Detecting and Analysing SSH Attacks with ksqlDB
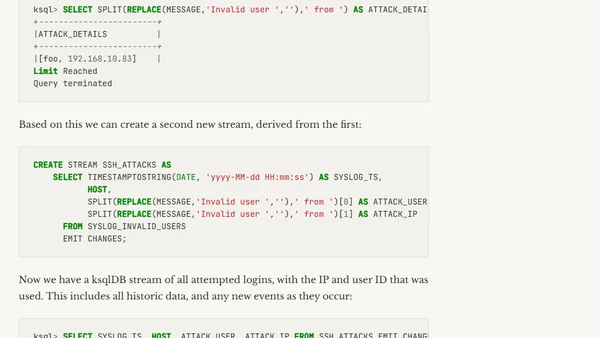
Read OriginalThis article provides a detailed tutorial on setting up a Syslog ingestion pipeline using Kafka Connect and ksqlDB. It covers creating a Syslog source connector, testing the data flow, and configuring devices to send logs. The focus is on using these streaming data tools for security analysis, specifically for detecting and investigating SSH attacks.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser
Top of the Week
No top articles yet