"Disregard that!" attacks
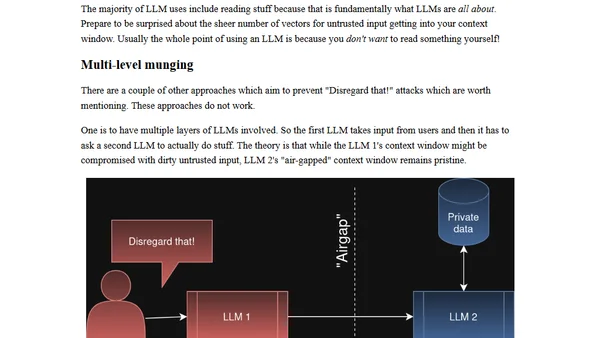
Read OriginalThis article discusses 'Disregard that!' attacks, a class of prompt injection vulnerabilities in large language models (LLMs). It explains how the context window (the full input to the model) can be manipulated by untrusted user input, leading to security risks like unauthorized actions or data exposure. Using examples such as a customer service chatbot, the author illustrates how attackers can override system instructions by inserting commands like 'DISREGARD THAT!' into the context. The article emphasizes the danger of sharing context windows with external sources (e.g., web search results) and highlights the need for robust input sanitization and isolation in LLM applications. It is relevant to IT/technology as it covers AI security, prompt engineering, and software vulnerabilities.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser
Top of the Week
No top articles yet