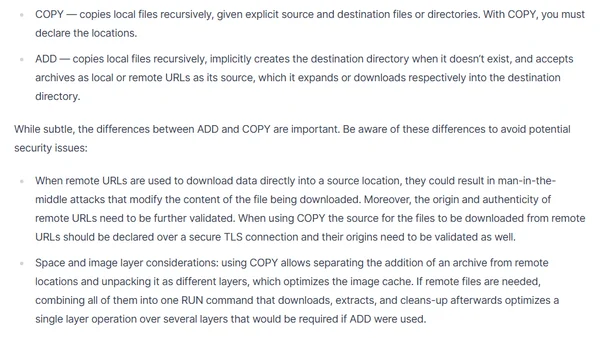
Why you should use COPY instead of ADD when building Docker images
Explains the security and performance differences between Docker's COPY and ADD commands, recommending COPY for safer image builds.
Liran Tal is an AI security researcher and Node.js security expert focusing on securing agentic AI workflows, MCP, and software supply chains through research, education, and open-source work.
213 articles from this blog
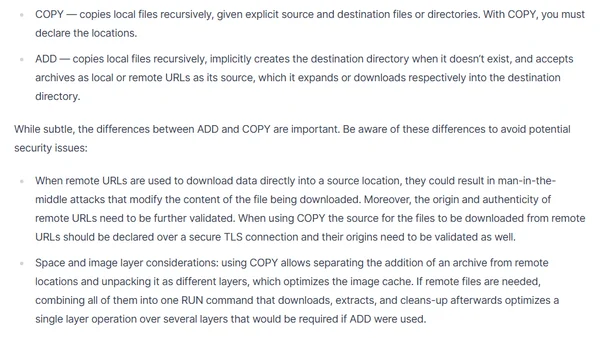
Explains the security and performance differences between Docker's COPY and ADD commands, recommending COPY for safer image builds.
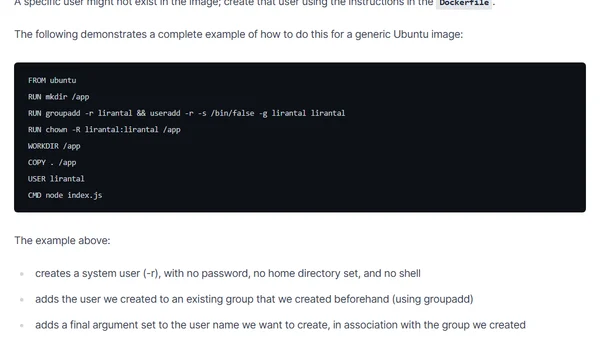
A guide on implementing Docker security best practices for Node.js, focusing on using non-root users to minimize attack surfaces.
Analysis of a malicious backdoor discovered in the popular bootstrap-sass Ruby gem, its impact, and essential security best practices for developers.
A guide to implementing Consumer-Driven Contract Testing with Pact to prevent API breakage in Service Oriented Architectures.
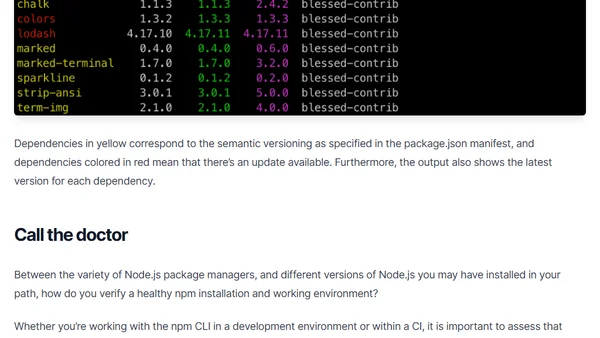
Learn how to use npm outdated and npm doctor commands to assess your project's dependency health and environment setup.
Explains the risks of inconsistent package lockfiles in npm/Yarn and how to enforce strict dependency installation using `npm ci` or `--frozen-lockfile`.
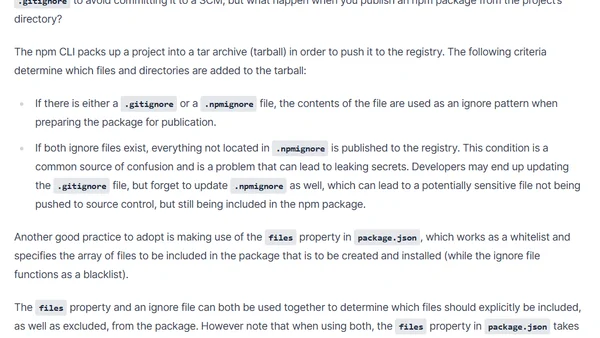
Explains how to prevent accidentally publishing secrets like API keys to the npm registry, covering .npmignore, package.json files, and dry-run.
Analysis of JSHeroes 2019 conference CFP data, revealing submission patterns and workshop details for the JavaScript event.
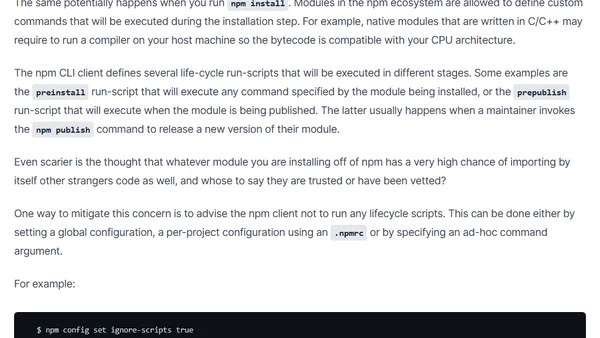
Analyzes security risks in npm package installation, highlighting the dangers of arbitrary code execution and advocating for cautious dependency management.
Highlights from the Node.js Security WG's January 2019 meeting, covering bounty programs and vulnerability database improvements.
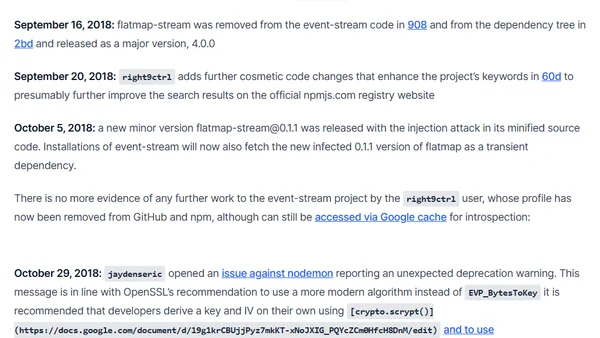
A detailed analysis of the malicious event-stream npm package backdoor, its timeline, and the social engineering attack that led to its inclusion.
Explains npm's evolving naming rules to combat typosquatting attacks, detailing case sensitivity and character restrictions for package names.
A guide to common pitfalls and best practices for testing asynchronous code using the Jest framework in JavaScript.
Explains security risks in the npm ecosystem, including malicious modules, typosquatting, and compromised contributors, with mitigation advice.
Key focus areas for hiring a VP of Engineering for a small, growing team, covering culture, automation, and team mentorship.
A developer's enthusiastic review of Jest's developer experience, highlighting its visual diffs, flexible conventions, and friendly CLI.
A developer shares key reasons to love the Jest testing framework, highlighting its zero-config setup, built-in features, and extensibility.
An introduction to the Node.js Security Working Group, its role in securing Node.js core and modules, and how to get involved.
Explains how flawed Regular Expressions can cause ReDoS attacks, crippling Node.js services with catastrophic backtracking and high CPU usage.
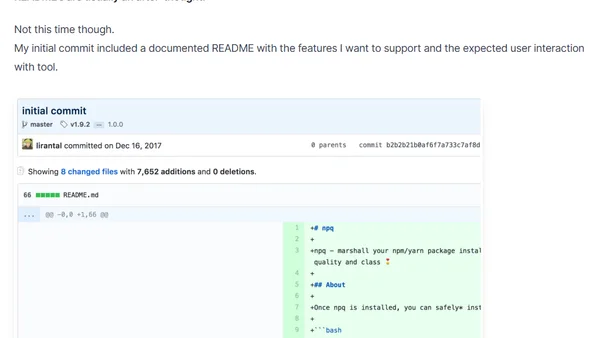
Introduces README Driven Development (RDD), a method for starting projects by writing a detailed README before code to define goals and features.