1% of CMS-Powered Sites Expose Their Database Passwords
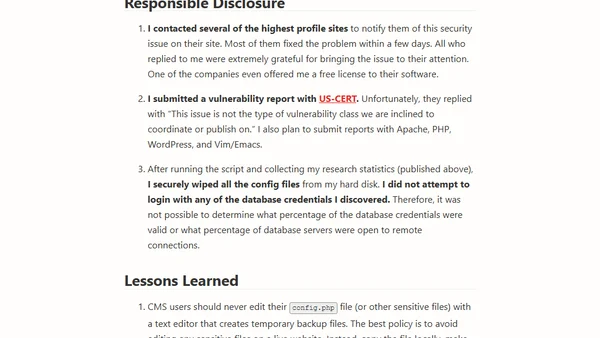
Read OriginalA security vulnerability in CMS-powered sites (like WordPress, Joomla) exposes database passwords when text editors like Vim or Emacs create backup files (e.g., wp-config.php~). These files are served in plaintext by web servers, allowing unauthorized access. The article details the CMSploit tool used to scan sites, finding 0.77% of CMS sites vulnerable, and explains the technical cause and implications.
Comments
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser
Top of the Week
No top articles yet