Using Docker-in-Docker for your CI or testing environment? Think twice.
Explains the pitfalls of Docker-in-Docker for CI/testing and recommends using bind-mounted Docker sockets or modern alternatives like sysbox.
Explains the pitfalls of Docker-in-Docker for CI/testing and recommends using bind-mounted Docker sockets or modern alternatives like sysbox.
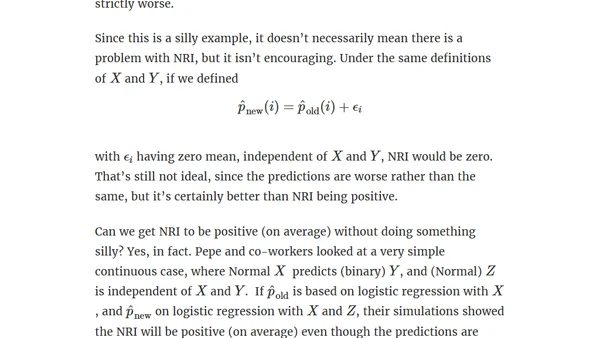
A technical critique of the Net Reclassification Index (NRI), a statistical measure for evaluating prediction model improvements, highlighting its surprising biases.
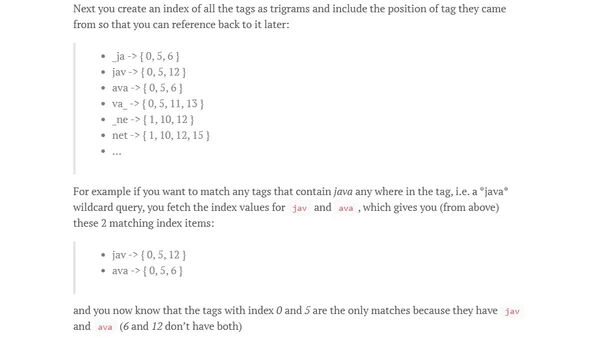
Deep dive into the technical design of Stack Overflow's Tag Engine, focusing on implementing ignored tag preferences and performance considerations.
A comprehensive overview of Project Jigsaw, the new module system coming in Java 9, covering its motivation, features, and syntax.
SoundCloud's journey from a monolithic architecture to a microservices system using Scala and Finagle, including monitoring with Prometheus.
Exploring Aspect-Oriented Programming in JavaScript to handle cross-cutting concerns like logging, using the aspect.js library.
Oracle releases critical security patches for OBIEE, ODI Data Quality, and Exalytics systems, addressing vulnerabilities in specific versions.
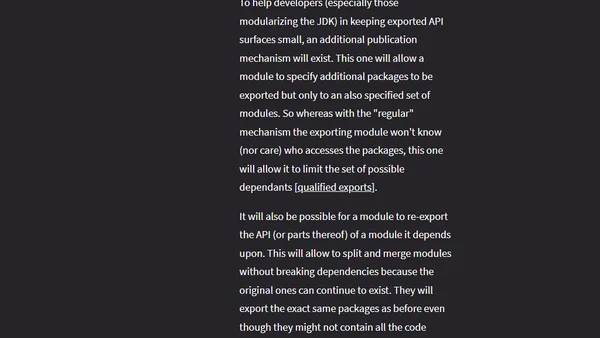
Explores the core concepts and features of Project Jigsaw, the module system introduced in Java 9, and its impact on code organization.
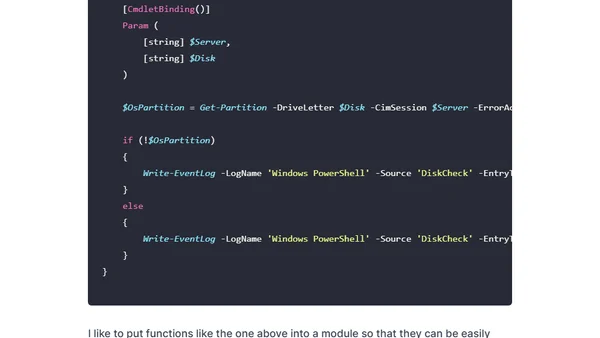
Explains how to use PowerShell scripts with Pulseway monitoring software to create custom alerts based on system events.
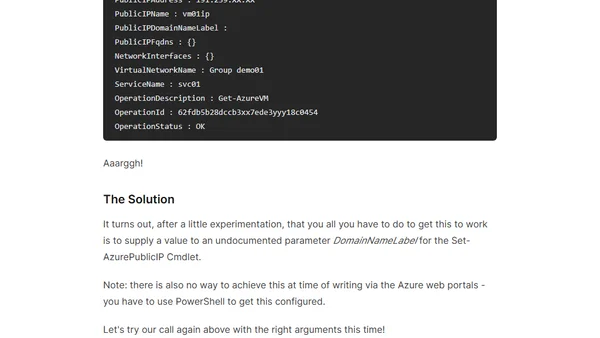
How to configure a static public IP address (ILPIP) on an Azure VM using PowerShell, including a key undocumented parameter.
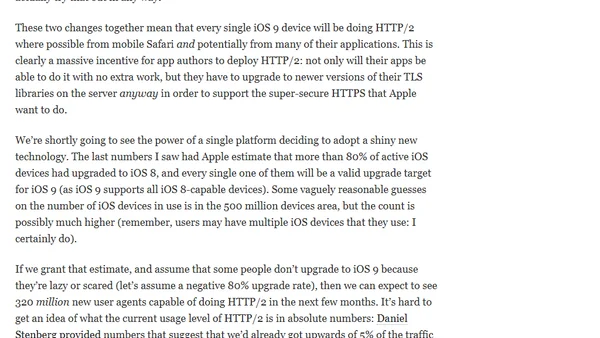
iOS 9 enables HTTP/2 and HTTPS by default for apps, accelerating adoption and requiring server-side upgrades.
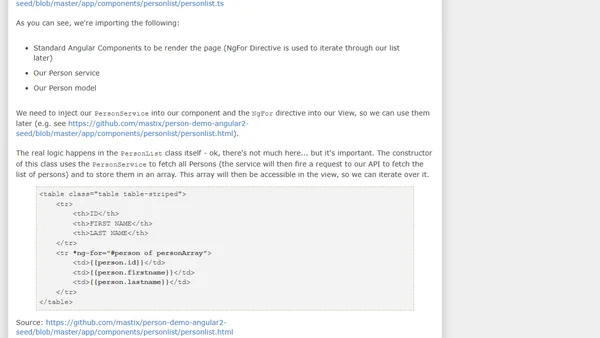
Part 9 of a Docker series: Creating a Docker container for an nginx web server hosting an Angular 2 frontend application.

The Bite Python Newsletter is now an official weekly publication, with a new schedule and homepage.
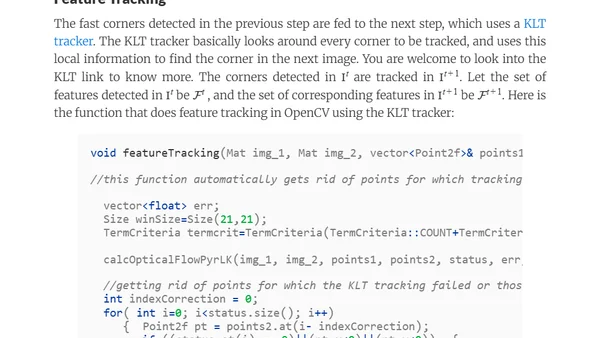
A technical guide to implementing Monocular Visual Odometry using OpenCV and C++, covering feature detection, motion estimation, and algorithm details.
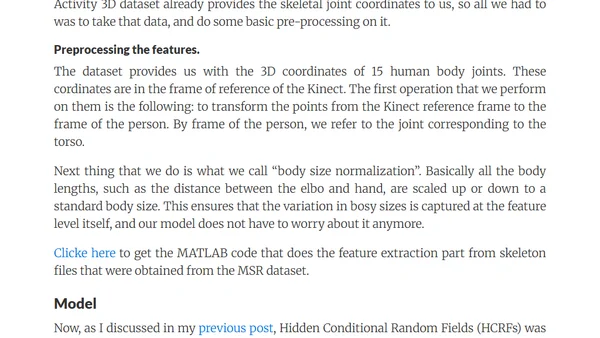
A technical walkthrough of implementing a human activity recognition system using Kinect's skeletal joint data and machine learning.
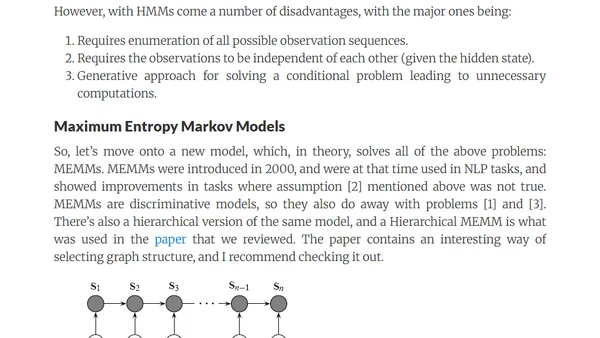
A guide to choosing temporal models like HMMs, MEMMs, and CRFs for sequence classification in a human activity recognition project using Kinect data.
A beginner-friendly tutorial on implementing Visual Odometry for robotics, focusing on a stereo vision approach based on a classic research paper.
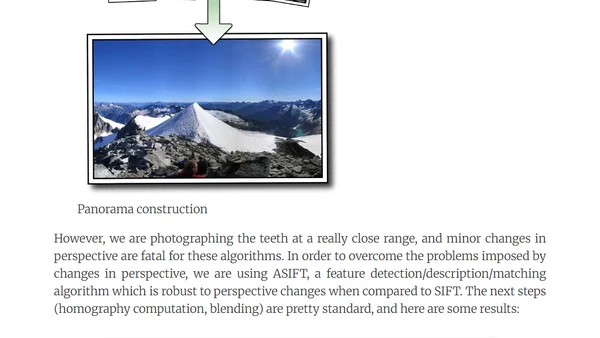
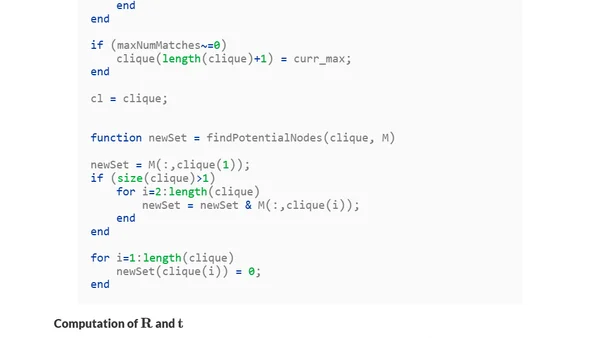
Explores using ASIFT algorithm to stitch close-range intra-oral dental images for a complete jaw view, overcoming perspective challenges.
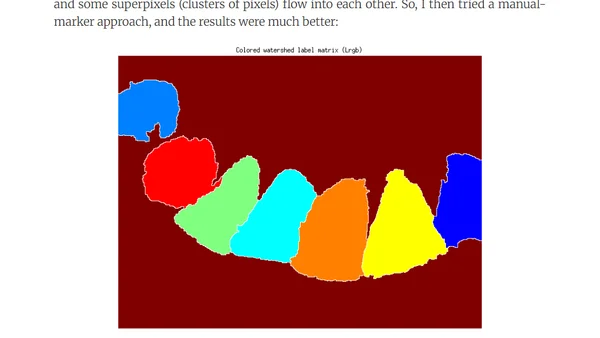
Explores algorithms for segmenting individual teeth from dental images, comparing Active Contours and Watershed transforms.
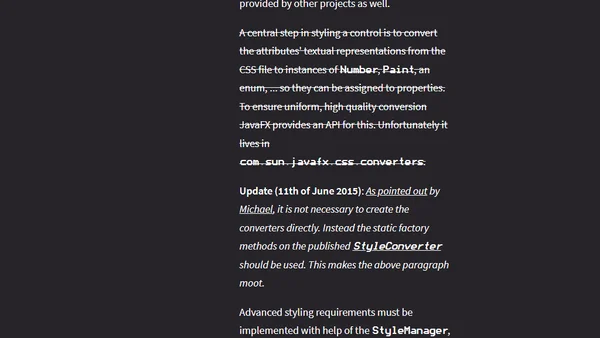
Explains how Java 9's Project Jigsaw impacts JavaFX development and how JEP 253 aims to provide public APIs for internal features.