Strengthening Resilience with Microsoft Sentinel and Security Copilot: Commvault Expands Microsoft Security Integration
Commvault expands Microsoft Security integration with Sentinel and Security Copilot for AI-driven threat detection and recovery.
Commvault expands Microsoft Security integration with Sentinel and Security Copilot for AI-driven threat detection and recovery.
A practical guide on integrating Generative AI into Security Operations (SOC), covering foundational LLMs, development tools, and automated agentic workflows.
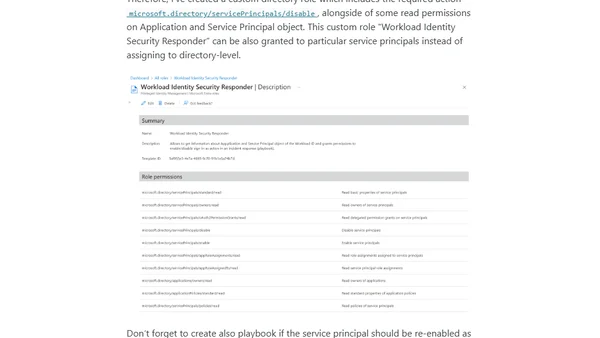
Explains how to use Microsoft Sentinel playbooks and Conditional Access to respond to security incidents involving compromised Microsoft Entra Workload Identities.
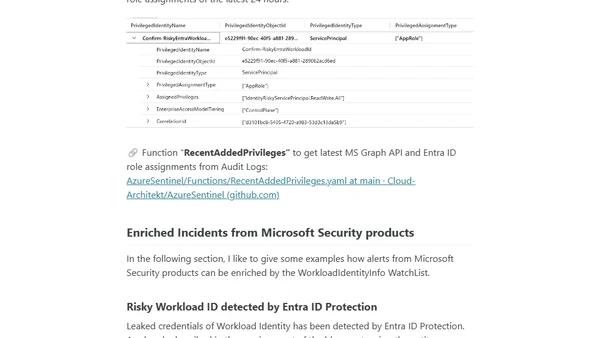
A guide on integrating Microsoft Entra Workload ID data into Microsoft Sentinel for advanced security monitoring and enrichment.
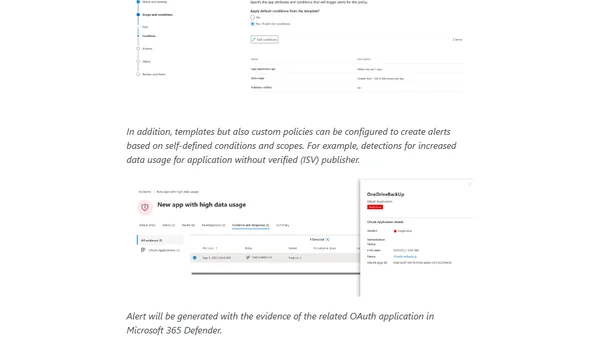
Explores threat detection for Microsoft Entra Workload IDs using Microsoft Defender XDR and Sentinel, focusing on attack paths and MITRE ATT&CK techniques.
A guide to getting started with Microsoft Sentinel, covering its SIEM/SOAR capabilities, cost structure, and initial setup for security monitoring.
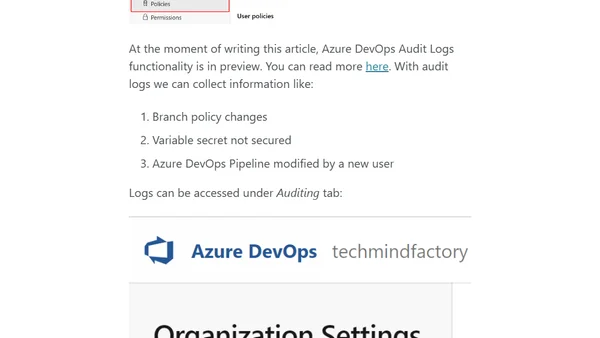
Final part of a DevSecOps series on using Microsoft Sentinel for security monitoring, threat detection, and incident response in Azure environments.
Explores security-focused open-source workbooks for Azure Monitor and Microsoft Sentinel, highlighting use cases and reviewing specific templates.
Explains how to analyze and audit Azure AD Conditional Access policies using Microsoft Sentinel and KQL queries for security insights.
A technical guide comparing agent options (Log Analytics, Azure Monitor, Defender for Identity) for monitoring Active Directory logs in Microsoft Sentinel.
Explains how to detect malware attacks using behavioral TTPs and kill chain analysis with Microsoft Defender and Sentinel, beyond just IOCs.