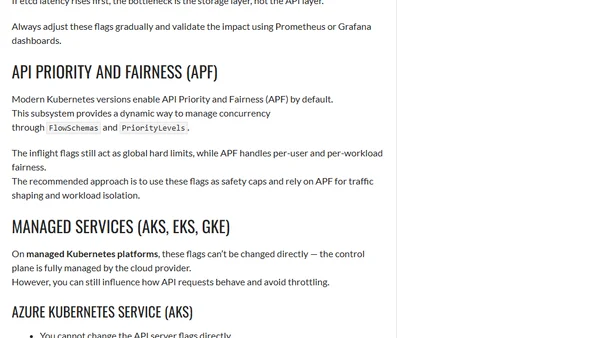
Understanding Kubernetes API Server Concurrency Controls
Explains how Kubernetes API server concurrency controls like --max-requests-inflight work to manage performance and prevent overload.
Explains how Kubernetes API server concurrency controls like --max-requests-inflight work to manage performance and prevent overload.
Explains how to implement Web Application Firewall (WAF) support in Azure Application Gateway for Containers for Kubernetes security.
A practitioner's key takeaways from the fwd:cloudsec 2025 conference, focusing on cloud security research, offensive techniques, and defensive strategies.
A technical deep-dive into diagnosing and resolving a persistent 'StopPodSandbox' error in Kubernetes Kubelet logs, focusing on network and CNI issues.
Explains how Kube-proxy uses iptables for load-balancing in Kubernetes and the implications for gRPC/HTTP/2 traffic.
A guide to using Azure Chaos Studio for controlled reliability testing, turning assumptions into evidence through safe, structured chaos experiments.
Explains how Azure Arc provides unified management for hybrid and multi-cloud environments, bringing on-prem and other cloud resources into Azure's control plane.
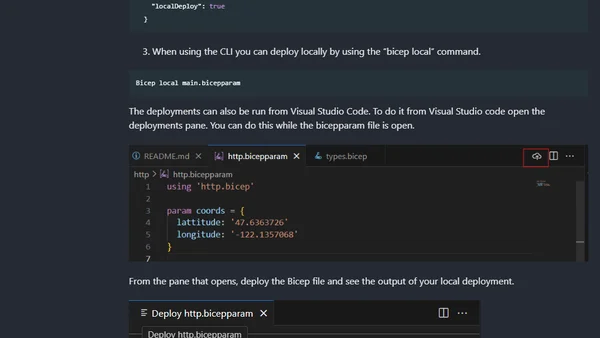
Explores Bicep extensions for deploying resources beyond Azure, covering their limitations and the new local deployment preview feature.

Explains CPU throttling in Kubernetes, how to identify it via metrics, and discusses a Linux kernel regression causing the issue.
Kubernetes 1.34 focuses on security enhancements, including short-lived registry tokens, scoped anonymous API access, and improved mTLS for pods.
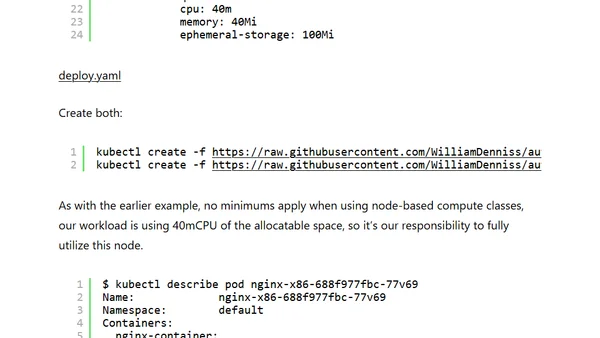
A technical guide on deploying Arm workloads on Google Kubernetes Engine using C4A and C4D Compute Classes.
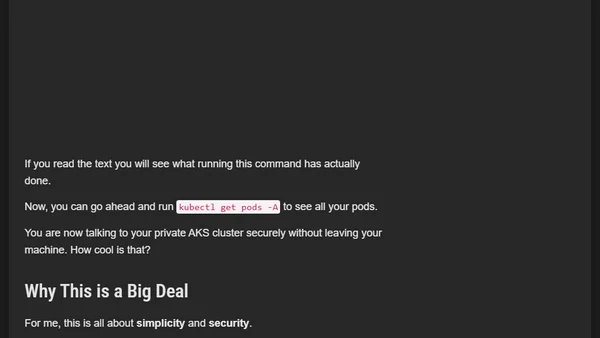
A guide on using Azure Bastion to securely connect to a private AKS cluster without needing a jump box VM, simplifying access and management.
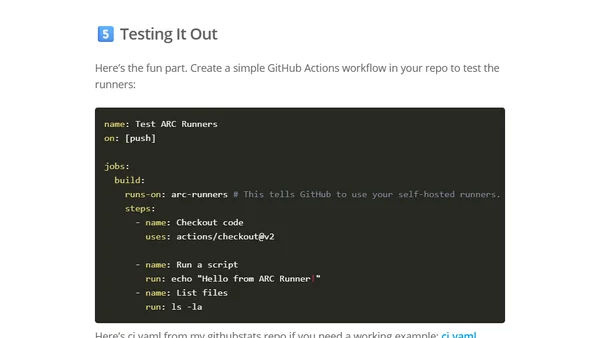
A guide to deploying self-hosted GitHub Actions runners on a home Kubernetes cluster using the Actions Runner Controller (ARC).
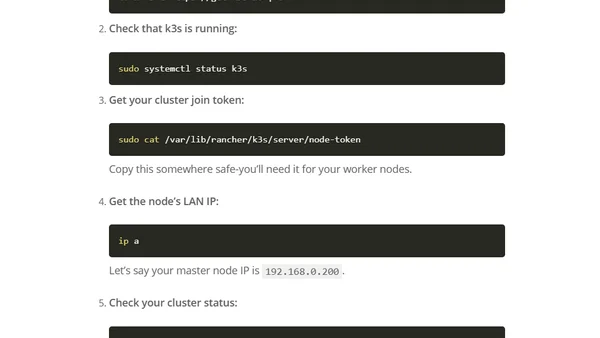
A guide to building a powerful home Kubernetes cluster using old laptops, Ubuntu Server, and the lightweight k3s distribution for development and CI/CD.
A guide to deploying and comparing open-weight LLM families (DeepSeek, Falcon, Llama, etc.) using the KAITO operator on Azure Kubernetes Service (AKS).
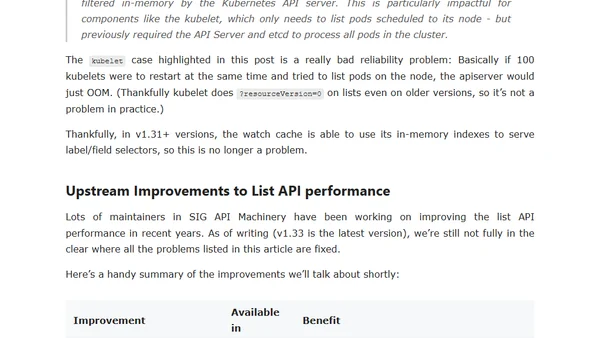
Analyzes performance and reliability challenges of Kubernetes List API calls at massive scale, explaining high-risk patterns and recent improvements.
![Any kubectl command throws "Unhandled Error" err="couldn't get current server API group list: Get "http://localhost:8080/api?timeout=32s": dial tcp [::1]:8080: connect: connection refused" - what do?](https://alldevblogs.blob.core.windows.net/thumbs/article-cfa76fb7e918-full-787fa002.webp)
Fixing kubectl connection errors when commands fail with 'connection refused' on localhost:8080.
Explores using SPIFFE workload identity for AI agents, highlighting technical gaps in current Kubernetes implementations for non-deterministic agent behavior.
Explains how Envoy Proxy enables Zero Trust Architecture in cloud-native environments through mTLS, RBAC, and centralized traffic control.
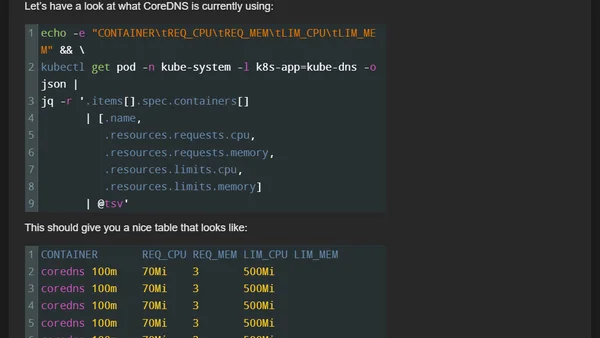
Explains how to use Azure Kubernetes Service's new preview feature for cost-optimized scaling of system add-ons using the managed Vertical Pod Autoscaler.