Protect your users from Device Code Flow abuse
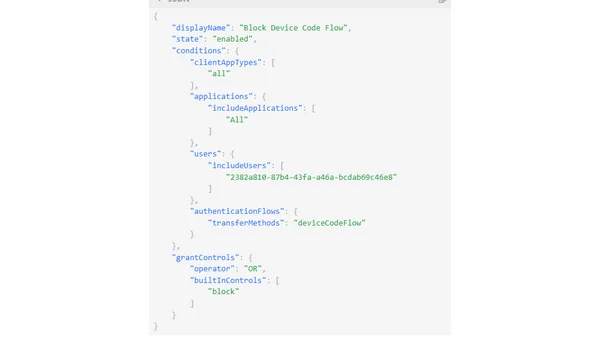
Read OriginalThis technical article details the security vulnerabilities in Microsoft's Device Code Flow authentication method, specifically phishing attacks like TokenTactics. It explains how attackers can abuse the flow and provides a solution using Microsoft Entra Conditional Access policies, including the new 'Authentication Flows' condition, to restrict or block Device Code Flow usage and enforce device compliance.
Kommentare
No comments yet
Be the first to share your thoughts!
Browser Extension
Get instant access to AllDevBlogs from your browser
Top of the Week
No top articles yet