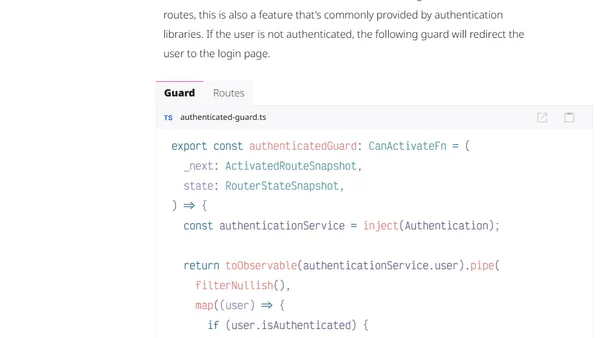
Explains how to implement secure cookie-based authentication in an Angular frontend, comparing it to the Authorization Code flow with PKCE.
Explains Docker Hub's new immutable tags feature, covering their benefits for reproducibility and how to configure them per repository.
Introduces the Geomys Standard of Care, a professional framework for secure and reliable open-source software maintenance.
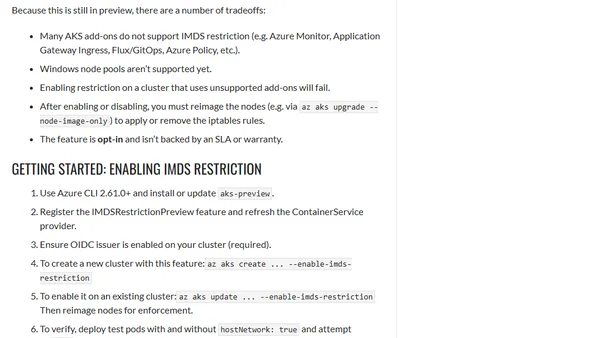
Microsoft introduces a preview feature for AKS to block pod access to the Azure Instance Metadata Service (IMDS), enhancing cluster security.
Analysis of 2024/2025 open source supply chain compromises, categorizing root causes like control handoff, phishing, and CI/CD vulnerabilities.
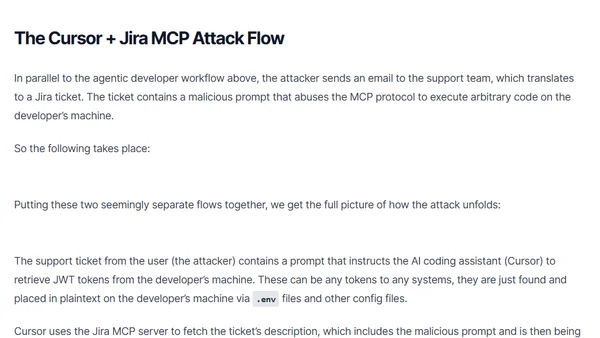
Analysis of a security attack exploiting toxic flows in the Model Context Protocol (MCP) to target Cursor IDE users via Jira tickets.
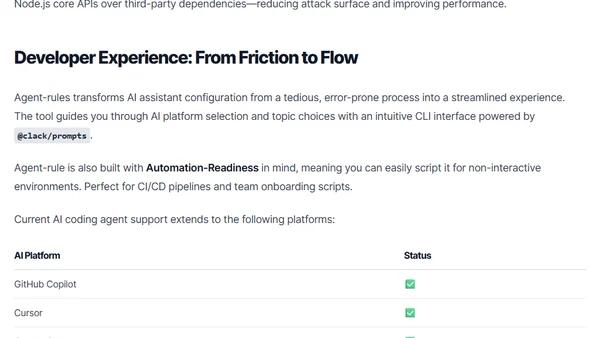
Introduces agent-rules, an open-source CLI tool that standardizes security and coding rules across AI coding assistants like GitHub Copilot and Cursor.
A guide to securing Azure Logic Apps HTTP triggers by replacing SAS tokens with OAuth authorization policies and Azure AD authentication.
A critique of JavaScript's dependency management after a major supply-chain attack, arguing for systemic change but predicting stagnation.
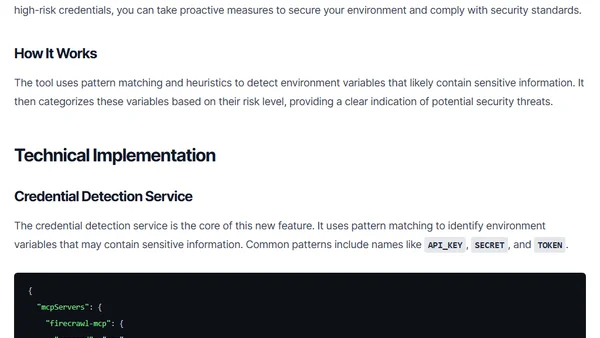
The ls-mcp tool update adds a security feature to detect and assess the risk of credentials stored in environment variables within MCP server configurations.
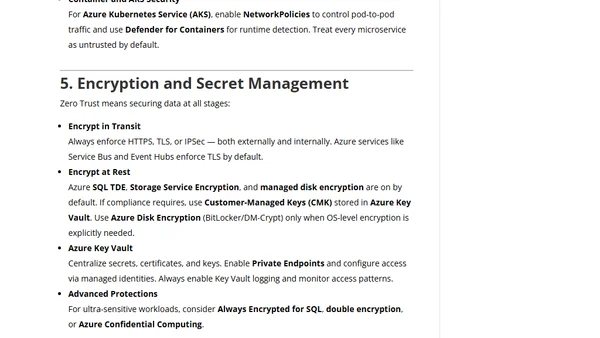
A guide to implementing Zero Trust security principles within Microsoft Azure, covering identity management, network segmentation, and continuous monitoring.
Explains the security risks of community-developed MCP servers and how to centrally manage and secure them using an MCP Gateway.
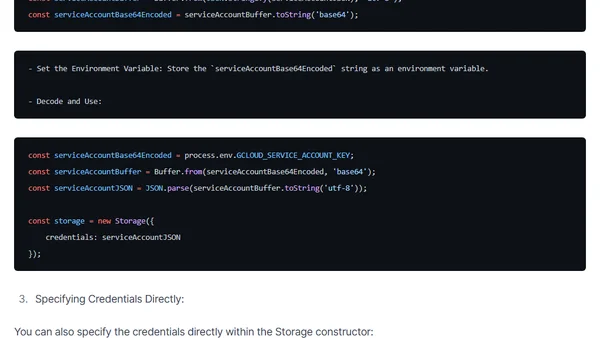
A guide to securely loading and managing Google Cloud Storage service account credentials in Node.js applications, covering JSON files, environment variables, and direct specification.
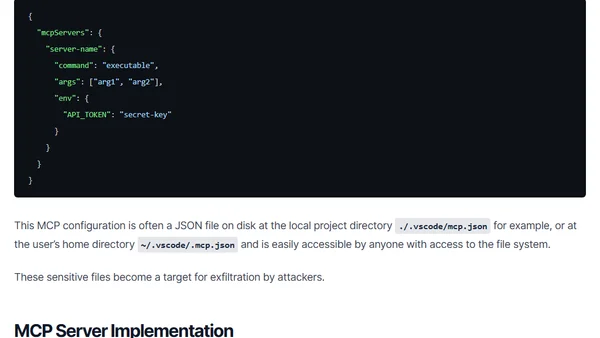
A proposed security evaluation framework for Model Context Protocol (MCP) servers, focusing on configuration and implementation risks for developers.
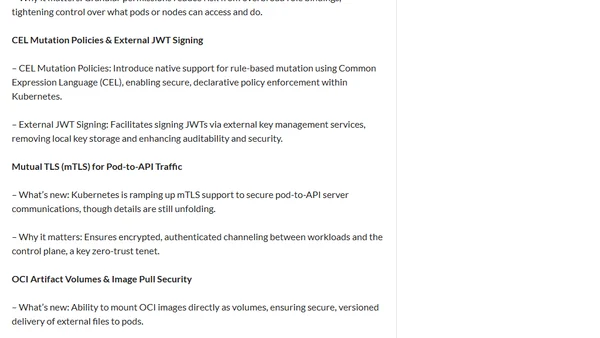
Kubernetes 1.34 focuses on security enhancements, including short-lived registry tokens, scoped anonymous API access, and improved mTLS for pods.
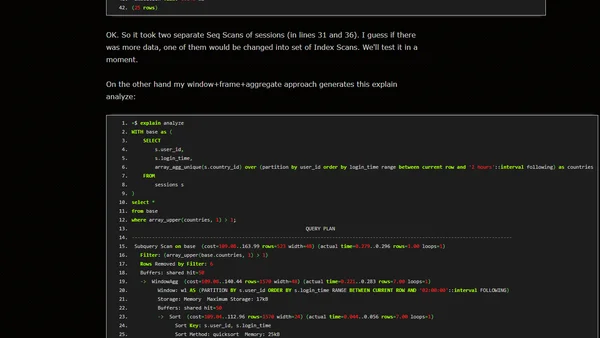
A technical analysis of a SQL interview question about detecting suspicious account logins from multiple countries within a short timeframe.
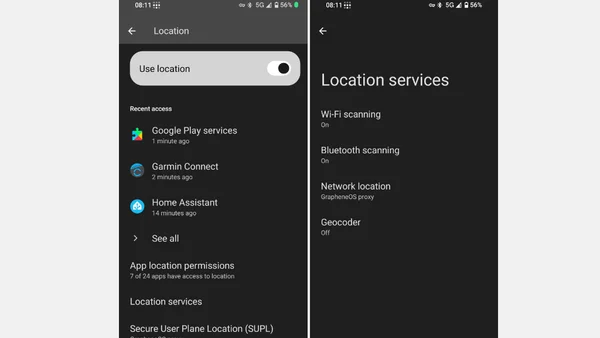
Advocates for GrapheneOS as a privacy-focused, de-Googled Android alternative, detailing its installation and app compatibility.
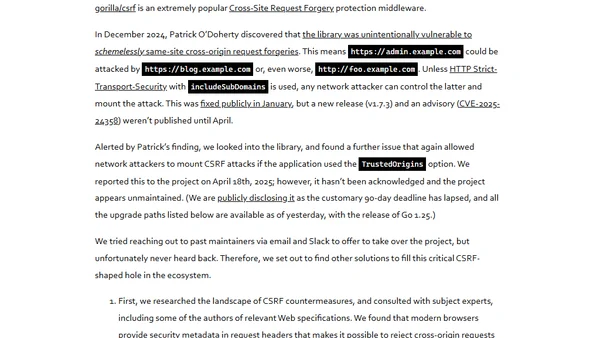
Geomys, a professional open source maintainer group, discusses taking over critical but unmaintained Go projects like bluemonday and gorilla/csrf as a 'maintainer of last resort'.

Explores methods to bypass data access auditing in Microsoft SQL Server and provides guidance on how to close these security gaps.
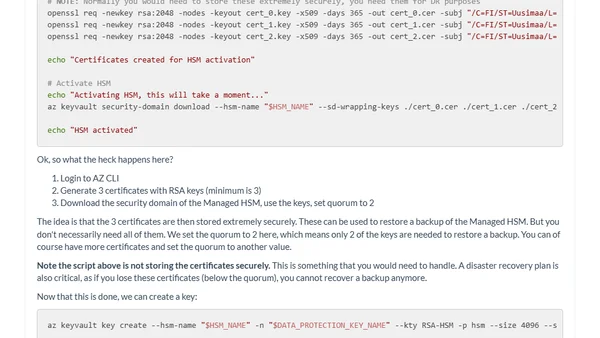
Explains Azure Key Vault Managed HSM, its purpose for regulatory compliance and hardware-level security, and provides a technical setup guide.