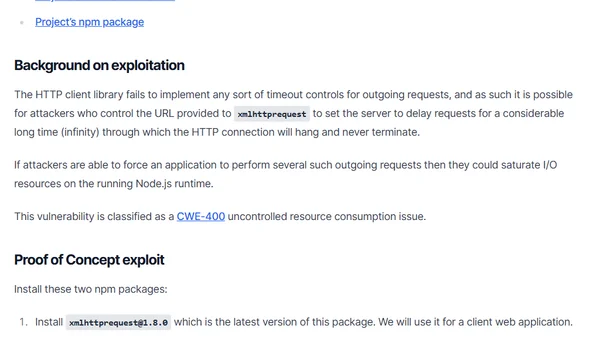
Disclosing uncontrolled resource consumption in xmlhttprequest library
Discloses a CWE-400 uncontrolled resource consumption vulnerability in the xmlhttprequest npm package due to missing timeout controls.
Liran Tal is an AI security researcher and Node.js security expert focusing on securing agentic AI workflows, MCP, and software supply chains through research, education, and open-source work.
213 articles from this blog
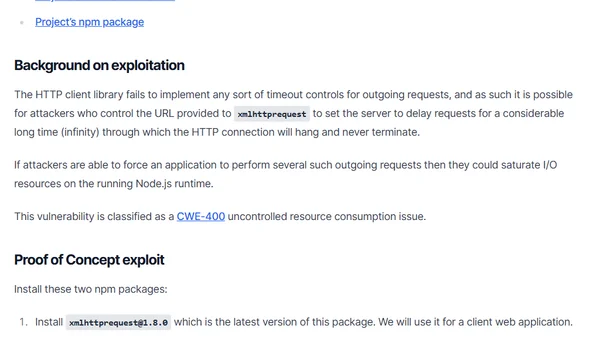
Discloses a CWE-400 uncontrolled resource consumption vulnerability in the xmlhttprequest npm package due to missing timeout controls.
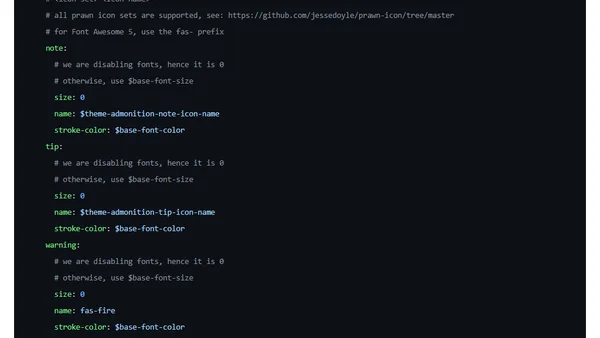
A technical guide on customizing the visual styles of admonitions (notes, warnings, etc.) in AsciiDoc documents, particularly for PDF output.
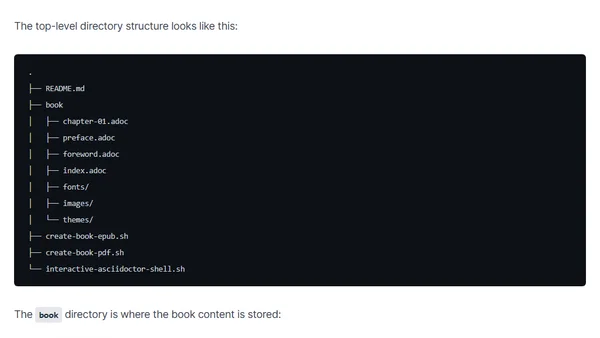
A guide to writing and publishing books using the AsciiDoc markup language and a starter GitHub template.
A developer shares their journey in open source, focusing on web security, Node.js contributions, and receiving the GitHub Stars 2023 award.

A developer shares their journey creating an open source activism program to teach collaboration and inclusivity in software development.
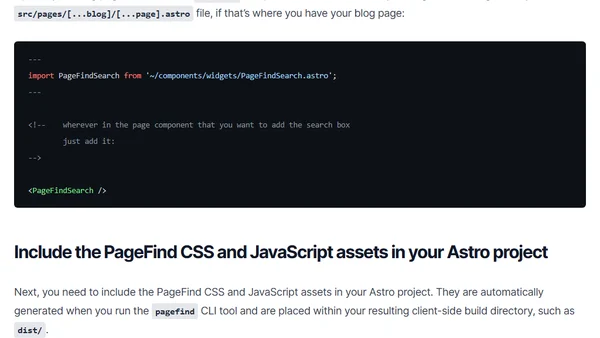
A tutorial on integrating PageFind, a client-side search tool, into an Astro static blog website.
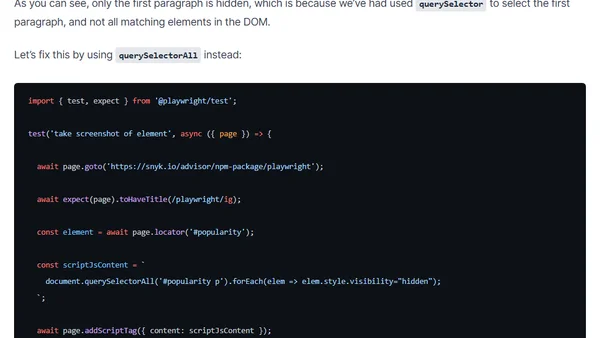
Advanced techniques for customizing element screenshots in Playwright, including DOM manipulation and image preprocessing.
A look at Warp, a modern terminal emulator with AI-assisted command suggestions and crowd-sourced workflow templates to boost command-line productivity.
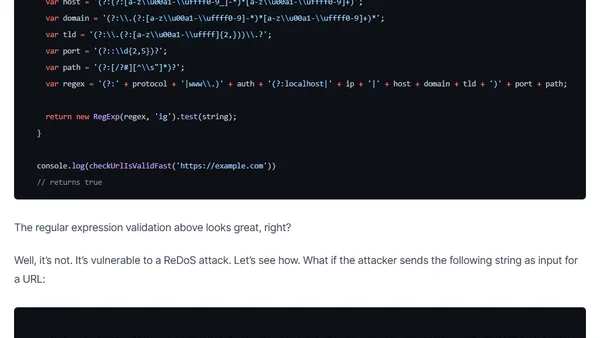
Explains why using RegEx for URL validation in JavaScript can introduce security vulnerabilities like ReDoS attacks, and recommends safer alternatives.
A guide to resources for finding tech conferences and submitting effective Call for Papers (CFP) proposals for public speaking.
A recipe of GitHub Actions CI workflows to automate documentation linting, dependency alerts, and PR management for open source maintainers.
Analyzes security risks from indirect dependencies in Angular and React boilerplate projects, comparing vulnerability counts and license issues.
A technical comparison of built-in security features and secure coding practices in React and Angular frameworks.
Analysis of widespread jQuery XSS vulnerabilities affecting 84% of websites, detailing version risks and vulnerable libraries.
Analysis of the 2019 State of Open Source Security Report, focusing on Node.js and npm vulnerabilities like Path Traversal and ReDoS.
A developer shares their experience attending JSConf Budapest, highlighting the talks, people, venue, and personal reflections on the event.
Essential npm security best practices to protect against malicious packages, including ignoring run-scripts and vetting third-party modules.
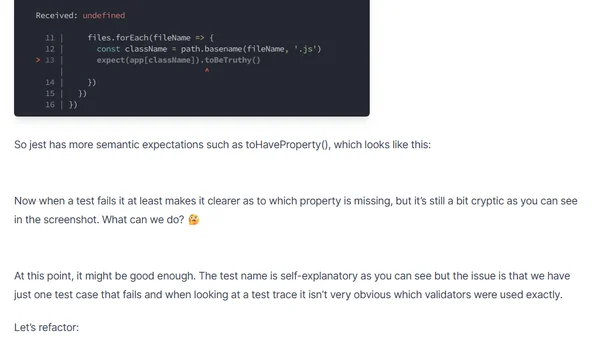
A guide to improving Jest test clarity by refactoring assertions and using custom error messages for better debugging.
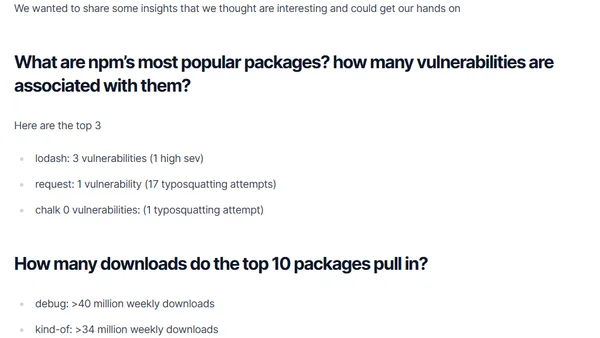
npm registry hits 1 million packages. Analysis of top packages, vulnerabilities, and download statistics.
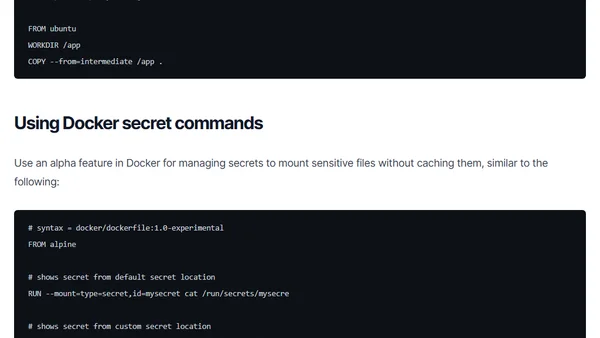
Learn how to prevent secrets like SSH keys and API tokens from being leaked into your final Docker images using multi-stage builds and secrets management.