Advent Calendar 2025 – Basic Login Solution – Part 1
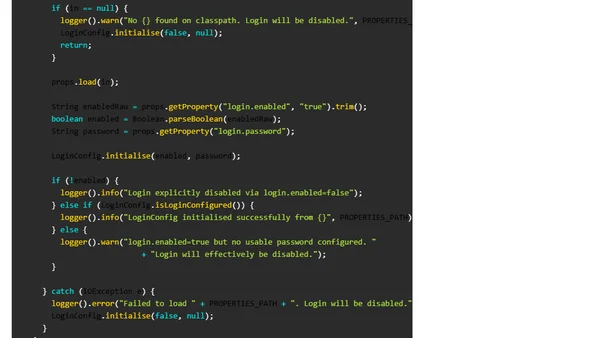
A tutorial on implementing a simple, configurable login mechanism for a URL shortener's admin interface, focusing on security without external dependencies.
A tutorial on implementing a simple, configurable login mechanism for a URL shortener's admin interface, focusing on security without external dependencies.
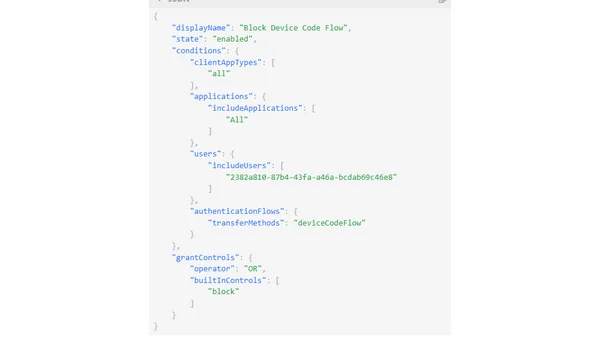
Explains the security risks of Microsoft's Device Code Flow and how to protect against phishing using Conditional Access policies.
Erläutert drei wichtige Gründe für die Migration einer Website von Joomla! 3.x auf die neuere Version 4.x, darunter Support-Ende, Sicherheit und Benutzerfreundlichkeit.

An overview of SQL Server 2016 sessions submitted for major conferences, focusing on Security, Performance, and In-Memory technologies.

A SQL Server expert's 2015 conference speaking engagements covering Extended Events, In-Memory OLTP, security, and Azure deployments.

Author explains why they don't publicly share SQL Server hacking demo scripts, focusing on security awareness over providing attack tools.

A technical session exploring various SQL Server attack scenarios, including SQL injection, privilege escalation, and DoS attacks, focusing on misconfigurations and security weaknesses.

Andreas Wolter presents two technical sessions at SQLCon 2011 on SQL Server security for developers and centralized Reporting Services design.