John D. Cook
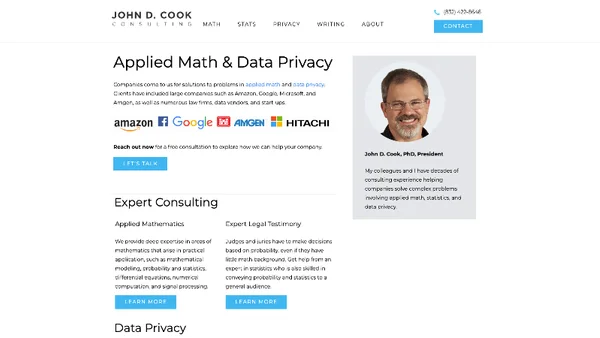
John D. Cook provides expert consulting in applied mathematics and data privacy, helping clients from tech, biotech, and legal industries—including Amazon, Google, Microsoft, and Amgen—solve complex problems efficiently.
applied mathematics
data privacy
consulting
software solutions
biotech
Articles from this Blog
0 articles from this blog
No articles found
No articles are currently available from this blog.